El Salvador still describes bitcoin as “legal tender”, but its acceptance is no longer obligitory (as it is with the US dollar) and the El Salvador government no longer accepts bitcoin for payment of taxes or fees. The use of bitcoin by criminals has attracted the attention of financial regulators, legislative bodies, and law enforcement. Third-party internet services, called online wallets or hot wallets, store users’ credentials on their servers, making them susceptible of hacks. Research produced by the University of Cambridge estimated that in 2017, there were 2.9 to 5.8 million unique users using a cryptocurrency wallet, most of them using bitcoin.
In 2017, François Velde, senior economist at the Chicago Fed, described bitcoin as “unlikely by itself to replace monies in well-functioning monetary systems.” According to The Economist in 2014, bitcoin functions best as a medium of exchange. The Economist describes bitcoin as “a techno-anarchist project to create an online version of cash, a way for people to transact without the possibility of interference from malicious governments or banks”.
Top 7 Dark Web Marketplaces
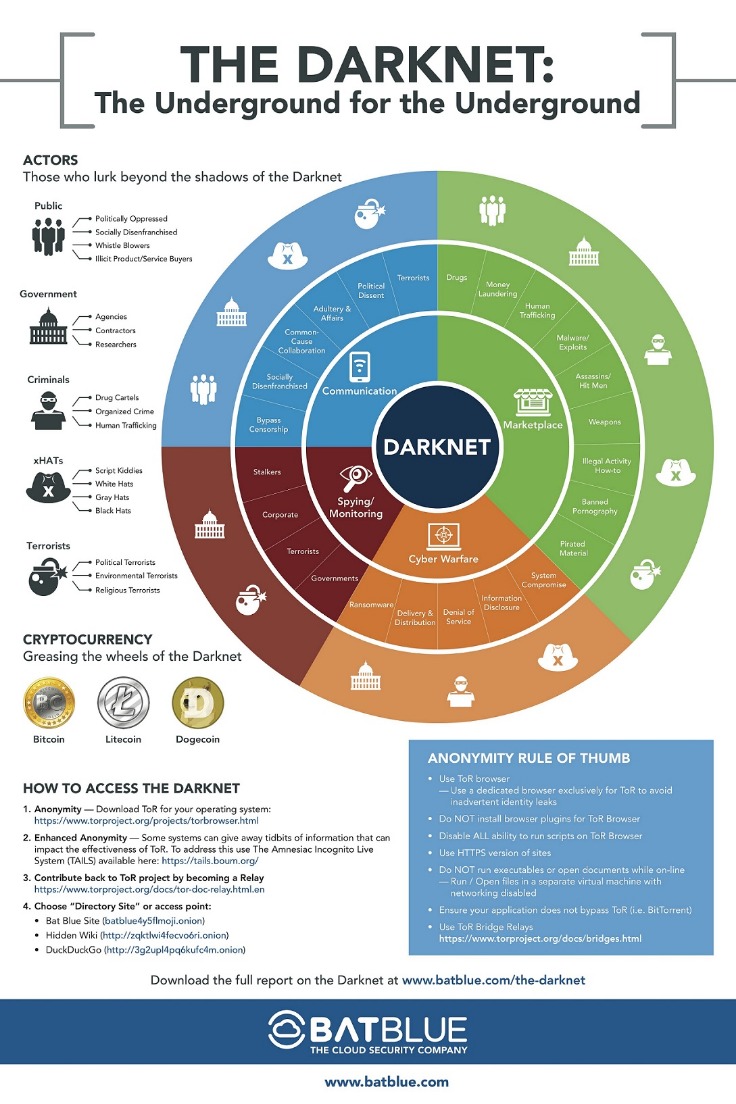
Accessible only through specialized software such as Tor (The Onion Router), the Darknet offers users anonymity and privacy, making it an attractive space for various activities, both legal and illicit. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web.
The Rise Of Monero Amid DNM Decline
Pastebins are text sharing services, useful for sending and sharing large snippets of code or text. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts.
