Just remember that if you’re not a big user of Ethereum and its related tokens, MetaMask might not be much help to you. Cold wallets are usually gadgets that help you store sensitive crypto information on a device that isn’t routinely connected to the internet. In this article, we’ll explore how to find legit darknet vendors and what to look for when evaluating their trustworthiness. Some offer legitimate products and services that are difficult or impossible to find on the surface web. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. The offers on the site do not represent all available financial services, companies, or products.
New Forums

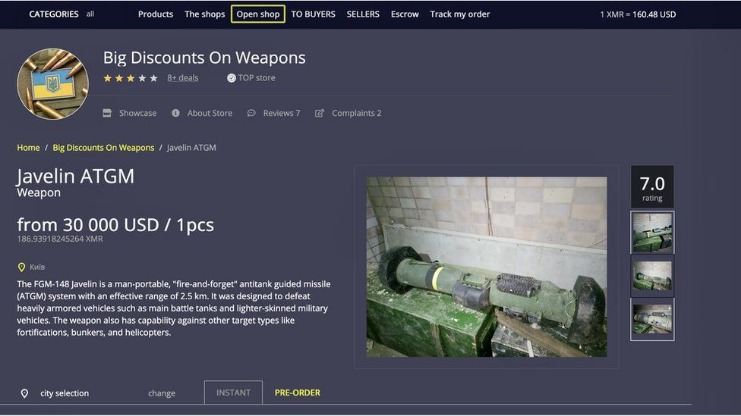
Dark web black markets thrive on the sale of stolen data, often sourced from large-scale data breaches. Both physical goods, such as drugs, and digital goods, such as software and credit cards, are sold on the ToRReZ Market. Over the next two years, the Silk Road set the standard for darknet marketplaces. The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created.
It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. Moreover, you can use a Tor circuit, but it won’t improve security; instead, it will surely improve the browsing speed. For instance, you can choose the preferred security levels for enhanced protection.
How Darknet Markets And Fraud Shops Fought For Users In The Wake Of Hydra’s Collapse
Credential markets fuel phishing and account‑takeover crime. Ransomware operators have franchised their playbook, renting out encryption malware and leak‑site hosting for a cut of each payout. Drugs still dominate darknet sales, with vendors touting laboratory test results and next‑day shipping. Dread, a Reddit‑style forum launched in 2018 and still active in 2025, hosts sub‑communities on operational security, encryption and privacy best practices alongside its more controversial market chatter. During the February 2024 Iranian protest blackouts, digital‑rights monitors reported traffic spikes to the mirror as citizens sought unfiltered coverage—proof that onion sites can outmaneuver nationwide filters.
AlphaBay Market
Medical records, in particular, are even more sought after since they contain PII and sensitive health data, making them useful for insurance fraud. Criminals can use Fullz to open bank accounts, apply for loans, or conduct other forms of financial fraud. These cards are highly sought after for their anonymity and ease of use in laundering money, making them a staple commodity in the Dark Web trade. Unfortunately, a glance at certain less legitimate online sites on the Dark Web is just as easy.
Which Markets Do Y’all Trust?
These are the most expensive items on the Dark Web markets by a long shot. One could end up with their details being used to open accounts on various pornographic websites or cryptocurrency trading sites. The hacked accounts may belong to a country that has a larger selection of streaming sites than their own.
Which Businesses Are At The Highest Risk Of Fullz-related Fraud?
This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. Data breaches like the ones mentioned above highlight the significant threats posed by dark web black markets. The stolen data included names, contact information, and order histories. This market is one of the easiest to use and is very simple for inexperienced dark-net users.
New websites and forums were created nearly overnight and very quickly filled the gap left by the sites taken down by authorities. This, however, did little to reduce the supply of illicit goods and services on the dark web. As in the previous 3 years, we conducted research into the supply and prices of various goods and services sold by cybercriminals on the dark web. Information in the listings was entered into a spreadsheet for data analysis and statistical calculations. While SSN, name, and DOB are all fairly standard in fullz, other information can be included or excluded and thereby change the price. These bundles of personal info are called “fullz“, short for “full credentials.” So instead of looking at the prices of SSNs on their own, Comparitech researchers analyzed the prices of fullz.
A Three‑Stop Postal Route For Data
Empire Market is a dark web shop that resembles the AlphaBay marketplace. However, you must wait some time to reassess this marketplace because it’s been shut down. The website allows visitors to view all the goods and services on display before they buy something. DarkOde Reborn is a great darknet market where you can find anything you want. It allows you to buy and sell a wide range of products and services with a good user experience. Its impressive anti-DDoS protection feature and easy-to-use interface make this marketplace stand out among the others.
Industry-Specific Cyber Threat Intelligence Powered By Agentic AI
Our investigation into the activities of b1ack’s Stash has unveiled a substantial threat to the security of payment card data across local banks. Regarding the validity of the stolen payment card dataset, additional details such as user agents, IP addresses, dates of birth, and email addresses suggest with high confidence that the information is authentic and not generated. In line with b1ack’s freebie marketing strategy, they announced the release of 1 million stolen payment cards for free on several popular carding forums on the last day of April this year. Considering this backdrop, it is evident that b1ack’s primary goal has consistently been to profit from the sale or use of these stolen credit card details. These methods are deliberately designed to cast a wide net, targeting users across multiple platforms where significant groups are likely to input their payment card information, thereby maximizing the potential to capture valuable data. Further investigation indicated that B1ack started this marketing campaign in January this year by posting hundreds of free stolen payment cards to build credibility and attract more customers.

