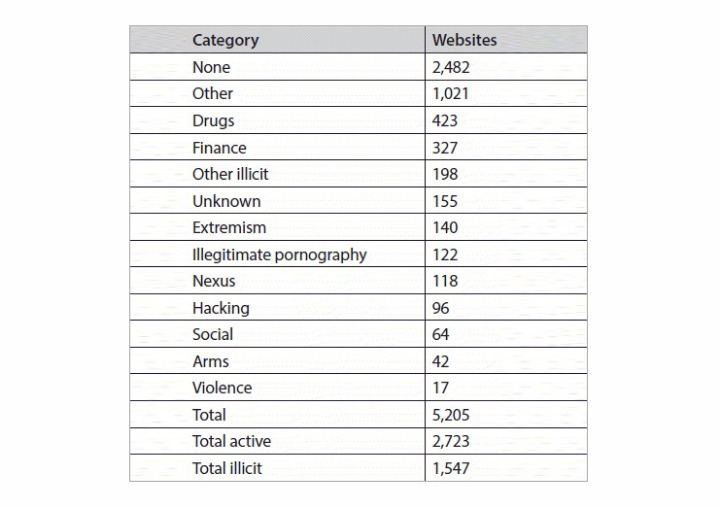
Law enforcement officials can also set up traps to capture criminals engaged in illegal transactions. For instance, money laundering can be detected by correlating cryptocurrency wallet addresses with illicit activities. Using threat intelligence platforms to analyze the threat data gathered from the dark web also enables organizations to defend themselves against attacks more effectively. Disregarding dark web security can lead to irreversible damage to an enterprise’s reputation, besides heavy monetary losses.
You can also stumble upon politically radical or extremist forums and other disturbing content. As you venture deeper, you might start to come across borderline illicit content like pirated music and movies. Your college website account, online library, or the project management app your employer uses are all part of the deep web. Although Tor encrypts your connection, its encryption standards are pretty low and a third-party could easily track your internet activity.
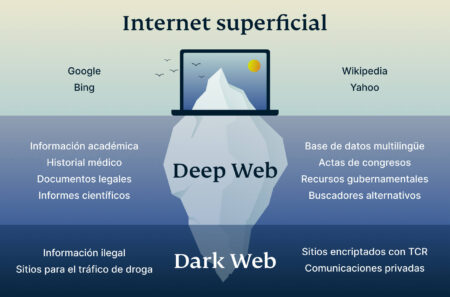
Dark Web illegal activities can lead to severe legal actions, such as arrest, and so it must be taken very seriously by the users. This information about the implication of accessing not only the deep web but also the dark web empowers the person to make responsible decisions and fathom the complexity of internet interaction. Many useful services can be found in the deep web, including facilitating research in academia, securing sensitive medical information, and providing a means for private communication within organizations. Hence, the deep web encompasses the dark web which constitutes a relatively smaller section entirely hidden and requires software specialized as Tor to access. Perhaps the most notorious of the dark web sectors, it is indeed infamous for hosting illicit content, which contains marketplaces trading everything from drugs and weapons to stolen data. People might operate under anonymity without revealing their identity, which could protect their privacy but can also lead to illegal activities.
