During our research, we noticed that there is a market where the product listing data can be obtained by submitting a single request to the server API. Since the way this market obtains data on the front end of the web page is through a simple API, we are able to pass larger parameters to this said API to obtain all the data in JSON at once. Considering the file format characteristics of JSON, data transmission and formatting are very efficient and do not put more stress onto the server.
Darknet market lists and darkmarket URLs help users navigate the ecosystem efficiently. Bitcoin remains the primary currency, facilitating seamless transactions on dark web marketplaces. Darknet drug markets and cryptomarkets continue to expand, offering competitive pricing and quality assurance. Tor markets and darknet sites maintain robust security protocols, ensuring user privacy and transaction integrity.

It does not constitute legal, financial, credit, or estate planning advice, and should not be relied upon as such. Regulations, eligibility, and requirements may vary depending on your personal circumstances. Screen shot from Dread dark web forum advising users of ViceCity exit scam.
What Are Initial Access Brokers (IABs)?
It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines.
Australia Dark Report: March 2025
The surface you see with search engines like Google is the “clearnet,” but a much larger portion lurks beneath the water – the deep web. This deep web encompasses everything not indexed by search engines, including private databases, paywalled content, and, yes, the dark web. Beyond monitoring and assessment, implementing proactive measures is crucial. Employee training programs enhance awareness of phishing schemes and social engineering attacks.
Big Cities In Australia And Darknet
When the website returns a non-valid response, the crawler can call the Selenium component for manual interaction and inspection. Moreover, to the best of our knowledge, the class names used in steps 5-8 are static in terms of path or ID in the HTML code, thus indicating that the sites do not apply crawler obfuscation traps. This process also prevents crawlers from getting stuck in program deadlocks (infinite loops) 12. Initially, we tried to use an existing crawler to obtain (sales-related) data for all markets.
The number of data breaches shared on underground forums also rose significantly (+43%), as did endpoint logs for sale (+13%) and compromised credentials (+34%). Hacktivism was prevalent, hundreds of unique varieties of malware were sold on underground forums, and some of the worst vulnerabilities were found in information security products themselves. According to Chainalysis’ 2025 Crypto Crime Report, darknet market (DNM) vendors are adapting their money laundering tactics. While centralized exchanges (CEXs) remain the dominant cash-out method, a notable shift has been toward decentralized finance (DeFi) protocols. Businesses can use deep and dark web monitoring tools to keep track of stolen credentials or mentions of their brand to protect against cyberattacks.
Litecoin has the same anonymity features as Bitcoin, so next to zero, and using USDT in this context is clearly a mistake because USDT is controlled and tracked by a private institution. DAI, with its decentralised features would be a much better option than USDT, but both pale in comparison with Monero. Georgoulias et al. 18 comprehensively documented the features and functionality of existing dark web markets in 2021. In our current work, we focus on security mechanisms using more recent and broad data points. The insights and experiences we share are mostly regarding data collection.
Want To Receive The Complete “Dark Report–Australia” Each Month?
- Beyond monitoring and assessment, implementing proactive measures is crucial.
- From the perspective of dark web users and vendors, there are almost no security mechanisms to prevent or mitigate such events because the operators are the ones who implement those mechanisms.
- Finally, we describe the details of their implementation of financial security, including the supported currencies, transaction types, as well as the handling of complaints and general user support.
- Those additional security checks may include additional CAPTCHAs (i.e. making the session expire) and killing the current Tor circuit (i.e. changing the Tor identity needed).
- It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video.
- These groups often operate on a ransomware-as-a-service (RaaS) model, renting their tools to affiliates in exchange for a share of the profits.
However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
Moreover, some users use this hidden part of the internet to stay away from prying eyes. However, as the name indicates, this shady part refers to hosting illegal and inappropriate activities, including drug selling, hacking, etc. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web.
ASAP Administrator Announces That Notorious Dark Web Marketplace Is Closing
While some studies have claimed that illegal Bitcoin activity is as high as 44%. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. Data gleaned from ransomware and data breaches is available on the dark web.
- In this high-stakes environment, remaining unaware is no longer an option.
- The future of darknet drug trade lies in its ability to adapt to technological advancements while maintaining the core principles of privacy and reliability.
- These days, you often have to pass stringent verification and vetting processes to join a forum.
- Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
- As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
Rise Of AI-Powered Cybercrime
Therefore, you can prevent this exploitation by setting up a non-admin account. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
Anywhere you store personal data is a potential entry point for cyberattackers. If you’re in a coffee shop or anywhere else you don’t trust network security, use a virtual private network (VPN) to encrypt all communications. But if an attacker has access to an unencrypted network that you’re using, it’s easy to view your account data and steal or alter your information. Check out my guide to the best VPNs if you are interested in picking one. As retailers accept mobile payments and other forms of online payment, payment processors have become increasingly common.

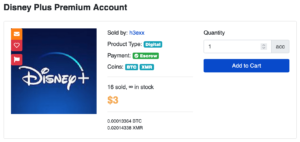
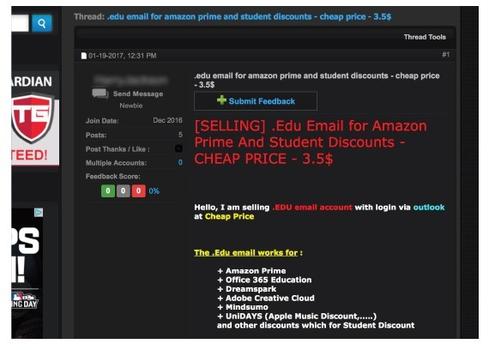
Darknets are online overlay networks one can use to access specific websites and web pages. They use specific software, authorization, communication protocols, and configurations to provide access to these sites. Every location where personal data is stored is a potential target for cybercriminals. Here are some methods to thwart unauthorized access to your data repositories. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web.
Interdisciplinary Perspectives For Socio-Technical Cybersecurity Threats
As a hidden part of the Internet, the dark web is an ideal base for many cybercrime networks, hosting illegal marketplaces, anonymous forums, unethical software, and more. In Grand Theft Auto Online, players who purchase warehouses and garages for illicit cargo and stolen cars can buy/steal and sell them through trade on the “SecuroServ” syndicate website. Globally, police seized over 41 million USD in cash and cryptocurrencies, 45 firearms, and 234 kilograms of drugs. The arrest of 150 vendors and buyers largely occurred in the US, the United Kingdom, the Netherlands, Switzerland, Bulgaria, France, Germany, and Italy. The operation shut down darknet marketplaces like DeepSea and Berlusconi. As with our previous reports, we gather data by scanning Dark Web marketplaces, forums, and websites.
Threat Actor Profiles

One such sophisticated darknet market, Hydra, offered all that and more,” Chainalysis explained. For example, two months ago a Russian national was arrested in Arizona for allegedly deployed LockBit, Babuk, and Hive ransomware. The increased law enforcement activities of the past year are changing the landscape of cybercrime—one of the dark web trends about which we can all be happy. The dark web continues to expand in scale, complexity, and criminal utility.