Cyble Titan Endpoint Security

It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This just involves turning on your VPN before you open Tor and connect to dark web sites. It’s, ironically, more conspicuous than using popular browsers and sites. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. With that said, legitimate websites also exist on the dark web. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place.
Daily deposits dropped by over 90% in the final weeks, despite reassurances from its administrator. In late June 2025, Abacus users reported withdrawal issues and decreasing trust in the platform. These efforts helped it become one of the most active platforms among Australian users. TRM Labs assesses the event was likely an exit scam, though a covert law enforcement seizure cannot be ruled out. TRM will continue to closely monitor the evolving DNM landscape, including emerging platforms, vendor migration patterns, and on-chain activity, to support efforts to disrupt illicit actors and safeguard the broader crypto ecosystem.
What’s Behind This Likely Exit Scam?
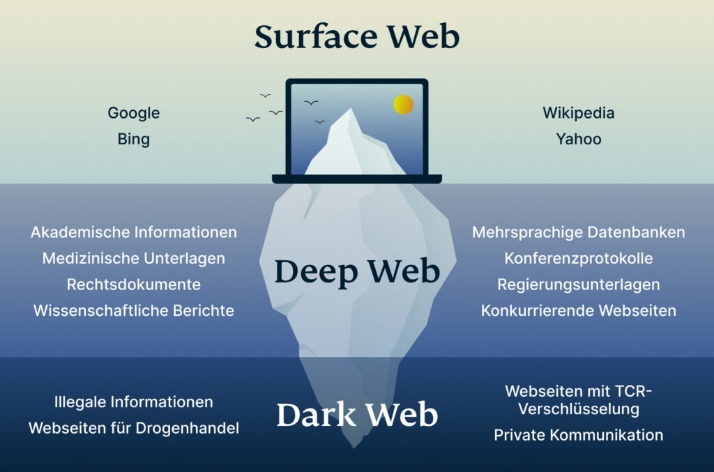
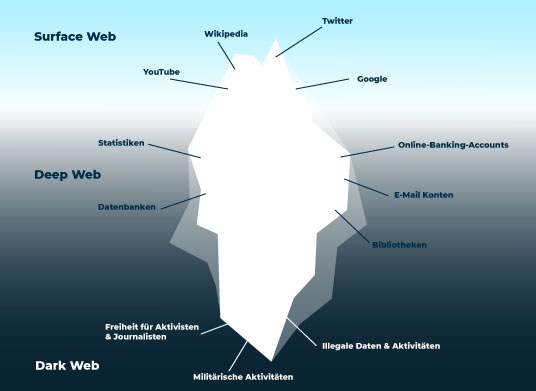
Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity. Even platforms like Netflix, which require paid access, are technically part of the Deep Web. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted. There are estimated to be 1.1 billion websites on the Surface Web as of 2025 (Internet Live Stats). Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

It can be run by a single vendor or it can be setup for use by multiple vendors and operate like a darknet market where all participants are anonymous. To prevent deanonymization of users there is no use of client side scripting languages.This means a tradeoff has been made in favor of security and anonymity resulting in a basic 1990s appearance and minimal features.The application does not utilize email in any way because it is insecure and can reveal identities. The main distinction from other alternatives such as WooCommerce is that privacy and anonymity are the primary design goals.Both the website operator and all users of the web application can conduct business while remaining anonymous.This is achieved by running the web service as a TOR hidden service and encouraging PGP communication between users.TOR is recommended but if anonymity is not required, it can be used without TOR. Extensive research that focused on over 150 of the most prominent message boards and marketplaces on the dark web reveals that Litecoin is unexpectedly “surpassing other cryptocurrencies in preference”. “The Dash network is not aware of a single Darknet market that uses Dash on its platform,” said Ryan Taylor, Dash CEO. “We believe it is an absurd assertion that the report concluded that 20% of vendors accept Dash for Darknet transactions. Unexpectedly, Bitcoin Cash was the third-most common cryptocurrency with 13% of vendors trusting it as a payment method.
