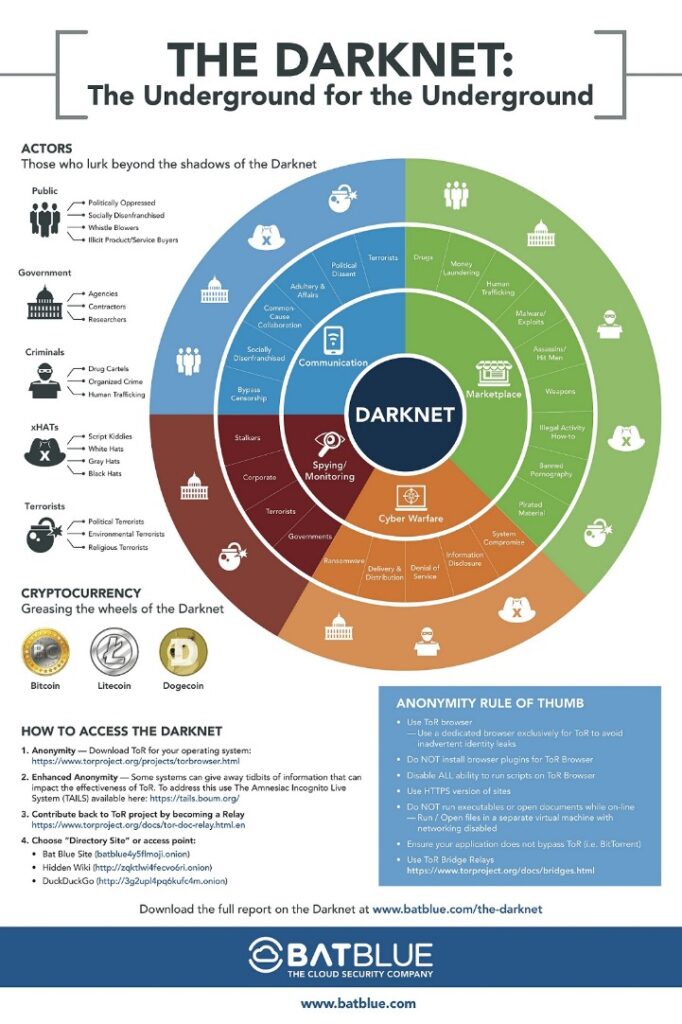
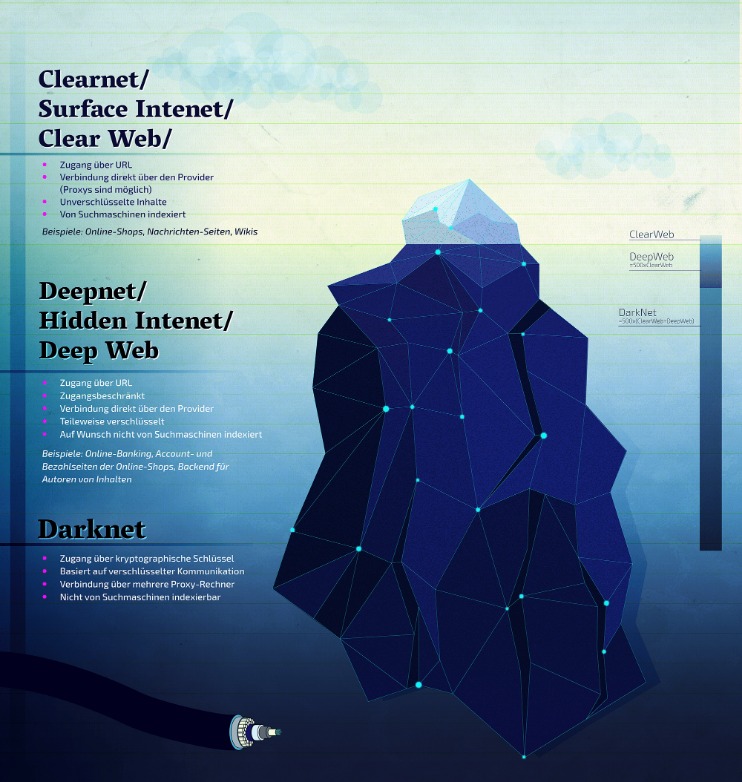
Threat actors use the dark web to coordinate attacks, distribute exploits, and monetize their operations. The dark web plays a crucial role in cybersecurity, serving both as a threat vector and a valuable intelligence source. But many dark web users still use Bitcoin, and Bitcoin tells a story if you know how to read it.
Top 10 Darknet Markets Of 2025
They benefit from limited domestic enforcement risk and a domestic supply of synthetic drugs and precursors, mostly sourced from China. The Russian-language markets—led by platforms such as Blacksprut and Kraken—are far more dominant, technologically advanced, and resilient. Their longevity is generally short-lived, with most platforms shuttering or collapsing within two to three years due to law enforcement pressure, market volatility, or internal instability. TRM currently assesses that between 20 and 30 significant drug-focused DNMs are active at any given time—a number that has remained remarkably consistent over the past several years. The Treasury action followed Nemesis’s dismantlement in March 2024, when a coordinated law enforcement operation led by US, German, and Lithuanian authorities seized its servers and approximately €94,000 (about USD 102,000) in cryptocurrency.
- This paper provides details of the counterfactual experience of what may occur if a darknet marketplace is given scope to develop.
- McDonald purchased bulk quantities of fentanyl and cocaine and then directed others to complete hundreds of drug sales involving large quantities of both fentanyl and cocaine.
- You are technically aiding a criminal organization (by paying the market fee) as well as bypassing country tax laws.
- This kind of timing correlation attack only works in certain scenarios it’s notably less effective if someone is only using Tor’s hidden services and not going out to the normal internet.
- Normal rows show drug types within each group
Torum Is Dead Long Live CryptBB?
The May 2019 seizure of news and links site DeepDotWeb for conspiring with the markets created a temporary disruption around market navigation. On April 28, investigations into the Italian Darknet Community (IDC) forum-based marketplace led to a number of key arrests. At the end of August, the leading marketplace Agora announced its imminent temporary closure after reporting suspicious activity on their server, suspecting some kind of deanonymization bug in Tor. Following these events commentators suggested that further market decentralization could be required, such as the service OpenBazaar, in order to protect buyers and vendors from this risk in the future as well as more widespread support from “multi-sig” cryptocurrency payments. Such launches were not always a success; in February 2014 Utopia, the highly anticipated market based on Black Market Reloaded, opened only to shut down eight days later following rapid actions by Dutch law enforcement. Not long after those events, in December 2013, it ceased operation after two Florida men stole $6 million worth of users’ Bitcoins.
Best Privacy Protection Apps For Ultimate Anonymity And Security

