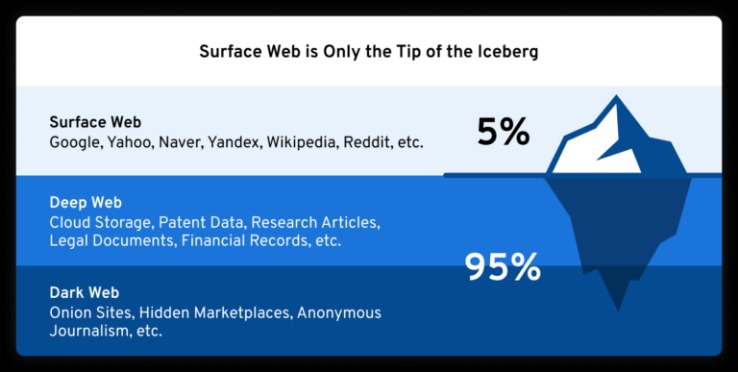
The Google search engine, for example, “crawls” the web looking for websites that are open for anyone to visit. Definitions may vary a little, but the surface web is essentially all of the websites and resources connected to the internet that can be freely discovered and visited. There are also phone number and people finder websites that give you detailed reports of individuals. Such databases give advanced access to hidden information. Google might not follow such pages, but it will still look through the top directory and may find the hidden content there. These parts of a website are off limits to regular visitors, and only legitimate users can access them.

Facebook Onion Site
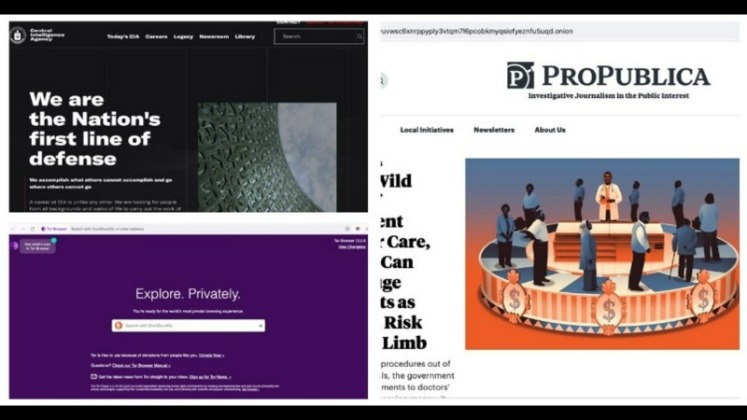
Much of this content is in the form of databases that are accessible only by password or subscription or for a fee. Called “dark” because it is accessible with anonymity and only through certain networks and software such as Tor, this part of the Internet represents a small fraction of the overall Web. They can only be accessed using Tor Browser, which gives users access to the Tor network. This anonymity can be achieved in various ways, but most of the sites on the dark web are “onion” sites. These are websites and servers that have been deliberately hidden. The “deep” web then, is all of the stuff connected to the internet but hidden away behind some form of security.
Online College Rankings
Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. ProPublica covers all the controversial stories from corrupt politicians, child labor, etc., in English and Spanish. The website is available on the surface web and has a .onion site. ProPublica is a popular online publication that won five Pulitzers in 2016.
These digital explorers traverse the vast expanse of the World Wide Web, indexing its content for public access. Likewise, content secluded behind paywalls, ranging from exclusive movies to subscription-based stories, coexists within the territories of the Deep Web. By monitoring the dark web, users might gain the advantage of knowing where exploits are before they become widespread threats. Logging into Gmail or LinkedIn, or signing in to the Wall Street Journal are just a few examples of accessing data on a deep web site.
Naval research laboratory first launched intelligence tools for Deep Web use in 2003. What they lack, however, is the ability to index the vast amount of data that isn’t hyperlinked, and therefore immediately accessible to a web crawler. This metadata, consisting of elements such as page title, page location (URL) and repeated keywords used in text, takes up much less space than actual page content. Understanding how surface pages are indexed by search engines can help you understand what the Deep Web is all about. The sites that traditional searches yield are part of what’s known as the Surface Web, which is comprised of indexed pages that a search engine’s web crawlers are programmed to retrieve. They can monitor exit nodes but cannot easily trace traffic back to individual users unless mistakes are made.
