Research by VPN provider NordVPN of over four million credit cards for sale on the dark web found that credit cards from US citizens were the most common, with 1.6 million of the 4.5 million analysed being from the US. Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing. Sales of passports, driver’s licenses, frequent flyer miles, streaming accounts, dating profiles, social media accounts, bank accounts, and debit cards are also common, but not nearly as popular. Use a service, like Flare, that allows you to monitor the dark web for any mentions of your organization’s information, including business credit card numbers.
Holders of any credit cards, whether you know if they have been compromised or not, are advised to monitor bank statements for any suspicious or unusual activity. If your PayPal account or credit card details end up on the dark web, it’s essential to act quickly to minimize potential damage. Full or partial credit card details are commonly sold on the dark web, including BIN numbers, credit card numbers, expiration dates, and CVV numbers.
Watch These Astonishingly Realistic Clips From OpenAI’s New AI Video Generator
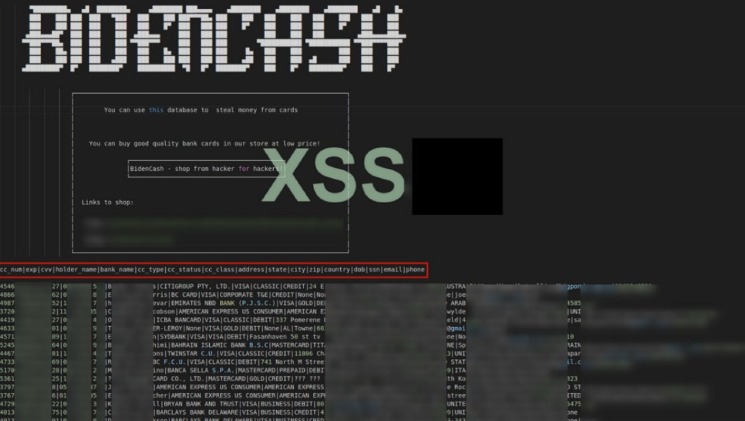
Stay vigilant, protect yourself and others, and make ethical decisions when navigating the vast landscape of the internet. Lastly, remember that the traditional web offers countless legitimate ways to engage in online transactions and protect personal information. Explore trusted websites and platforms that prioritize cybersecurity, privacy, and legal compliance. The personal details including the passport, licence and Medicare numbers of 10 million Optus customers were exposed in a data breach last month. “The subject release of the credit and debit cards data by BidenCash shop is one of the largest leaks of its kind on any of the cybercrime/underground forums in recent times,” Cyble said. As for the credit cards, the file itself features cards with an expiry date from 2023 to 2026.
Taming AI’s Threat Vectors: Why CISOs Must Adopt A Secure Enterprise Browser (SEB)
Some vendors offer a “complete package” known as “Fullz”, which includes full personal details as well as financial details like bank account information or social security numbers. Monitoring the activity on these platforms is crucial for fraud detection, brand protection, and financial intelligence. Because of the level of anonymity, these sites allow cybercriminals, it is critical to use powerful dark web monitoring tools, such as Webz.io’ Lunar, to track emerging financial and reputational threats. Since then, BidenCash has continued to operate using the “dumping” method.
Methods Used By Criminals

Once stolen card data hits the dark web, it can be hard to track down just where it lands, and it can be even harder to prosecute offenders. You can also limit your risk by being picky about your ATMs, where criminals sometimes install card skimming devices. These are hard to detect, but only using ATM machines inside banks or other physical buildings offers some protection, Thomas says.
Now that we have explored the payment methods used on the Dark Web and the necessary precautions, let us delve into the protective measures individuals can take to safeguard their personal information during credit card transactions. Now that we understand why individuals are enticed to buy credit cards on the Dark Web, let us explore the risks and challenges involved in these transactions and how to navigate this treacherous landscape. Unlike the traditional web we use every day, with search engines indexing websites for easy discovery, the Dark Web operates on anonymous networks such as Tor. This anonymity allows criminals to conduct illegal activities without fear of being traced by law enforcement agencies. As previously mentioned, credit card fraud is a massive market for criminals. According to data from Merchant Savvy, global payments fraud has increased from $9.84 billion in 2011 to a staggering $32.39 billion in 2020.
Recommendations For How To Combat Stolen Financial Data
“There are sites out there where they ‘rack and stack’ them, and say how much exactly a specific card is worth,” agrees Wilson. As data breaches become more common, and scammers grow more sophisticated, this is a reality many people are having to contend with. Kaspersky advises individuals and organizations monitor bank notifications, enable two-factor authentication and run full security scans on all devices to remain vigilant against these types of malware threats. The use of JavaScript-sniffers, also known as Magecart, has led to a significant increase in stolen payment card data. A second major leak of cards relating to Indian banks has been detected by Group-IB, with over 1.3 million credit and debit card records being uploaded to the Joker’s Stash marketplace.
