We also prefer this method because of VPN’s all-encompassing security. Plus, the ISP won’t see that you’re using Tor. For one, the VPN can’t see your online activities because of VPN encryption. When you go on the dark web and visit the site, your traffic is decrypted, and everything functions the same.
Step-by-Step Guide: Access The Dark Web On Any Device
The dark web is hard to stop because it’s difficult to track and monitor activity since much of it is encrypted. The dark web is packed with potentially harmful content that puts you at risk, so a VPN is an important tool in keeping your identity and personal information safe. Yes, we recommend that you always use a VPN if you’re accessing the dark web on your phone.
Check Tor Network Status
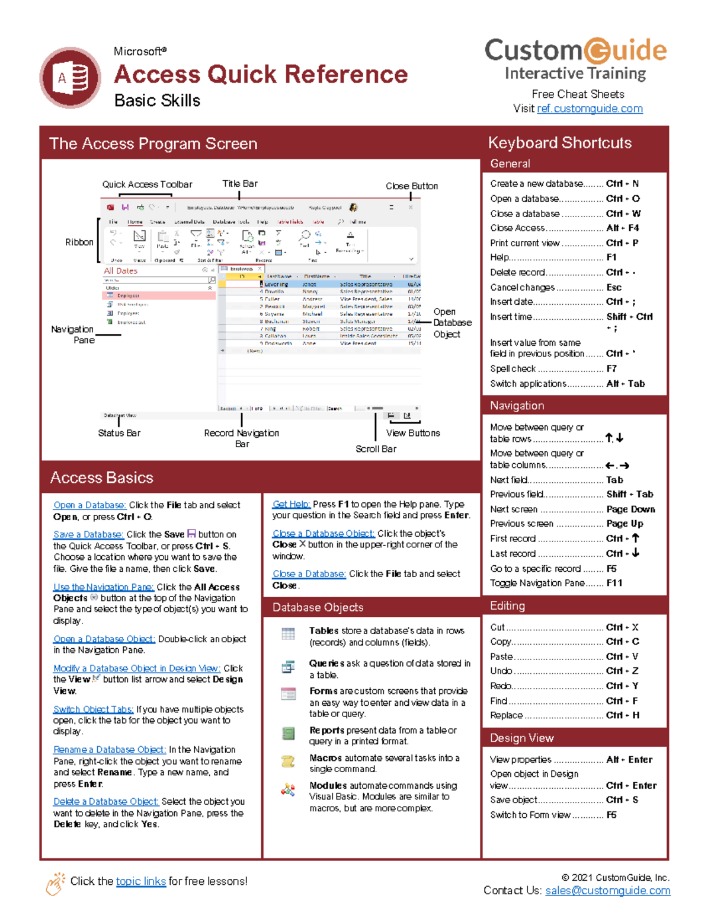
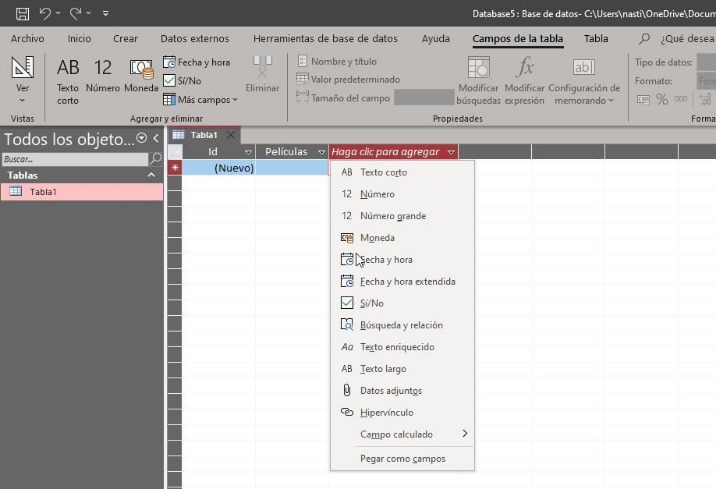
So there’s no sense in using the Tor Browser if you’re just going to give away your data again. The settings are accessed by clicking the shield button next to the address bar and choosing Advanced Security Settings. Configure is for people who are using a proxy to access the internet. This allows people in oppressive states to access undoctored news securely.
Do’s And Don’ts For Tor Browser
Take a look at your Tor Browser settings before you start your first dark web browsing session. There are a lot of these sites across the dark web, which is why you have to be extra careful. Often, these sites are made to look just like real, trusted platforms, such as banks, social media sites, or email providers. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors. It offers some protection, but you still have to be wary and sensible when browsing the dark web.
How To Access The onion Domain?
Without a VPN, your ISP or network administrator may be able to detect, monitor, or block dark web access; Tor-over-VPN provides an extra layer of privacy. The dark web is a murky part of the internet that isn’t accessible via a normal browser — and can be dangerous to visit if you don’t know what you’re doing. This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing).
