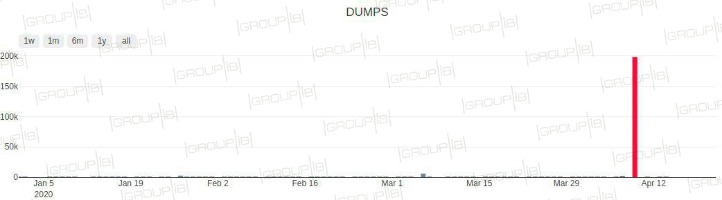
While the market shift happened, advancements in card security and other factors also continued to affect the quality of the card “dumps” appearing in forums, researchers say. Carders are still hard at work, but recent trends — including the appeal of ransomware — have altered the ecosystem. These methods are deliberately designed to cast a wide net, targeting users across multiple platforms where significant groups are likely to input their payment card information, thereby maximizing the potential to capture valuable data. Sometimes hackers will commit “card-present fraud” by breaching the point of the sale at a physical store. Or they’ll commit “card-not-present fraud,” by hacking a website and stealing the online card information that gets entered into the checkout page. As data breaches become more common, and scammers grow more sophisticated, this is a reality many people are having to contend with.
Hello Gym Data Breach Exposes 16 Million Calls And Voicemails Online
Historically when darknet sites close down, the operators disappear with customers’ or vendors’ money – this is known as an exit scam. Join us this Halloween for a live webinar exposing real password breaches and how to stop them. It has a bidding feature, with new batches of stolen data being frequently added. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
- This data is typically obtained through malicious activities such as hacking, skimming, or phishing.
- The leaked data from the BriansClub hack showed that stolen cards from U.S. residents made criminals about $13 to $17 each, while those outside the U.S. sold for up to $35.70, Krebs reported.
- Stay informed about the latest threats and trends in cybercrime, and always prioritize your personal security online and offline.
- While stealing card data can sometimes be relatively easy, successfully using it is far more difficult.
- Together, we can work towards a future where digital transactions are secure, and individuals can make financial transactions with peace of mind.
B1ACK’S STASH: A Comprehensive Analysis Of The Free 1 Million Card Leak
In addition to just selling credit card details, some threat actors offer a “complete package” often referred to as “Fullz”. Fullz includes full personal details as well as financial details such as bank account details or social security numbers, which can be used for a full account takeover or identity theft. The supply chain for carding stores like Joker relies on large data breaches, usually sourced from hacks involving point-of-sale software for large retail or merchandise outlets. Buyers, also known as “carders,” typically will then turn around and use the data to clone a card or multiple cards, which can then be used to make illegal bulk online purchases that can be re-sold for a net profit.
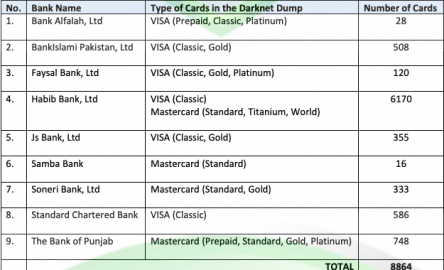
See Why DarkOwl Is The Leader In Darknet Data
Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs. Because the merchant requires equipment to clone the card and must send the buyer a physical product complete with PIN number, the price for cloned cards is much higher. According to threat intelligence Cyble, the payment card data belong to cardholders across the globe including US, Canada, India, Bangladesh, Saudi Arabia, UAE, Indonesia, Malaysia, and Singapore. Unlike a credit card, a debit card is connected directly to your checking account, allowing fraudsters to immediately drain your account.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces
Stay informed about the latest threats and trends in cybercrime, and always prioritize your personal security online and offline. Companies, on the other hand, face significant reputational damage and potential legal consequences when dealing with credit card dumps. A successful breach could result in a loss of customer trust, which can negatively impact sales and revenue. Furthermore, companies may be subject to regulatory action and fines for failing to protect consumer data adequately. In some cases, the financial burden for remediation and compensation may also fall on the company. Consumers may face financial losses due to unauthorized charges on their accounts or even identity theft.