What Is The Darknet?
The same Naval research group to develop intelligence-gathering tools created The Onion Router Project, now known by its acronym TOR. “Anonymity has its value, and many users simply prefer to operate within an untraceable system on principle.” This may or may not be intentional; for example, content behind a paywall or a blog post that’s written but not yet published both technically reside in the Deep Web.
Other Deep Web Tools
Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week. Tor Search is a very efficient search engine because it indexes new content all day from the TOR network. This search engine’s mission is to be leaders in providing services on the deep web, protecting the anonymity of each user. However, not Evil is not a repository for illegal services and illegal material. It is also possible to find sensitive data on the deep web that can be stolen or abused, and, of course, the possibility of encountering individuals who engage in cybercrime and unethical, even harmful, activities is always a risk in the online world.
Dark Web Chat/Social Networks
As news outlets rarely concern themselves with explaining exactly what it is besides being a place where you can anonymously acquire illegal goods. If you’ve followed the news in the last two decades, you’ve probably heard stories and seen headlines about the deep web or dark web. All our content is written fully by humans; we do not publish AI writing. However, any earnings do not affect how we review services. The surfaced results account for a thousand queries per second to deep web content. Google’s deep web surfacing system computes submissions for each HTML form and adds the resulting HTML pages into the Google search engine index.
Though people usually think of dark websites as the wrong online place, that’s not the complete truth. As when visiting ordinary websites, stay alert to security risks on onion sites. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts.
How Can Private Investigators Leverage Data And Information On The DarkNet?
If you can’t think of a strong password, consider using a password generator. It uses obscure or obfuscated servers to hide VPN usage from ISPs and anti-VPN applications and services. Its server network is widely extensive, and it has state-of-the-art encryption, prevents IPv6 and DNS leaks, and ensures privacy with a no-logs policy.
Congratulations to Hayden Dalby, writer of the winning story, “Playpen” (Click HERE to read). And still the internet feels like “the new thing.” I used to take it for granted, like we all do. Sometimes I find it hard to believe that I’ve been an internet user for twenty years now. My local internet cafe is not much of a sight to behold. The storm made the city street a blur to Tim Avery as he walked rapidly down the sidewalk. My foot tapped eagerly on the floor of the internet cafe.
How Tor Browser Works: Simplified Explanation
- Note that connections inside of the Tor network are end-to-end encrypted by default, meaning there is no separate encryption layer necessary as with regular websites.
- Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff.
- Since the internet is open to everyone, there is no privacy.
- There are some specialized websites or search engines that catalog some deep websites.
- TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki.
- The U.S. Army developed “onion routing” to protect intelligence communications online.
This means that if you do anything illegal on the dark web and are unlucky enough to be routed through one of these nodes, the authorities will be well aware of what you’re doing. Tor encrypts your traffic through multiple relay nodes, but it’s important to understand that this encryption is removed at the exit node before reaching its final destination. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened. For example, one of the most common ways to access both the deep web and the dark web is through Tor.
Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. Think of it as the internet’s wild card. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. But even though it seems like there’s a lot out there, this only makes up about 4% of the entire internet.
Constant reports of data breaches, identity theft, and state-sponsored hacking fill our daily headlines. To see more like these, please look at our Research Beyond Google article. What people don’t understand is what exactly constitutes deep web information. Request access; this could be as simple as a free registration.
Find The Main Page With Google, Then Explore
It wouldn’t be until he gave me a list of links that I would truly understand just why people referred Tech researcher and writer with a passion for cybersecurity. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
My advice to you would be to stick with the editor’s pick. Well, now it’s time to fire up Tails and do a little bit of tinkering. For this tutorial, I’ve used Universal. I recommend using a stick since DVDs have a read-only function after you’re done burning well and accessing the dark web required a bit of writing. It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure. Because it’s easier to contain malware in a virtual environment, which can be fully controlled.