It is crucial to approach the Dark Web with caution and fully understand the risks involved. It is illegal and unethical to engage in activities that exploit stolen credit card information. Protecting personal information and ensuring online security should always be a top priority. Another study by Fortra’s PhishLabs, a cybersecurity expert, discovered that 81% of cybercrime is stolen credit card data, while financial institutions like credit unions, banks and payment services remain the biggest target of scammers. Since Real and Rare serves vendors as well as consumers, it offers its users a referral program that provides them with their own personal referral URLs, which they can hand to new users and get a 10% commission for every purchase they make.
- It’s imperative you have visibility into the stolen data being used to potentially create fraudulent accounts or transactions.
- It is understood that the data included such highly sensitive information as the primary account number of the credit cards concerned, along with expiration dates and the card verification value, CVV2, security code.
- The sunsetting comes exactly a year after Joker’s Stash, the previous market leader, announced its retirement in January 2021 after having facilitated the sale of nearly $400 million in stolen cards.
- The site also has a unique news section, listing new leaks and their size.
A cloned card is a type of credit card theft where a person’s card information is copied into a new card, which allows the scammer to access their financial accounts. These aren’t just random forums, they’re organized platforms where stolen card data gets packaged and sold as “fullz” (full card details including CVV) or “dumps” (raw magnetic stripe data). Some criminals organize stolen card data by ZIP code, according to Novak, “because it makes it harder to conduct fraud detection,” he says.
Scan Millions Of Data Points

Learn the basics of credit card cards, including features, fees, and rewards to make informed decisions about your credit card usage. The three suspects from Indonesia confessed to stealing payment card data using the GetBilling JS-sniffer family. Canceling your PayPal account or credit card is a crucial step in preventing further unauthorized transactions. To avoid falling victim to these scams, it’s essential to be cautious when entering sensitive information online. This includes using strong passwords and enabling two-factor authentication.
The dark web market is growing, with retailers selling stolen credit card data, cryptocurrency accounts, hacked Gmail and Twitter accounts, and purchasable malware for significantly cheaper prices over the past year. But it’s the threat from infostealer malware that is of most concern right now, not just in terms of the gargantuan number of passwords that are available in logs for sale, but the sheer number of stolen credit cards as well. Back in the day, carding forums were the busiest of online crime hangouts, selling packs of stolen credit card data to anyone with the cash. That was then; now, you are more likely to find a roaring trade being made on the dark web in the likes of stolen passwords and account credentials, phishing exploit kits and malware-as-a-service platforms. A new report has revealed that the B1ack Stash crime forum has just given away more than a million stolen credit cards for free. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details.
Keeping Your Data Safe
Only accessible by a specific browser, the dark web keeps traffic anonymous. These generated numbers link to your real card but can be limited by merchant, amount, or time. I’ve investigated too many breaches where malware jumped from an infected office computer to the payment network. When we spot cards from these BIN ranges appearing in bulk listings, it often indicates a breach somewhere in the payment chain. One particularly interesting detection method involves monitoring dark web markets themselves. This enables systems to detect fraud based on minute changes in transaction velocity, merchant category patterns, and even the time of day purchases are made.
“As long as these markets continue to thrive, cyberattacks will remain a constant threat, making it vital business leaders arm their security teams with the resources they need to keep information secure.” Another seller was offering what they called “full profiles” of stolen identities. For the bargain price of $40, the seller would allegedly provide social security numbers, addresses, dates of birth, and less sensitive information such as education and telephone numbers. The details required to access Lloyds Bank accounts with balances of roughly £5000, for example, are on sale for up to £400 each.
The data then gets parsed, sorted by bank type and location, and sold in batches. One compromised payment processor or e-commerce platform can yield thousands of card numbers at once. Credit card fraud on the dark web operates quite differently from what many people imagine. “Many of these forums are owned by people who live outside of the U.S., where American law enforcement cannot put their hands on them,” says Mador, citing Europe, Russia, Latin America, Asia, and Israel as areas where forums have been hosted. Unless you live the rest of your life only paying with cash, you’ll never be totally impervious to payment fraud. One of the largest known underground shops, Joker’s Stash, generated more than $1 billion before getting shut down in February, according to Gemini Advisory.
From the data D3Labs has examined so far, about 30% appear to be fresh, so if this applies roughly to the entire dump, at least 350,000 cards would still be valid. Dark web posts and offers of this size are usually scams, so the massive dump of cards could easily be fake data or recycled data from old dumps repackaged under a new name. To ensure larger reach, the crooks distribute the collection via a clearnet domain and on other hacking and carding forums.
How To Protect Your Money From The Dark Web
Marijus Briedis, CTO at NordVPN, said the details for sale on the dark web are increasingly acquired through brute-forcing. Some fullz even include photos or scans of identification cards, such as a passport or driver’s license. Another important aspect is understanding your exposure when third-party breaches occur. Monitoring these sites also helps track the effectiveness of security investments.