Bitdefender offers comprehensive security and privacy plans that cater to all your digital needs. Our Ultimate Security plans (for US only) protect up to 10 devices with state-of-the-art technologies that predict, prevent and remediate new and existing cyber threats whether you’re at home or on the go. Nixon said breaches of criminal website databases often lead not just to prevented cybercrimes, but also to arrests and prosecutions. The Federal Trade Commission oversees a website called IdentityTheft.gov, which provides the appropriate steps to report and recover from credit card fraud.
Cyble TIP Threat Intel
The malware targets websites by sending thousands of connection requests, which overloads and crashes the website’s server. No information is stolen through these attacks, but they can be used to extort ransoms or hide other hacking activities. As retailers accept mobile payments and other forms of online payment, payment processors have become increasingly common. The value of a hacked account will fluctuate because these entities vary in cybersecurity capabilities and insurance.
Each card can sell for between $20 to $100, according to Business Week and the New York Times. Dark Web Informer is a cyber threat intelligence platform that provides insights into activities on both the dark web and the surface web. The site covers topics such as data breaches, darknet markets, ransomware incidents, and threat alerts. This latest pack is the fourth credit card dump the carding market has released for free since October 2022, with the previous leaks counting 1.22 million, 2 million, and 230,000 cards. The shop offers stolen card data from around the world for as low as $0.15 per item and uses verification and automated checks to check the validity of the cards people put up for sale on the platform.
Instagram Events: Marketing Tips For Bigger Impact
BidenCash shop was established in April 2022, following the seizure of other card shops and carding platforms by the Russian authorities. Since its inception, it has been attracting the attention of both old and new cybercriminal customers. Those who wish to see the “best” cards in the shop need to maintain certain minimum balances, as shown in this screenshot. Almost certainly, at least part of the appeal is that my surname means “crab” (or cancer), and crab is Russian hacker slang for “carder,” a person who engages in credit card fraud. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading.
How To Protect Yourself From Identity Theft
- They can help you dispute the charges and may provide additional security measures such as a new card or a temporary freeze on your account.
- Learn through real-world case studies and gain insights into the role of FP&A in mergers, acquisitions, and investment strategies.
- The archive also reveals the proprietor(s) of BriansClub frequently uploaded new batches of stolen cards — some just a few thousand records, and others tens of thousands.
- Soon after vDOS’s database was stolen and leaked to this author, its two main proprietors were arrested.
While consumers are typically protected from direct financial losses, dealing with credit card fraud is incredibly disruptive. Leaking credit card credentials has become a very common phenomenon on chat applications, particularly Telegram. In fact, the overwhelming majority of leaked credit cards in past months originate from Telegram channels.

Judging from the activity on the shop, BidenCash appears to be thriving in 2023, providing an active data and money exchange platform in a market that has experienced a decline in recent years. This time, the leaked data contains card numbers, expiration dates, and three-digit security codes (CVVs). The expiration for most cards reviewed by BleepingComputer ranges from 2025 to 2029, but we also spotted a few expired entries from 2023. It should be noted, however, that analysis of the previous data dumps showed that the data packs contained some duplicates as well as invalidated or expired cards, so a significant percentage of the free packs weren’t actually usable. All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online.
Censys’ Silas Cutler On How Adversaries Chain Vulns Together For Big Attacks
Companies must act promptly to notify affected customers, provide them with resources to protect their personal information, and work closely with law enforcement to identify and apprehend the responsible parties. Additionally, engaging a reputable data breach response firm can help mitigate damages and restore customer trust. Despite these challenges, companies that respond effectively to a credit card dump can minimize the long-term damage to their reputation and bottom line.
One common approach is skimming, where an illegal card reader or a hidden device captures the information encoded on magnetic strips or chip-and-PIN cards when they are swiped or inserted in ATMs or POS terminals. Skimming devices have been reported to be used at gas stations, restaurants, and other high-transaction locations. It is important to note that credit card dumps are illegal and highly unethical. Engaging in such activities carries severe legal consequences and can lead to serious financial damage to both individuals and financial institutions. Cybercriminals will use this kind of rich data grab to target you with additional attacks. They use a term known as “Fullz” in underground online forums and dark web marketplaces, where cybercriminals buy and sell stolen personal information.