Our Security Colony platform relies on Breachsense data as part of our dark web monitoring service. Its primary purpose is to help individuals check if their personal information, such as email addresses and passwords, has been compromised in data breaches or leaks. Whether you are an individual or part of an organization, SpyCloud’s services empower you to proactively safeguard your digital identity and sensitive data from malicious actors on the dark web. Platforms like DarkTracer, Cybersixgill, SpyCloud, and Recorded Future are at the forefront of detecting data breaches, cyber threats, and ransomware operations in underground networks. Here’s a detailed list of the best tools based on real-time scanning capabilities, user interface, reporting features, and threat intelligence.
ZeroFox Dark Web Monitoring
Protection from viruses, hackers, and identity thieves. When you first sign up to this plan, we’ll begin monitoring the dark web for your email address right away. From shady hacking collectives and illegal marketplaces, to identity thieves and fraudsters, all sorts of risks lurk in the dark depths of the web. Botnets are networks of compromised devices used for malicious purposes. Learn how to recognize and defend against these personalized attacks on your organization. Depending on the severity of your breach, you may contact the legal authorities as well to seek legal aid.

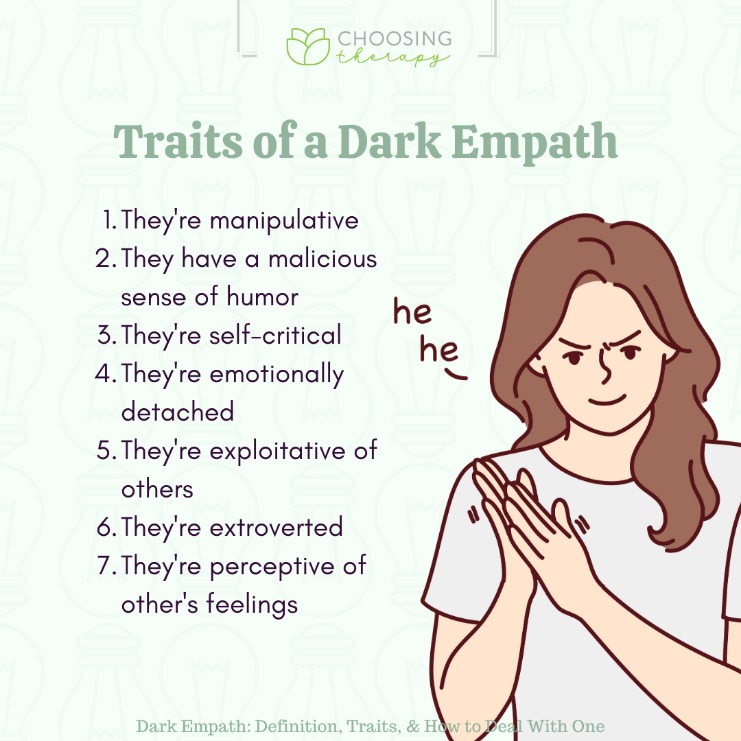
Prevention Of Identity Theft
- In this guide, we’ll explain how Dark Web monitoring works, compare the best monitoring tools, and show you how to protect your personal information in the future.
- Software tools can be loosed on known hangouts for malicious users to exchange techniques or compromised data, compiling this data into streams that can be analysed and catalogued.
- If your data is detected, you receive an alert with details about the breach, allowing you to take steps to secure your accounts.
- Frequently used for law enforcement cyber threat monitoring, it simplifies the process of extracting crucial intelligence from onion sites.
- It involves continuously monitoring dark web forums and underground marketplaces where cybercriminals trade stolen data.
These sites often harbor malicious software and compromised credentials, posing significant risks to individuals and organizations alike. Understanding the vital role of dark web monitoring is essential in today’s interconnected world. Frameworks like GDPR, HIPAA and SOC 2 all emphasize proactive data protection, and monitoring the dark web aligns perfectly with those standards. When cybercriminals steal data in a breach, they often turn around and sell that personally identifiable information on dark web marketplaces.
Tools To Help Protect You From Threats On The Dark Web
When matching data is found, the service sends an alert to your security team, enabling immediate action like changing passwords or enabling multi-factor authentication. While a scan shows what’s already leaked, continuous monitoring catches new exposures as they happen, enabling faster response to emerging threats. A dark web scan searches criminal marketplaces, forums, and breach databases for your organization’s exposed data. The most common types of data leaked include login credentials, personal details, and financial records. These areas are not indexed by standard search engines and require special tools to access.
Saved Searches