Most People Access The Deep Web Everyday, But Not The Dark Web
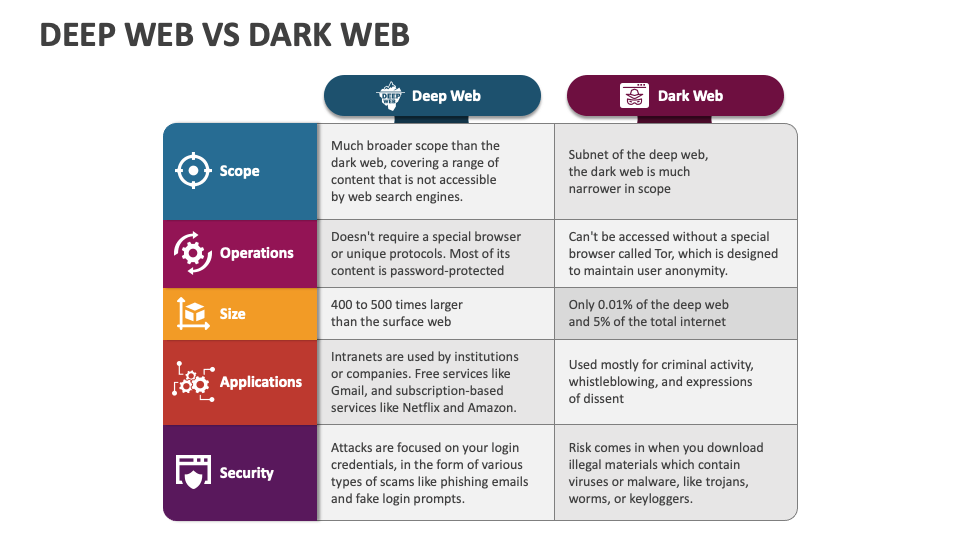
While the dark web typically boasts content that is deliberately hidden and needs special software, such as the Tor browser, to access. The websites that we frequently come across are just the tip of the iceberg of the vast amount of content that’s available on the internet. It also includes websites that simply choose not to be ‘crawled’ by search engines.
Most of our usage of the “private” internet is through authenticated portions of the deep web. Since then, the Silk Road has reappeared and been shut down again, but has never become as popular.Monitoring the dark web for illegal activity is something that law enforcementagencies all over the world are grappling with. The principle of ‘onion routing’, which underpins TOR, was developed by the researchers Paul Syverson, Michael G. Reed and David Goldschlag at the United States Naval Research Laboratory in the 1990’s.
Frontier Sites
- Ultimately, the Deep Web serves as an essential backbone for modern digital life—enabling privacy, secure collaboration, and the storage of sensitive information.
- Xcitium provides advanced cybersecurity solutions, including Zero Trust architecture, to ensure the safety and integrity of your digital assets, whether you’re navigating the surface web, deep web, or protecting against dark web threats.
- Cybercriminals take advantage of the privacy and anonymity that the Dark Web provides for a variety of purposes.
- According to SpiceWorks, the deep web hosts around 7,500 terabytes of data, whereas the surface web hosts 19 terabytes.
- While it’s best known for underground markets, drug sales, and hacking services, it also hosts legitimate content.
The Deep Web’s design prioritizes privacy, inherently limiting accessibility. The main purpose of the deep web is to protect private information. The dark web deep web difference is primarily in their accessibility methods and intended purposes.
MANAGED SERVICES
The information available on message boards and forums suggests a paywall where users can see truly hardcore and shocking content. It is encrypted and regularly updated, meaning your data won’t be easily accessible to malicious parties. Fortunately, if this data is no longer accurate to create harm, you have little to worry about – especially if you use multi-factor authentication. This leaked data helps hackers and other cybercriminals get the info needed for identity theft, stuffing attacks and nefarious activities of all kinds. The reason for this is because the primary transacted good is the data of users. What is illegal in every jurisdiction is using the dark web to acquire illicit products or services.
Stolen data often ends up on the dark web for sale, giving cybercriminals the incentive to target organizations with sensitive customer data (such as financial institutions). Subscription-based applications can be accessed only once the user has paid for them. Organizations use intranets for internal communication and documentation and for hosting internal online tools. They require access to a specific VPN service and credentials before they can be viewed. Intranets, or internal networks used by companies and academic institutions, cannot be accessed by the public.
Is It Illegal To Access The Dark Web?
But unlike the latter, the dark web is not accessible via a typical web browser like Chrome or Firefox. If you access your YouTube account’s settings page, that’s the deep web. In your daily life online, you frequently jump between the surface web and the deep web, likely without realizing it. Sure, you’ll find Netflix via a Google search, but you won’t find the player for Love Is Blind, Season 9, Episode 1 unless you log into the site first.
