If you’re feeling chatty, you can always access a chat room. I recommend using a stick since DVDs have a read-only function after you’re done burning well and accessing the dark web required a bit of writing. It knows you’re accessing Tor but can’t see beyond that. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable.
DuckDuckGo (on Tor)
Learn how to turn threats hidden in the dark web into actionable threat intelligence. Make Tech Easier provides tech tutorials, reviews, tips and tricks to help you navigate the complicated world of technology. Our latest tutorials delivered straight to your inbox It will display a message, Onion available, if onions are available for the website.
Improving The Web: Building A Smarter, Safer, And Faster Internet
Keep in mind what you’re looking for, find that information, and disconnect from the dark web. Check around with other users and ask if they know anything about the new marketplace. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep.
What Is The Safest Way To Download Tor Browser?
Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s. However, the vast majority of items found on dark web marketplaces are illegal or illicit. Books, video games, apparel and rare collectibles are some of the legal items you can buy on dark web commerce sites. If you’re in a restrictive country, you’ll be crossing the red line and authorities could be at your heels. A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense. There’s evidence that law enforcement agencies in freer countries operate many exit nodes for monitoring and surveillance purposes.
Minimize Or Rescale Your Tor Browsing Window
This helps protect your personal information and adds an extra layer of anonymity. This will provide an additional layer of defense against malware and other malicious activities. This software encrypts your internet traffic and allows you to navigate anonymously. Remember, researching the Dark Web requires caution, diligence, and adherence to legal and ethical standards. This will add an extra layer of security and prevent potential attacks on your system.
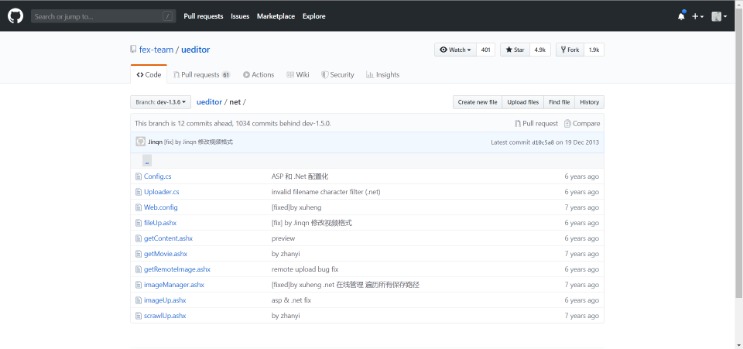
The current repository has over 22,000 journals with over 10 million articles across all subjects. The amount of content on USA.gov is seriously impressive. If you pair the regular DuckDuckGo engine with the Onion version, you can perform an entire web search.
This gives anonymity to .onion website owners and visitors. Even if you’re only attempting to visit legitimate sites, one wrong click could expose you to content you would rather not see. There are numerous phishing sites, too, as explained earlier, designed to fool users into giving up their personal data. However, remember to be cautious when accessing this hidden part of the internet. As such, it’s important to be extremely careful when accessing the dark web, as you could inadvertently access a site containing, displaying, or linking to illicit content in some form.
These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. As always, protect yourself from online threats with mobile Android security or iOS security software. Before accessing the dark web, install strong security software to help keep your device protected. Tor is a web browser that lets you stay anonymous online or access the dark web.
- Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions.
- They do this to ensure that people all over the world can access their service, even if the government decides to pull the plug.
- When cybercriminals leak stolen sensitive data, it almost always ends up on the Dark Web, as this part of the internet grants users anonymity and privacy from IP address-tracking.
- If you live in a country where certain news sites are restricted, you might also benefit from staying up-to-date with ProPublica.
- Unlike other search engines, it does not collect or share web activities and personal data of users.
As a result, you cannot find them with a regular search engine. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. It is easily accessible by the general public and requires no special configuration.
If you’re hiding from your government, they’ll perceive the dark web as a threat. Never click on dark web links unless you know exactly what they are. Cybercriminals often use the dark web to access and learn about malware. If you really must buy something, research how to do it safely using cryptocurrency.
How To Safely Access The Dark Web
Reputable organizations, security researchers, and privacy advocates provide a wealth of insights, tutorials, and software to help you explore safely and responsibly. While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance. Stay vigilant, trust your instincts, verify sources, and prioritize your security to make the most of the anonymity these networks provide. Now that you understand the essentials of anonymous networks and how to prepare yourself for secure browsing, it’s time to explore the practical steps involved in accessing the Dark Web. By familiarizing yourself with these networks and protocols, you gain a clearer understanding of the diverse strategies people use to stay hidden online.
Should You Use A VPN And Tor?
For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. If you want to observe the lawless sides of the internet from afar, check out YouTube videos of dark web explorations, like this one from John Hammond, to satisfy your curiosity. I don’t recommend seeking out dark web content unless you have a specific reason to do so. Remember to update the Tor Browser regularly to ensure you have the latest security patches, and scan your computer for malware regularly using antivirus software.
Accessing The Dark Web
You’ll find links to many of the sites we’ve covered in this list. Powered by the same data as Have I Been Pwned, Firefox Monitor sends alerts if your info appears in a new breach. Many tools help users check if their data is on the dark web. Take control of your online security and protect your identity with these helpful tips. Learn how to monitor, get alerts, and stay safe online with easy steps. Engaging in illegal activities is strictly discouraged and can have serious legal consequences.
The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. This way, you can protect yourself from websites that want to steal your login details or cryptocurrency. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Other options include Ahmia and NotEvil, which focus on listing .onion links. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results.
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
Some countries frown upon dark web usage, so it’s good to cover your back with a reputable VPN service. It encrypts your traffic right away, beneficial if you don’t want your ISP to see that you’re using Tor. A VPN is a confusing factor for many because there are two ways to use it with Tor. Either way, some sites take up to a minute or more to load, so don’t fret.
When accessing the dark web, the first step is to install a dark web-friendly browser on your computer. Less commonly, activists and dissidents may use these channels to exchange information, recruit, and plan activities. Another difference you’ll notice is that instead of seeing web addresses with a “.com,” “.org,” “.edu,” or “.gov” suffix, they’ll end in “.onion.” It’s estimated that the surface web makes up about 5%–10% of the internet, while the deep web comprises as much as 90%–95%. Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats. Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe.
Ultimately, the Dark Web is neither purely nefarious nor inherently virtuous—it’s a dynamic environment shaped by the motivations and actions of its users. While the Dark Web remains a core venue for privacy-seeking users and covert activities, a range of emerging platforms and shifting trends shape the broader ecosystem of underground communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes. Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. This “onion” routing masks your IP address and encrypts your data multiple times, peeling away layers of encryption at each relay. Understanding the differences and capabilities of various anonymity tools will help you make informed decisions about which networks best serve your needs.