Dark Web Black Market Technologies And Tools
Navigating darknet links requires a comprehensive understanding of essential safety protocols to protect your privacy and security. This comprehensive approach provides the highest level of protection when accessing darknet links, though it may require additional technical knowledge and setup time. Advanced users often employ multiple security layers, such as running a secure operating system alongside a VPN and specialized browser.
It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Law enforcement agencies do monitor these spaces, and just because it’s anonymous doesn’t mean you’re invisible. Just visiting the dark web, or using a tool like Tor, isn’t illegal in most countries. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
Top Dark Web Marketplaces Of 2026: A Deeper Dive Into Illicit Trade Markets
Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. Site operators can also submit their own .onion sites for indexing.
In December 2013, the People’s Bank of China prohibited Chinese financial institutions from using bitcoin. In June 2013, the US Drug Enforcement Administration seized ₿11.02 from an individual attempting to use them to purchase illicit drugs. Andresen later became lead developer at the Bitcoin Foundation, an organization founded in September 2012 to promote bitcoin. On May 22, 2010, the first known commercial transaction using bitcoin occurred when programmer Laszlo Hanyecz bought two Papa John’s pizzas for ₿10,000, in what would later be celebrated as “Bitcoin Pizza Day”.
- These platforms cater to specialized criminal sectors, making them more efficient and organized.
- FreshTools has been around since 2019 and has earned its place as one of the most well-known underground markets, even though it doesn’t follow the traditional dark web rules.
- The legal status of bitcoin varies substantially from one jurisdiction to another.
- Regular browsers like Chrome or Firefox, even with additional security extensions, cannot match the specialized security features built into Tor.
- As Bitcoin leaves its place of being the most favored cryptocurrency used in the criminal community, Litecoin – and not Monero or Ethereum – appears to be ready to rule.
- In May and June 2022, the bitcoin price fell following the collapses of TerraUSD, a stablecoin, and the Celsius Network, a cryptocurrency loan company.
Acronis Cyber Protect Cloud: New Version C2505

In addition, the black market is increasingly abandoning Bitcoin due to the high cost of commissions for operations. Waiting for unconfirmed transactions on the network increases their risk of being deceived. Any drug marketed as an opiate, be it pressed pills or heroin, may also contain amounts of tranquilizers or fentanyl. Many DNMs sell “pressed pills” which are fake pills cut with more dangerous illegal substances.
The prospect of having to wait up to 24 hours to confirm their transactions, in addition to exuberant payment fees, has rendered Bitcoin payments unusable for a large group of bad guys. To address this abuse, most vendors adopted a rule requiring three confirmations before treating transactions as complete. The same technology that makes blockchain networks resilient, relying on the distributed network of miners to maintain transaction history, creates an opportunity for dishonest users to double-spend their coins, if they act quickly. Dear vendors, please implement alternative payment options; otherwise, I will miss out on this Christmas season. Beginning in the middle of 2016, Recorded Future began noticing an increase in frequency of discussions regarding the functionality, security, and usability of cryptocurrency among members of the cybercriminal underground. Store and/or access information on a device.
Precautions To Take When Using Darknet Links
Litecoin payments have not been exercised in production yet. Write help documentation for buyers, vendors and administration. Paperclip gem is deprecated and image support needs to migrate to ActiveStorage. Other digital currencies such as Litecoin can be enabled in addition to bitcoin if they use the same RPC API as bitcoind. The addresses are saved as “watch-only” on the web server.It was designed to use only bitcoind so support for xpub addresses was not developed.
However, when a DNM collapses — especially a large and reputable market — its users typically migrate to the nearest available platform. Dread’s administrator, Hugbunter — who was in close contact with the Abacus team — believes Abacus’s disappearance was not the result of a law enforcement action. This signals a growing preference among darknet operators for obfuscation and anti-surveillance tools.