Knowing where online materials are – and who is searching for them – makes it possible for search engines like Google to sell advertisements. This accounts for well over 80 percent of the company’s revenue, linking people who are searching with the millions of sites out there that pay Google to list their content. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals.

Separate Your Real Life From Your Online Persona
If the Tor browser is running, you can immediately check whether it is working as intended. To do this, go to the website whatismyipaddress.com, for example. Since these have been used several times for criminal offences and rampages and the media have reported on them, the darknet has increasingly become the focus of public attention.
How Many Dark Web Sites Are There?

I2P must be downloaded and installed, after which configuration is done through the router console. Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser. Due to all the nodes that your traffic passes through, Tor by itself significantly limits bandwidth.
Use A VPN Or Proxy For An Extra Layer Of Security
We are committed to ensuring that our website is accessible to everyone. If you have any questions or suggestions regarding the accessibility of this site, please contact us. By embedding these standards into their security framework, organizations can minimize their exposure, fortify their defences and stay one step ahead of cybercriminals. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. You might be used to typing in a word or phrase on the surface web, hitting “Enter,” and receiving pages of results. You must type in a valid web address instead of “surfing the web” to find what you want.
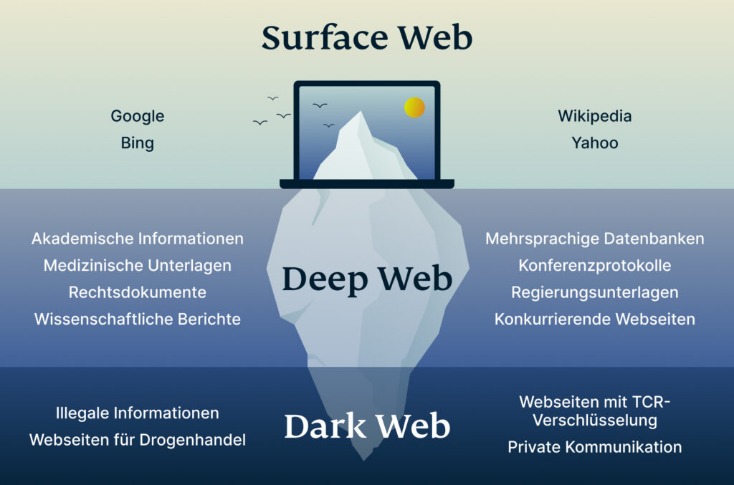
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself.
Major Risks And Downsides
With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims. Such people can be opposition figures from dictatorship-led countries, politically oppressed individuals, whistleblowers, or journalists. The internet is an extensive network of millions of servers, databases, and web pages that run continuously. The editorial team did not participate in the creation of this guide.
- Then, they can use your data to impersonate you and run social engineering attacks to target your loved ones.
- In addition, even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up.
- It uses its own internal DNS to access “eepsites”, not .onion addresses.
- Antivirus will ensure that any viruses or malware downloaded from the dark web are removed.
- By following this dark web access guide, applying Tor browser safety practices, and knowing when it’s safe to browse the dark web, you can navigate responsibly without compromising your security.
Not to mention its Advanced Protection that blocks malicious sites, trackers, and ads. This is accompanied by the Network Lock kill switch that also prevents IP leaks. This allows you to go online anonymously and without ISP monitoring.
Encrypted Communication Tools
Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity.
How To Access The Dark Web On An IPhone
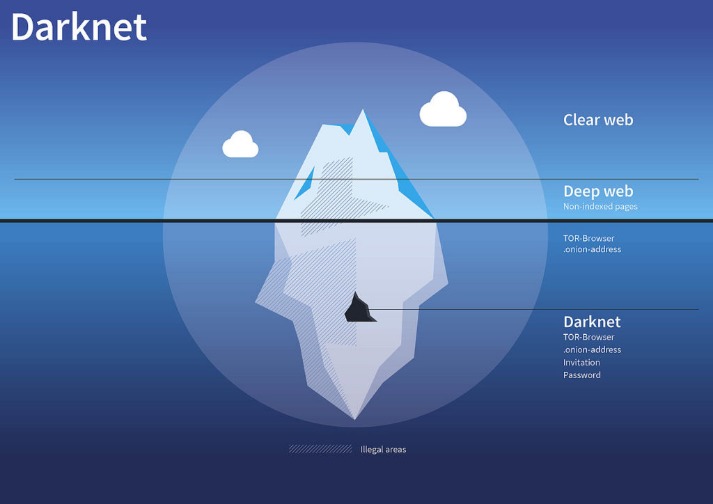
The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
However, bear in mind that they are often less user-friendly than Tor (which makes accessing the dark web easy). The deep web refers to any part of the internet that is not openly indexed and made available via a web search. This includes any private information held on the cloud that is not listed on the Web. This includes things like the data stored on private cloud servers, backup services, email accounts, etc. Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes.
This is usually done to prevent tracking and website shutdowns typical for this part of the internet. The trick with these onion websites is their accessibility, which is made possible only with Tor. Tor is an abbreviation for The Onion Router and now, we can see why. It’s not easy to find what you’re looking for on the dark web, especially if you want to do it safely.
Cybercriminal groups like DDOS have carried out over 140 cyberattacks on companies since Bitcoin’s emergence in 2014. The attacks have led to the formation of other cybercriminal groups and Cyber Extortion. According to recent research, Bitcoin tumblers are increasingly used for money laundering. In another example, Playpen, the largest child pornography site in 2015 on the dark net with a membership of more than 200,000, was taken down by the FBI.
Is It Illegal To Visit Dark Websites?
The dark web isn’t only about illegal activities; its primary purpose is to provide maximum anonymity by making your connection private online through encrypted servers. While the dark web is famously known as an illegal platform for criminal activities, that’s not all about this part of the web. The darknet is a private place where nobody can intercept, monitor, or steal anything online from you. If you want to be extra safe, routing your connection through a VPN and then accessing the dark web using the Tor browser provides more security than Tor alone. You can also use the Tails operating system to further protect yourself. If you’re just browsing the dark web out of curiosity, Tor, or a Tor and VPN configuration is safe enough.