Talk to our team to see how it can protect your data and reduce your risk. Want to learn how proactive protection fits into a trusted IT partnership? At CMIT Solutions, we don’t just alert you to potential compromises—we help implement the necessary security changes to protect your business. 💡 Even monthly scanning can leave your business vulnerable for weeks if credentials are leaked shortly after a scan occurs.
When you Input your email or phone number, the site will sweep through known breached sites to determine if your data was compromised. Have I Been Pwned is a dark web scanner that specializes in identifying vulnerable info from data breaches. Using your email, it scans the dark web for known breaches and notifies you if your info has been compromised.
Trusted By Fortune 500 Enterprises, MSSPs, And Security Teams Worldwide
It’s about using threat intelligence to identify risks, like leaked personal details or confidential business data. They don’t use regular search engines to do this; they have special tools that dive deep into security systems to find and steal this info. These services extend beyond mere observation, providing a comprehensive approach to detect and counteract the ever-evolving cyber threats. That’s why many companies in these spaces don’t just use dark web monitoring as a stand-alone tool.
Features Of Dark Web Monitoring
In many cases, the real danger begins when stolen information ends up on the dark web—a hidden part of the internet where cybercriminals buy, sell, and trade compromised data. Your company’s sensitive data—like employee credentials, client information, and financial records—is constantly at risk of exposure. Request Dark Web ID pricing for your organization to see if your credentials are exposed, so you can prevent a costly data breach. The dark web is a growing threat to businesses of all sizes, but tools like Dark Web ID can provide the insights needed to stay ahead of cybercriminals. It lets you know if your sensitive data is found on the dark web, so that you can take action to fill those security gaps and identify the source of the leak. At Invenio IT, we offer an array of solutions that can work seamlessly with monitoring tools.

FUN FACTS ABOUT CYBERSECURITY
IDStrong helps you protect your personal and credit information online. Dashlane offers 3 different plan tiers to meet your specific security needs. For businesses, Dashlane offers features like customizable security settings (2FA, single sign-on, and more) and employee groups for secure password sharing and increased productivity. As a search engine, Intelligence X is unique because it works with “selectors”—specific search terms such as email addresses, domains, URLs, IPs, CIDRs, BTC addresses, IPFS hashes, and more. The platform also works with breach analysis companies and different law enforcement agencies. This lets you respond to potential cases of identity theft immediately.
This ongoing vigilance ensures that new threats are detected promptly, giving your security team the ability to respond before damage occurs. 📌 Small and medium businesses should prioritize tools that provide both credential monitoring and domain mention alerts to get comprehensive coverage without overwhelming their IT resources. 💡 The timing of these alerts is critical—organizations that respond within the first 24 hours of credential exposure can reduce the risk of account takeover by up to 70%, according to security researchers. When these tools detect a match, they trigger an alert system that notifies your security team so you can take immediate action to mitigate potential damage.
- You should immediately change your password for the account to help prevent any data theft.
- Dark Web Monitoring actively seeks out signs of data breaches so you can take swift action to help secure your accounts and prevent your personal information from being exploited.
- It ensures timely awareness of potential risks to your personal data, and gives you relevant actions you can take to mitigate them.
- These tools scan dark web websites, forums, marketplaces, and chat rooms for specific data indicators, such as email addresses, social security numbers, bank account information, and other personal identifiers.
- By establishing connections between dark web sites and other threat sources, Cyble provides actionable intelligence that enables organizations to recognize, assess, and respond to cyber threats swiftly.
- Moreover, you can integrate this solution into primary tools like SIEM and SOAR, making it one of the best dark web monitoring solutions.
While useful, these periodic scans can miss newly leaked data that appears between scanning intervals. These alerts serve as an early warning system, allowing you to reset passwords and strengthen security before attackers can exploit the leaked information. A dark web alert is a notification that your company’s data—such as employee email addresses, customer information, or proprietary data—has been detected on illicit marketplaces or forums.
These stolen credentials then appear for sale across hidden markets or leak repositories, which are indexed by monitoring engines. For defenders, this is a reminder that monitoring for leaked credentials and data involving key vendors is as important as watching their own estate. For defenders, the emphasis is on high-quality data extraction, not on manually browsing hidden services. Historically, dark web search engines were limited to poorly indexed onion services and unstable crawlers. Modern platforms now offer structured APIs, bulk data feeds, and automated alerting pipelines that slot directly into SOC and threat intelligence workflows. Dark web search engines have become essential for enterprise security teams that need early visibility into leaked credentials, impersonation attempts, and supply chain exposures.