These regulations encourage businesses to track dark web activities to prevent stolen data from being sold or misused. These include requiring businesses to implement dark web monitoring as part of their security posture. The anonymity provided by cryptocurrency often complicates efforts to recover stolen assets or track down the perpetrators. Major crackdowns, such as those on Silk Road and AlphaBay, have led to the arrests of countless users. Even with China’s tough controls, the country has become one of the biggest dark web marketplace centers. Ironically, some of these tight regulations have had the opposite effect, driving users to the dark web.
Recommended Content
These addresses are essential for establishing a direct and encrypted connection to the marketplace’s server. Accessing a darknet market begins with obtaining its correct onion address, a unique identifier that functions like a URL but within the Tor network. These .onion addresses are the primary gateways, and their verification through trusted directories is a standard security practice to prevent phishing attempts.
During its time online, staff members of Knight, Qilin, qBit and other ransomware gangs advertised their affiliate programs, looking for new partners. Allegedly aimed at actors looking to join the ransomware scene, Ransomed appeared on the dark web in October 2023, with more than 200 members joining the board in the first weeks. The forum widely accepts discussions about ransomware and seeks to welcome actors speaking languages other than English and Russian. The RAMP forum is also considered “friendly” to Exploit and XSS, with one key differentiating factor.
Physical Dark Web Marketplace Products And Services
- One of the most notable occurred in 2022, when 7.9 million credit card records were released.
- This level of quality assurance, combined with the convenience of direct delivery, establishes darknet markets as a primary source for many consumers.
- If you need non-VBV cards, they are often the best.
- This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself.
- The term “fullz” is used by criminals on the darkweb when they are buying or selling stolen credentials.
Sign up to receive the latest security news and trends straight to your inbox from Trustwave, a LevelBlue Company. Sign up to receive the latest security news and trends straight to your inbox from Trustwave, A LevelBlue Company. Understanding these dynamics is crucial for organizations to stay ahead of attackers, mitigate risks, and fortify their defenses against an ever-changing threat landscape.

Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs. These campaigns helped them gain users and redirect traffic after attacks such as DDoS.With an easy-to-use interface, a vast amount of data, and constant updates, BidenCash has become a favorite among cybercriminals involved in identity theft and financial fraud. The truth is that, despite the incident, the site is still active and constantly renewing its inventory.Thanks to its track record, loyal user base, and continuous flow of updated data, BriansClub remains a key player in the current landscape of dark web fraud. You won’t find drugs here, but you will find tons of credentials, RDP access, CVVs, and records stolen using malware.The platform works with data collected by well-known malware such as Lumma, RedLine, Raccoon, Vidar, and Aurora. The marketplace functions as a comprehensive online drug store, providing a vast catalog of substances. The dark-web market for stolen data is thriving, creating a new reality for cybersecurity professionals.
For this reason, fullz are typically sold by vendors along with ‘logs’, a term for login information and/or web activities history (See Figure 2), and card cloning services (See Figure 3). They are commonly utilized to cash out money from the victims’ accounts, as the complete PII in possession of the threat actor can be exploited to bypass online banking verification processes. Then the reseller, who will have a presence on one or more dark web markets, will sell the fullz off to individual customers at a profit.


