Joint operations and information sharing between agencies such as Interpol and Europol have led to significant successes in shutting down major darknet platforms. It’s crucial to stay informed about these risks and adhere to proper protocols to protect yourself and others from falling victim to these illicit activities. Contrary to popular belief, Bitcoin and other cryptocurrencies are not the holy grail of untraceable transactions on the darknet. However, it’s important to remember that engaging in illegal activities can have serious consequences. The dark web offers a variety of marketplaces that cater to different needs and preferences. When it comes to finding alternative platforms in the dark web marketplaces, there is no shortage of choices.
The Need For A Balanced Approach To Bitcoin And The Darknet MarketsOriginal Blog
These hidden corners of the internet have become hotspots for the online drug trade, providing access to a wide range of illicit substances that are just a few clicks away. These underground online marketplaces have become breeding grounds for cybercrime, posing a significant threat to society as we know it. Darknet markets continue to be a significant concern for law enforcement and society due to their association with cybercrime. To access these sites, users typically require special software, such as Tor, which ensures anonymity.
Enhance Your Threat Intelligence
The dark web is composed of specially encrypted parts of the deep web, and it’s used by cybercriminals, as well as everyday people, who want to communicate and trade in secret. Another advantage of traditional markets is the ability to bargain and negotiate prices with vendors. One could find any number of panic-inducing items on the shelves of these digital marketplaces. These fraudsters congregate on forums where they buy and sell stolen data and swap tricks of the (financial crime) trade.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. If you’re looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. In a way, these investigations have made law enforcement more collaborative and tech savvy than ever before. However, the flip side is that criminals also adapt using better encryption, shifting to new platforms, or operating from jurisdictions where they feel safe. Law enforcement has adapted, and many dark web perpetrators are being brought to justice. For the public and businesses, these developments are a reminder that the dark web isn’t some mythical safe zone for criminals.
What Is Cyber Threat Intelligence?
Once the buyer has initiated the purchase, the respective cost of the purchase in Bitcoins from the buyer’s account are held in the darknet market’s escrow until the order has been completed. The dark web is a part of the internet that is not indexed by search engines and is accessible only through special software, such as the Tor network. “In some cases, users will sell access information to organizations in what are called IABs (initial access brokers). Cybercriminals often steal this information through phishing attacks, data breaches, and other forms of cybercrime. Try our Dark Web monitoring tool for free to safeguard your business data against scammers. Continuous efforts are necessary to combat the risks and illegal activities prevalent in these hidden corners of the internet.
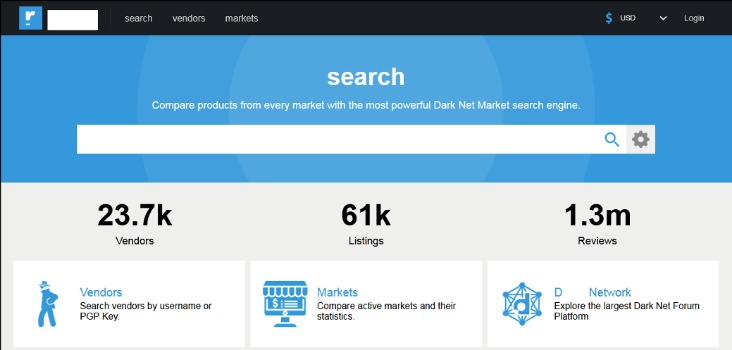
Given the events in the English-speaking sphere of TOR during the last 18 months, current instability among DNMs and uncertainty among darknet users, it could be an opportune time for a new player to take the stage. The invention of cryptocurrency helped the dark web flourish, because it added a new layer of anonymity to transactions. Cybercriminals can easily purchase and sell illegal drugs on these platforms, often using encrypted communications and anonymous shipping methods to evade detection.
Over the years, dozens of large DNMs have been established and eventually shut down by law enforcement, including AlphaBay, Dream Market, Wall Street, and, most recently, Hydra. Ulbricht was eventually arrested by US law enforcement and Silk Road was seized and taken offline. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs.
Investigators know this, so they actively scour for any link between an online alias and a real identity. Cazes also failed to completely hide his administrative activities on AlphaBay’s servers; once authorities had his name from the email, they could correlate it with other data and eventually pinpoint him in Bangkok. OPSEC, short for operational security, refers to the practices that should keep an online criminal’s identity separate from their real life.
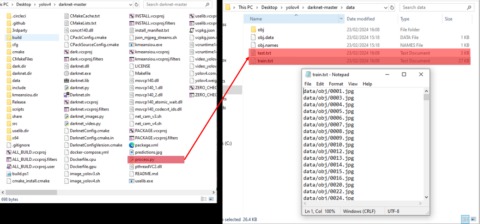
They’ll use techniques like linguistic analysis comparing writing styles and metadata analysis checking document properties or image GPS tags to connect the dots. He used his personal email to send out automated welcome messages to new AlphaBay users. Similarly, Alexandre Cazes, the Canadian behind the AlphaBay market, got comfortable and sloppy. He kept an incriminating diary and business plans on his personal laptop and cloud storage which, when seized, were gold mines of evidence. That email was protected like a neon arrow pointing to him, once investigators found it.
Is It Illegal To Access Darknet Markets?
