It allows users to stay safe from ISPs, governments, surveillance agencies, and hackers monitoring their activities, and is the perfect option to access the dark web. Regardless of your jurisdiction, activities such as trading stolen financial data, compromised accounts, or money laundering services are illegal. Governments make significant efforts to shut down darknet marketplaces due to concerns about illegal activities, including drug trafficking, weapons sales, and cybercrime.
Step-by-Step Guide: How To Access The Dark Web Using Tor Browser
The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. The core principle of the Tor network was first developed by U.S. Those who access the dark web do so via the Tor (The Onion Router) browser. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The users of the dark web are typically aiming to block governments from snooping on them.
Should I Only Use A VPN To Access The Dark Web?
Darren is regularly featured as a cyber-security expert in major media outlets including CBS Evening News, Fox & Friends, USA Today, ABC and Mashable. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. There are several whistleblower sites, including a dark web version of Wikileaks. You can conduct discussions about current events anonymously on Intel Exchange.
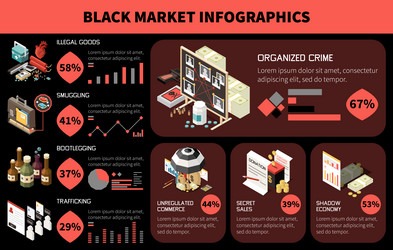
Organized crime groups are heavily involved in the black market for firearms, using their networks to acquire, transport, and distribute weapons. The presence of black market firearms also undermines the rule of law and creates a climate of fear and insecurity. Such modifications are illegal and contribute to the proliferation of dangerous weapons on the black market. Straw purchasers often receive compensation for their services, making it a lucrative, albeit illegal, activity.
Use Cryptocurrency For Transactions

They often use the profits from gun trafficking to fund other criminal activities, such as drug trafficking and human trafficking. The dark web and encrypted messaging apps allow buyers and sellers to communicate anonymously and conduct transactions without fear of detection. Handguns, particularly semi-automatic pistols, are the most commonly found firearms on the black market due to their concealability and relative ease of acquisition. Combating the black market for firearms requires a multi-faceted approach.
As a reminder, most of the purchases described here are illegal and/or dangerous. When shipments come from within the US, the illegal goods are likely to arrive at the right mailbox without incident. Anyone who executes these purchases via anonymous bitcoins will leave no trace of the transaction. The level of protection provided by Tor makes law enforcement’s job tracking such activities next to impossible. We have touched on Tor two or three times to protect your identity while online, but Tor includes other functions.
- There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data.
- The homepage includes options like browsing products, searching, mixer, and coin exchange.
- While it’s true that some corners harbor illegal activities, it also provides a platform for whistleblowers, journalists, activists, and everyday users seeking privacy and freedom from censorship.
- It is difficult to say exactly what can be found on the black market, as it is an illegal and unregulated market.
- The marketplace has a pleasant, user-friendly interface built from the ground up.
Is The Dark Web Illegal?
We recommend using NordVPN as it offers top-notch security features, including dark web threat protection. The layers of encryption hide your data and activity from snooping eyes. Your information might be on the dark web if your data was part of a data breach or hack. The Silk Road was illegal because it was primarily a hub for the sale and distribution of illegal items and facilitated other unlawful activity.
Are The Products On The Black Market Safe To Use?
The dark net has also been used for sharing illegal pornography and purchasing hacked accounts or software that can be used to break into someone’s bank account. Below, you can find our recommended dark web tools for exploring this part of the internet. Accessing the black market can be a daunting task, especially for those who are unfamiliar with its inner workings. That way, you can change your passwords and protect your accounts before anyone can use your data against you.
Which Darknet Markets Are Still Open
These pages come with extra protections for user anonymity and data security, and you need special software to access them—you can’t get at them through your normal web browser, like you can with much of the rest of the deep web. A darknet market (also known as a darknet shop or dark web shop) is an online marketplace operating on the dark web, accessible only through specialized software like the Tor browser. In the digital age, darknet markets have emerged as sophisticated platforms facilitating anonymous transactions using cryptocurrency and Tor network encryption. This platform provides in-depth analysis, security guides, and educational materials about digital privacy, anonymous browsing, and darknet marketplaces. Welcome to the Black Market Encyclopedia, your comprehensive educational resource for understanding darknet markets, black market online stores, and the broader dark web ecosystem. 👉 Note – To enhance your security and maintain anonymity when accessing the black market, it is highly recommended to utilize a NordVPN.
How To Access & Get On The Black Market (Instant Safe Tips)
But there are also many illegal activities that happen on the dark web. The dark web limits online tracking, and there are many legitimate reasons people like journalists and activists use the dark web to remain private. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. Lastly, The Hidden Wiki is a collection of dark web links — but the links may not work and can lead to dangerous websites. The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet. As always, protect yourself from online threats with mobile Android security or iOS security software.

That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. While some studies have claimed that illegal Bitcoin activity is as high as 44%. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Last but not least, we here at Pixel Privacy never condone illegal activity. If you decide to enter the dark web, always make sure to take all the necessary online privacy precautions.
Think of it as the internet’s wild card. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. But even though it seems like there’s a lot out there, this only makes up about 4% of the entire internet.

- By encrypting communication before it gets to the Tor network, pairing Tor with a VPN gives a second degree of protection.
- As in the real world, the price you pay for stolen data fluctuates as the market changes.
- In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network.
- For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users.
- Most dark web marketplaces use cryptocurrencies like Bitcoin for transactions to help maintain anonymity.
- After all, they need to maintain their service somehow, and selling user data to third parties is the route many of them follow.
I2P cannot be used to access .onion sites because it is a completely separate network from Tor. It can only be used to access hidden services specific to the I2P network. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. Specialized search engines, directories, and wikis can help users locate the data they’re looking for. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. Obviously not all Tor users, but you never know whether someone might be looking into you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. It’s especially important to take your privacy seriously if, strictly out of curiosity, you want to browse the market places on the dark web.