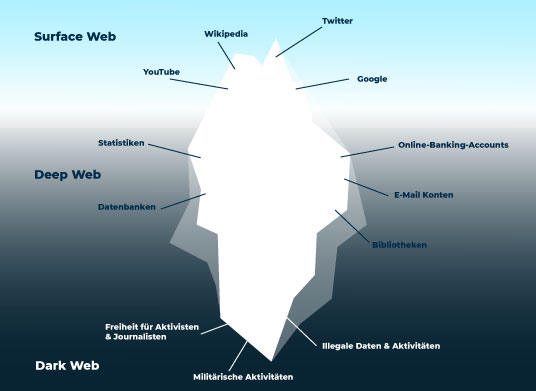
It’s crucial to understand the operational mechanics of these marketplaces. The sheer scale of data breaches has created an unprecedented supply of raw material, flooding these markets and lowering the barrier to entry for a wide range of cyberattacks. Here’s a quick look at the going rates for common types of stolen data and cybercrime services on dark web marketplaces in 2025. Strong security on Gmail, such as two-factor authentication and suspicious login warnings, push the price down to just $1 compared to other providers, as access can be swiftly revoked, rendering the hacked details useless.
Nexus Market’s Reliable Service
- To ensure uninterrupted access, the market administration provides a regularly updated list of verified mirror URLs.
- Platforms such as Nexus Market have refined this model, offering users a reliable and streamlined experience.
- On the dark web, Tor encrypts your data and bounces it through multiple servers around the world before reaching the destination website.
- Secure escrow services are standard, holding payment in trust until the buyer confirms receipt, which protects both parties and builds marketplace integrity.
- This system is engineered for both ease of use and security, facilitating swift and anonymous financial exchanges that are integral to the platform’s function.
Platforms like the Nexus darknet market utilize sophisticated encryption and Bitcoin transactions to facilitate anonymous trade. This process ensures a consistent and secure entry point, facilitating uninterrupted access to the marketplace’s inventory and services. This infrastructure ensures that Nexus Market and similar platforms remain accessible, providing a resilient foundation for secure and private commercial exchange.
Darknet Market Prices: How Much Is Your Data Worth?
Do you need proof that cybercriminals have developed a taste for a huge variety of Dark Web data offerings? Nevertheless, three new cryptocurrency-based products debuted on the Dark Web this year. Guides to cashing out these transfers without alerting the authorities often accompany the purchase of payment processing accounts, another commonly listed item. The value of a hacked account will fluctuate because these entities vary in cybersecurity capabilities and insurance.
Key Risk Indicators To Monitor
This is addressed through a system of multiple mirrors and official links. Such operational resilience is achieved through robust server infrastructure and proactive administrative management. This stability is characterized by minimal service interruptions and consistent uptime, which is crucial for maintaining the continuous flow of commerce. The efficiency of this system is comparable to that of mainstream e-commerce, but tailored for the anonymous acquisition of controlled substances.

The operational framework of modern darknet commerce is fundamentally built upon the decentralized and pseudonymous nature of Bitcoin. The continued evolution of these platforms indicates a mature digital economy focused on transactional privacy and user experience. Market links and updated lists ensure users can navigate these spaces effectively. The operational stability of these darknet sites, including their drug market sections, demonstrates robust infrastructure.
Nexus Shop Provides Reliable Drug Sales
The efficiency of this method underscores the user-centric design of these platforms, facilitating immediate and direct engagement with the marketplace’s full range of services. Accessing these platforms begins with locating their onion addresses, which are essential for maintaining operational security. The most sophisticated markets automate this process, offering users verified and cryptographically signed mirror links through official channels to prevent phishing. The aggregation of this data over hundreds of transactions generates a vendor’s overall rating, a critical indicator of their reputation and trustworthiness within the marketplace ecosystem.
Always Available: How Darknet Markets Keep Goods In Stock
- The evolution of feedback mechanisms on modern darknet markets has transformed user interaction from a leap of faith into a calculated risk assessment.
- The reliability of these links is paramount, as they must bypass the need for search engines and provide a stable connection to the platform’s servers.
- Transactions are secured with strong encryption, protecting both the buyer’s identity and the transaction details from interception.
- The available product range is extensive, covering everything from common prescription medications to specialized research chemicals and potent psychedelic compounds.
Stable URLs and persistent access points are fundamental, minimizing the disruption caused by routine security rotations and mitigating the risk of phishing attacks. A vendor’s financial success is tied to their ability to meet consumer expectations for stealth shipping, product purity, and communication. This responsiveness to market forces ensures that popular items remain in stock while niche products can still find an audience. The darknet drug trade operates on classic economic principles, where supply and demand dictate market dynamics with remarkable efficiency. This mechanism holds the buyer’s funds in a secure, third-party account until the product is received and confirmed to be satisfactory.
Practice Account And Password Hygiene
A dynamic market list, often hosted as a .onion resource itself, provides an updated, verified index of active marketplaces and their current addresses. This system facilitates a seamless economic flow where a user in one hemisphere can instantly and securely pay a vendor in another. These systems operate on a principle of verified purchases, where only users who have successfully completed a transaction are permitted to leave feedback for a product and its seller.
While transactions are recorded on a public ledger, the blockchain, they are linked to alphanumeric addresses rather than real-world identities. While Bitcoin transactions are recorded on a public ledger, the use of Tor obfuscates the IP address from which a transaction is broadcast. This means that messages between a buyer and a vendor are encrypted on the sender’s device and can only be decrypted by the intended recipient’s device. This system encrypts and randomly bounces user traffic through a series of volunteer-operated servers globally, effectively anonymizing the connection’s origin and destination. This ensures that messages between buyers and vendors, including order details and shipping information, are encrypted on the sender’s device and only decrypted by the recipient’s device. The foundation of this security is end-to-end encryption (E2EE) for all communications.
Its infrastructure is engineered to maintain consistent uptime, a critical factor for facilitating uninterrupted commercial transactions. Users are advised to employ the Tor browser and verify PGP-signed addresses to ensure they are connecting to the legitimate platform and not a phishing replica. The available inventory includes a wide variety of compounds, from plant-based products to synthetic pharmaceuticals, catering to diverse consumer demand.
A Guide To The Best Darknet Markets Of 2025 For Secure Shopping On Nexus And Other Top Sites
Note that the DDoS attacks offered below are described by the target, thousands of access requests, quality, speed, and duration. These can hijack computer resources via ransomware or steal user or patient information. Easy availability and low accuracy make data from email dump notoriously cheap.

Nexus Tops Darknet Market Lists For Reliable Access
For consistent entry, it is standard practice to verify the link’s authenticity through PGP signatures provided by the market administration, which prevents phishing attempts. Users must procure these addresses from specialized updated market lists and forums that are maintained by the community. The platform’s structure supports this variety, allowing for efficient categorization and searchability. This evolution is driven by the maturation of platform infrastructure and the widespread adoption of more sophisticated cryptographic escrow systems. Platforms like Nexus Market represent the current pinnacle of this evolution, providing a user interface that rivals conventional online retailers.
Market mirrors are identical copies of the market’s main website, hosted on different server infrastructure and accessible via unique URLs. The platform’s design minimizes external dependencies and potential points of failure, creating a self-contained environment for commerce. The interface is designed to facilitate private and secure transactions, predominantly using Bitcoin or other privacy-focused cryptocurrencies.