This kind of timing correlation attack only works in certain scenarios it’s notably less effective if someone is only using Tor’s hidden services and not going out to the normal internet. That led straight to an individual who was running a major illegal site on the dark web. In the German investigation, officers even got an ISP to reveal which customer was using a certain Tor entry node at a specific time.
2 Policy Implications From Hydra’s Unique Features
Law enforcement infiltrates closed forums, poses as criminals, and even runs illicit services as honeypots to catch participants. In fact, many dark web busts happen because the perpetrators slipped up on their operational security OPSEC, not because of some magical decryption of Tor. In practical terms, that means a criminal marketplace on the dark web can operate with a much lower risk of being discovered or shut down… at least initially check out our latest article about Deep Web vs Dark Web.
Why People Use Dark Web Marketplaces
With enough resources and court orders, law enforcement can turn Tor’s strength the distributed network into a weakness by watching big chunks of it at once. By watching when encrypted traffic entered the Tor network and when it exited, and noting the sizes and timing of packets, they could statistically match some users to the dark web sites they were visiting. Law enforcement uses several technical and investigative techniques to deanonymize dark web users and gather evidence of their crimes.
In fact, one provider advertises that their archived dark web documents meet legal admissibility requirements, meaning the data can be used in court. Some tools send alerts when new mentions pop up helpful for tracking emerging threats or new leaks of stolen data. Think of them as Google for the dark web but private, secure, and geared for investigators. Of course, criminals adapt many now use coins like Monero or mixers/tumblers to obscure their trails. While Monero, a privacy coin, couldn’t be traced, Bitcoin could and agents followed Bitcoin flows to locate AlphaBay’s servers and even tie some funds to Cazes, the administrator. With a subpoena to that exchange or cooperation from a crypto analytics company, suddenly the supposedly anonymous Bitcoin leads to Dan’s real name and bank account.

ICE HSI Supports Extensive International Operation Targeting Darknet Opioid Traffickers
Finally, many smaller satellite cities around Moscow (such as Aprelevka or Solnechnogorsk) have a particularly high number of listings per capita. Among the less populated cities, Sochi stands out as one of the cities with the highest demand with 16 listings per 100 residents, likely related to its popularity as a resort location. Data is restricted to instantaneous dead-drop listings on Hydra except where specified otherwise.
Scamming and the reputation of drug dealers on darknet markets. Do police crackdowns disrupt drug cryptomarkets? Will growth in cryptomarket drug buying increase the harms of illicit drugs? We believe that the case of Hydra illustrates that there are many sides to the trade-off that governments face when they make the policy choice to shut down darknet marketplaces. Future studies can take advantage of a longer panel series and analyze seasonal and other temporal effects in prices, supply, and other indicators of the drug cryptomarkets, which can also result in more nuanced results with causal interpretation.
Zvonka (2017) is an early analysis of data scraped from Hydra and RAMP, the marketplace that Hydra initially competed against until RAMP was closed in 2017. First, we provide a comprehensive account of the organization of the Hydra marketplace and the core services and mechanisms that contributed to its success. With the establishment of the Silk Road in 2011, drug cryptomarkets emerged as a novel means of the drug trade (Christin, 2013). Using data scraped from the platform, we quantitatively examine the scale and the structure of the marketplace. We present a comprehensive description of Hydra, the largest darknet marketplace in the world until its shutdown in April 2022.
End Of Silk Road Dark Web Market

His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. If you’re looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. Agencies that never used to talk to each other now routinely sync up on operations.
- In August 2021, AlphaBay was relaunched after the return of one of the original security administrators DeSnake.
- It is one of the most active and up to date markets and always provides new and updated malware and data.
- At the same time, no other individual has been charged or arrested in connection with the operation of Nemesis.
- While Kamchatka Krai has a high density of Hydra listings as well, it is hard to draw any conclusions from this fact as population density is very low there.
- The impact of Operation RapTor can be attributed to the tireless work of U.S. and international law enforcement partners.
- As the darknet markets provide anonymity, you might flow out quickly and end up providing a lot more information about you than needed.
Hydra: Lessons From The World’s Largest Darknet Market
And it worked.This market focuses on stolen credit cards, personal identifiable information (PII), and SSH access credentials. Add in easy access and a vast inventory, and it’s clear why FreshTools remains highly active in 2025, even partly operating from the clear web. There are RDP accesses, SMTP logins, SSH credentials, fake pages, and even fraud tutorials. Everything is conducted within the Tor network, with payments made in Bitcoin or Monero, as is customary.One of its most curious features is its daily raffle system, funded by the market’s commissions.