Get The Latest Cybersecurity News And Updates Sent Straight To Your Inbox
Web pages on the Dark Web can only be accessed using the Tor browser, and users need to know the URL of the website to find it. Unlike the Dark Web, sites on the Deep Web can be accessed using normal web browsers like Firefox, Google Chrome, and Safari. Expanding their reach – through the use of Dark Web monitoring tools – can be invaluable to a corporate cybersecurity and risk management program. The Gray Web is referred to as the part of the Surface Web where fraudsters discuss or research their activities.
Besides, governments might actively monitor such activity, and anyone showing a keen interest in the dark web can become a law enforcement target. Tor browser is a tool used to browse the web privately. Dark web hosts project which ends with .onion (aka onion sites) and not .com, .net, .org, etc. that we generally operate with. Like its name, it’s dark (within deep), meaning it’s hard to find. But that can’t be said for the section of the internet we are about to discuss. Some of these password-protected pages (deep web) are marked with a “no-index” tag which prevents search bots from crawling them.
Are The Dark Web And The Deep Web Illegal?
Consequently, more data will be stored on the web, giving cybercriminals more opportunities to acquire and exploit it. It is estimated that almost fifty per cent of the world’s population has regular access to the internet. This may be accomplished by password-protecting sites that are only accessible to those who pay and restricting access to specific IP addresses.
When you think of the “dark web,” you probably imagine an underground, secretive network of sites, where illegal activities are aplenty, passing drugs, contraband, and illicit media with reckless abandon. Since you need special protocols to access these sites, that traffic is often private and anonymous. Just as you use Chrome to access public internet sites like Facebook or Lifehacker, you use a dark web browser to access dark web pages.
There isn’t any one way to access the deep web — it just depends on what you’re looking for. The deep web is also used by corporate organizations that want to protect sensitive business-related information, such as hospitals with online networks for internal use only. Some parts of the deep web require additional layers of encryption or permissions to access. My work bridges the gap between technology and cybersecurity education, helping to inform and empower others in the ever-evolving cyber landscape. With awareness and prudent practices, you’ll be better equipped to explore the internet responsibly, harnessing its vast resources while minimizing the inherent risks. Ultimately, the Deep Web serves as an essential backbone for modern digital life—enabling privacy, secure collaboration, and the storage of sensitive information.
And lastly, firewalls and other security tools prevent web crawlers from indexing these websites, hence their unavailability on regular search engines. That’s because these websites have been purposely hidden from web crawlers of these search engines. You can’t access websites on the dark web through search engines like Google, Bing, or Yahoo. Also known as the “hidden” web, the deep web is the collection of sites that aren’t indexed by search engines.
- The vast portion of the internet not indexed by search engines, including private databases and password-protected sites, which are primarily used for legitimate, secure data storage.
- If you watched a single procedural TV series recently, they definitely featured at least a single internet-heavy episode.
- Maybe you’re a journalist and you are communicating with sources who want to keep their identities private.
- In this case, two familiar people communicate with each other directly over the internet.
- The internet experience on the deep web is devoid of hurdles.
- Popularly known as the visible web or indexed web is a unit of the WWW (World Wide Web) that is open for general usage and can be accessible by anyone around the world.
Obscurity simply refers to the inability to find an internet resource in one of the major search engines. It’s where our daily online activities take place, and what most people consider to be the Internet. Therefore, although it’s not illegal to just access the dark web, it makes you one of a kind. Therefore, it’s a perfectly safe place on the dark web, like many other onion sites you can easily google.
Heisenberg Dependency Health Check – GitHub Action For Supply Chain Risk
Understanding the Deep Web and Dark Web can help you navigate the internet with greater awareness. Contrary to popular belief, neither the Deep Web nor the Dark Web is inherently illegal. It’s particularly useful for journalists, whistleblowers, and individuals living in regions with internet restrictions. For those needing an additional layer of privacy, the Dark Web provides more anonymity.