Dark Web Websites
The features make NordVPN viable for accessing the dark web as your IP address can’t find out that you are using Tor. The deep web search engines communicate to the service through Tor and resolve the .onion links thereby delivering their output to your surface web browser. However, there are specialized deep web search engines that crawl over the Tor network successfully and bring results to your regular browser. As we explained, Google and other powerful search engines can’t crawl and index the data on the Dark Web. In darknet mode, Freenet will allow you to connect and share content with only your friends on the network. Freenet enables users to connect to the dark web and only uses content uploaded to the Freenet.
Adjusting Security Slider Levels
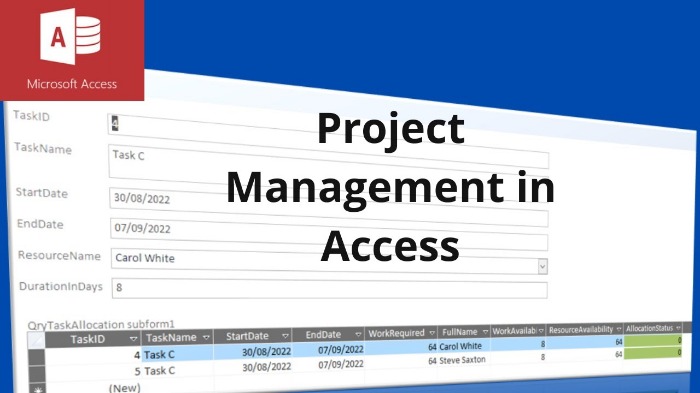
Once you are connected to the TOR network, you can start browsing the dark web by entering .onion URLs into the address bar of the TOR browser. The dark web is accessed through a network of encrypted servers that bounce internet traffic around the world to obscure a user’s location and identity. In this tutorial, we will guide you through the process of accessing the dark web using the TOR browser, an encrypted browser that allows users to browse the internet anonymously. While disabling JavaScript might break the functionality of some websites, the enhanced security it provides is generally considered essential for navigating the potentially hostile environment of the dark web. Disabling JavaScript, especially on non-HTTPS sites (in “Safer” mode) or entirely (in “Safest” mode), is a widely recommended security practice when browsing the dark web.
More Security Articles
However, there are plenty of legal and legitimate online activities that require privacy and anonymity. Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight.
- Learn moreWizcase was established in 2018 as an independent site reviewing VPN services and covering privacy-related stories.
- Tor is not the same as a VPN, though both tools provide encryption and reroute your web traffic to another network.
- Tor doesn’t support plugins because they introduce security risks.
- It’s illegal to use the dark web for any form of criminal activity, like buying stolen goods, drugs, user accounts, and so on.
- It disables JavaScript and other potentially risky web features for maximum security.
You typically can’t access them from everyday browsers like Chrome, Edge, or Safari. Other people use these networks and social circles to whistle-blow against huge entities. People use Tor-like programs in countries where censorship is rampant. Many people turn to it to sell illegal substances and services, or even to post very disturbing imagery. But it’s also good to keep in mind that it’s hard — perhaps even impossible — to be completely anonymous online.
It routes traffic through service nodes operated by stakers in the network, creating a decentralized onion routing system that hides your IP and traffic. Unlike Tor, I2P is designed for peer-to-peer services like file sharing, email, forums, and even decentralized websites — all within its own closed network. Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation.
- But be warned, it’s not as user-friendly as the typical clearnet websites you access.
- So you can not only use Tor to access the dark web, but you’ll be encrypted as well.
- If a website you are visiting on the Tor browser has an onion site, you will see a purple button called (.onion available) at the right corner of the URL bar.
- Connection speeds are very fast, and you should be able to stream HD and 4K content without buffering.
- Each volunteer runs a node or a router called ‘relay’ and the Tor network is made up of more than six thousand relays.
And, of course, people, websites and third-party trackers will know who you are if you choose to identify yourself online. “All of your traffic goes through it, and you have to trust them as if they are your new ISP. Because the backbone of our software is a decentralised network, you don’t have to trust us to browse the internet privately.” “And if I use Tor then I have a good degree of certainty that at least the local weirdos are not looking over my digital shoulder at what I am browsing — and that when I kill my browser (unless I’ve bookmarked something, or saved a file) then all the data is properly cleaned-up and wiped.” “If the site invests in setting up a ‘native’ Tor onion-address for their website, then people who use the Tor browser to access that address never step outside the protection of the Tor cloud,” Muffett says.
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Last but not least, we here at Pixel Privacy never condone illegal activity. If you decide to enter the dark web, always make sure to take all the necessary online privacy precautions. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. Simply accessing the dark web and using the Tor browser may already raise government suspicion. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.