USA.gov is the United States government’s official search engine that allows you to search or access federal information and services and resources. DuckDuckGo works by using a variety of sources to provide search results, including Bing, Yahoo, and its own index of websites. DuckDuckGo has grown rapidly in popularity over the past few years, and is now one of the most popular search engines in the world. DuckDuckGo is a privacy-focused search engine that doesn’t track your searches or browsing history. Surfwax is undoubtedly one of the finest search engine tools for delving deep into the Invisible Web. Pipl is one of the most comprehensive people search engines available, and it is often used by businesses and individuals to verify identities, conduct background checks, and find lost friends and family members.
The 13 Best Search Engines To Access The Invisible Web (The Deep Web)
Phobos is a minimalistic dark web search engine known for its simplicity and fast indexing. Haystak is used to search dark web marketplaces, leaked databases, and darknet forums, often by cybersecurity experts. However, accessing illegal content through them is not.
How To Multiply Numbers In Google Spreadsheets
It allows users to search for people by name, email address, phone number, or other identifying information. Pipl.com is a people search engine that aggregates data from a variety of sources, including public records, social media, and the deep web. It’s a digital time machine, preserving the evolution of websites, content, and design over time. In this article, we’ve compiled a list of the 11 best search engines to help you dive into the invisible web in 2025. Whether you’re looking for academic papers, government archives, or niche databases, there’s a world of hidden content just waiting to be explored.
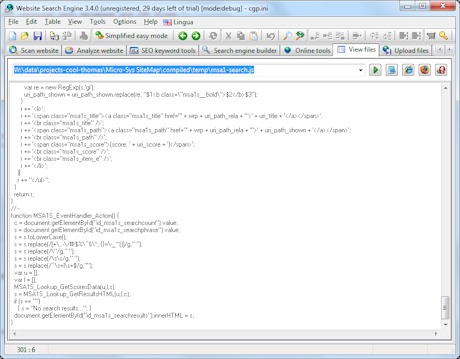
Advanced Web Search
Designed specifically for the Tor network (a browser for the dark web), it lets you search through hidden services. Simply put, it fetches information from the deep web, which conventional search engines can’t. It searches through databases, member directories, court records, and more to share relevant information about a person. Pipl is a deep search engine that specializes in finding people and their online presence.
What Content Can Be Found On The Hidden Deep Web?
We show you how to access a blocked website without breaking a sweat. What we like about it is the neat way in which it organizes information on so many different topics, including Wiki, hacking, news sites, images, video and web hosting, and cryptocurrency details. “Minimal but powerful” as described, Snow Search Engine is a constantly updated source of new onions from deeper places on the Web. Each search result is only given as a direct link to the respective site. However, there are a few countries that have banned access to BBC’s official homepage on the Web.
- You can also use it within the dark web, as it has .onion links.
- This engine uses information from publicly sourced sites (such as Wikipedia) with the aim of increasing traditional results and improving relevance.
- Unlike many dark web search engines, NotEvil prioritizes user privacy by not storing your search queries or personal data.
- The 11 search engines listed here offer unique access to hidden databases, archives, and resources that go beyond traditional search methods.
Why Is Certified Ethical Hacker (CEH V13 AI) So Popular
In addition, they share information of great importance, about the Tor network and the Tor project. Although the site is still continually expanding and improving, it has become a significant resource on the Tor network. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content. Its philosophy emphasizes privacy and not registering user information. This engine uses information from publicly sourced sites (such as Wikipedia) with the aim of increasing traditional results and improving relevance.
When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Stick to trusted databases and enable antivirus protection. Yes — you can locate where your data appears, then use removal requests or services like Defamation Defenders to eliminate it. Yes, without protection like a VPN or Tor, your activity could be logged by your ISP or network provider.
As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Site operators can also submit their own .onion sites for indexing. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser.
Torch is a leading dark web search engine known for its extensive index of .onion sites. Torch Tor Search is well known for offering anonymous browsing while enabling users to search through onion sites, which are otherwise invisible to the mainstream web. Darknet websites are one thing, but darknet markets involve a whole category of websites that may get banned by search engines. Click its “Onionize” button to search the onion links for any other dark web websites. To search for the onion URLs, you need access to a deep web search engine. These five deep web search engines can greatly expand your online research capabilities.
It grants you access to scholarly articles and research papers that might not be available elsewhere. The best thing about this search engine is it doesn’t support abusive material. Users can also contribute to the source code of this open-source search engine. The best part is that DuckDuckGo respects its user’s privacy and does not track or collect personal data.
CredShields Joins Forces With Checkmarx To Bring Smart Contract Security To Enterprise AppSec Programs
ExpressVPN uses the best encryption on the market to protect your data. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This just involves turning on your VPN before you open Tor and connect to dark web sites. It’s, ironically, more conspicuous than using popular browsers and sites. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. To look at it in a different way, it makes up between 90% and 95% of the internet.
Torch excels at providing comprehensive search results, whether you’re looking for academic resources, forums, or other hidden services. Always verify the legitimacy of the sites you visit, as even filtered platforms can occasionally index questionable content. Whether you’re conducting research or searching hidden services, Ahmia provides a reliable platform for uncovering valuable information. Ahmia also supports user privacy by not tracking your search queries, which is essential for anonymous search.
This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. You will find all the necessary .onion links to access any content or service on the dark web. You will need the Tor browser to access these links and the other (hidden) internet, the dark web. Many deep web search engines and browsers rely on specific configurations to maintain your anonymity. Its cloud storage feature ensures your projects are accessible anytime, providing convenience and security for your data. This is especially important when using deep search engines, as they often lead to sensitive or unindexed content.

Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. The service retains no copies of any data that passes through a ProtonMail account. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The software requires two-factor authentication to receive what’s been uploaded by the whistleblower and allows two-way communication between the anonymous contact and the media outlet.

Almost every other TOR search engine does, and it’s frustrating. This provides for a much cleaner interface than most other Tor search engines. I don’t wish to mislead you, you’re here searching for ways to get to the Deep web and a search engine which will get you a list of deep web sites, right? I pasted it here as a search engine because just like a Search Engine, it has enough links to keep you occupied for months and fulfil almost every need.