From Tor deanonymization to blockchain tracing and undercover stings, discover how police unmask criminals on the dark web in 2025 and why anonymity is no longer guaranteed. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. The legality depends on your activities and your country’s specific laws regarding darknet use. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet.
Market Operations
Dark markets are online platforms on the darknet where illegal goods and services are traded. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. The anonymity and encryption provided in dark markets create a haven for cybercriminals and nation-state actors to buy and sell dangerous assets while evading detection.
Escrow Services
Personal data, such as home addresses, birthdays, private email addresses, and Social Security numbers? These job listings often outline specific requirements for applicants, such as technical proficiency in programming languages, experience in evading cybersecurity measures, and a proven track record of successful attacks. Going to dark websites is not against the law, but doing unlawful things or viewing illicit content is. The Dark Web, also known as the “invisible web” or the “hidden web”, consists exclusively of websites that do not appear on search engines and cannot be accessed by conventional web browsers.
- While the darknet continues to be a breeding ground for cybercrime, efforts are underway to mitigate its impact.
- We’ve seen how traffic analysis can unmask users, how blockchain forensics can follow dirty money, and how even the most careful criminals can be tripped up by a human mistake.
- This means half of the users who suffered a data breach fell for a phishing attack.
- Machine learning is another big player here—it helps by analyzing data to predict and identify suspicious behavior much faster than a human ever could.
- When shortages arose in regular marketplaces of various COVID-19 medications, the Darkweb showed their high availability and vice versa.
Darknet Markets are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity! Eleven years after the launch of the pioneering Silk Road online black market by Ross “Dread Pirate Roberts” Ulbricht, new generations of underground markets have continued to sell illicit substances, malware, firearms and more online, oftentimes via darknet sites. In this article, we will delve into the depths of the darknet and explore how cybercriminals utilize these underground markets.
Cybercriminals use darknet markets to buy and sell illegal goods and services, as well as to launder money. Darknet markets are used to sell a wide variety of illegal goods and services, including drugs, weapons, stolen data, and hacking tools. In this article, we’ll explore how cybercriminals use darknet markets and what steps law enforcement is taking to combat this growing threat. They provide a platform for cybercriminals to buy and sell illegal goods and services, including drugs, weapons, stolen data, and hacking tools.
- Despite the growing adoption of cryptocurrencies, you must be aware of the potential risks to your anonymity and privacy.
- Europol’s EC3 and the FBI have also shared tools or provided on site support.
- While law enforcement agencies are working to shut down these markets and prosecute the operators and users, the reality is that they will continue to exist as long as there is a demand for illegal goods and services.
- You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers.
- These marketplaces facilitate the exchange of everything from stolen credentials and drugs to weapons and hacking tools.
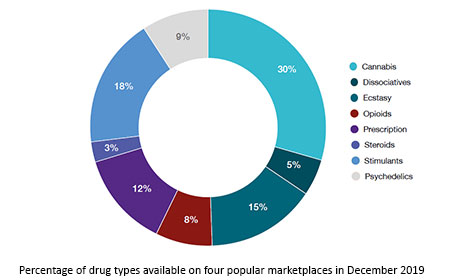
Although darknet markets accounted for a small share of drug transactions, their smoldering activities have been maintained over the past years (Décary-Hétu and Giommoni 2017; Demant et al. 2018a, b; Lacson and Jones 2016; Martin 2014a, 2014b). Accordingly, the costs were estimated at just $315 million per year based on calculations from drug-related transactions on 19 major darknet markets monitored from 2011 to 2020 (UNODC 2022b, p. 57). It is crucial for law enforcement agencies and cybersecurity professionals to stay vigilant and continuously monitor darknet activities to combat cybercrime effectively. By using encryption tools and cryptocurrencies like Bitcoin, cybercriminals can mask their identities and transactions, making it difficult for law enforcement agencies to track them down.
They operate similarly to regular e-commerce sites but use cryptocurrencies for transactions. You can access most deep web content through regular browsers with proper credentials. The deep web includes all content not indexed by search engines, like password-protected sites and private databases. You can access it for legitimate purposes like whistleblowing and freedom of expression. Businesses operating in such regions may need to adapt to the technical challenges and risks posed by using darknets for legitimate purposes. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures.
Also, loopholes in regulation introduce vulnerabilities to investors, for instance, through the failure of exchanges and sanction evasion. Cryptocurrencies are using decentralization, transparency, and security, fostering financial inclusion and innovation in decentralized finance (DeFi) and tokenized assets. They prioritize the safety of their customers’ identities and transactions to create a sense of belonging in the community.
Can Law Enforcement Track Down Cybercriminals On Darknet Markets?
A key method in protecting your organization from the threats inherent in the Dark Web is to monitor the activity within its bounds. Dark Web monitoring can also be used to check out vendor vulnerability for vendor risk assessment due diligence. In March, the FBI shut down Breach Forums, a criminal forum and marketplace that boasted more than 340,000 members. Novak is also wanted by U.S. authorities and has been indicted for being an alleged founder of the Infraud Organization, a financially focused cybercrime syndicate disrupted in 2018, with prosecutors tying it to $530 million in losses. Ransomware-as-a-service groups patronize these black market e-commerce sites to advertise for affiliates. The availability of such data on the Dark Web fuels identity theft, financial fraud, and other cybercrimes.