The authorities were not the only ones to identify and/or attempt to uncover the key players (aka staff) at AlphaBay Market. When authorities carried out the warrant and arrest in his apartment in Bangkok, his laptop was left unencrypted and the admin account for the market and server logged in. Authorities also simultaneously executed search warrants for the market’s server hardware located in Quebec, Canada. Prior to Keeper, Darren served as an advisor to JiWire, now called NinthDecimal. NinthDecimal is the leading media and technology service provider for the WiFi industry. He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks.
What Is Cyber Threat Intelligence?
Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. However, when it comes to darknet markets, the story is very different. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community.
After the shutdown of Silk Road, in the last quarter of 2013, the ecosystem evolves to a structure where several markets coexist. This structural change is reflected in the median net income of sellers and buyers, as shown in Fig. While the curves for the seller and buyer median net income were negatively correlated before Silk Road’s shutdown, after that moment they became positively correlated. Specifically, sellers show a trend of increase and buyers a trend of decrease in their median net income before the shutdown. On March 20, 2024, U.S., German, and Lithuanian law enforcement agencies seized Nemesis’ servers in a joint operation. Since the takedown of Nemesis, Parsarad has discussed setting up a new darknet marketplace to take the place of Nemesis with vendors that were once active on the marketplace.
Cryptocurrency
In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere. You should be aware that law enforcement agencies may be monitoring the dark web and that visiting certain websites or engaging in illegal activities can result in criminal charges. You can also check out this ultimate dark web safety guide to browse safely.
Popular Dark Web Marketplaces
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. The marketplace is much more organized, which makes it easy to use and navigate. Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade.

Treasury Sanctions Head Of Online Darknet Marketplace Tied To Fentanyl Sales
The number of multisellers steeply decreases after operation Bayonet but they still sustain high incomes. Nevertheless, by analysing the income of each multiseller, we observe that the median income still reflects their high income, as shown in Fig. Individually, they are able to yield significant high incomes compared to other types of sellers.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
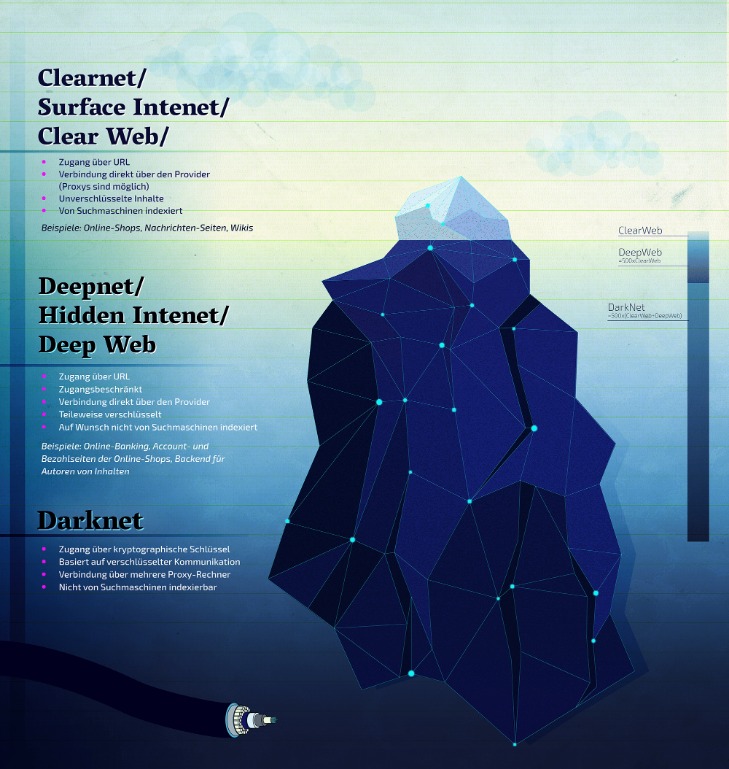
The concept of darknets emerged as a response to concerns about digital privacy and government surveillance. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity.
- While Tor provides anonymity, combining it with a reliable VPN adds another layer of protection.
- Yes, the Hidden Wiki remains one of the most accessed community-curated directories for .onion links, though users must verify each link’s authenticity.
- Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files.
- The dark web is only accessible through specific software like Tor (The Onion Router).
- Moving forward, it’s important to remain vigilant and proactive about new developments as they emerge, as continued innovation and collaboration are essential to outsmart dark web criminals.
- However, experts estimate it accounts for no more than 5% of the internet.
Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails. Some now offer customer support, escrow systems to prevent fraud, and even user-friendly interfaces that make illegal trade feel strangely routine. Still, the dangers are severe — exposure to scams, malware, surveillance, and prosecution are just the beginning. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there.
Zoom Vs Microsoft Teams Statistics 2025: Who Leads In Users, Features & Growth

Staying cautious with software and limiting what you expose yourself to are critical steps in darknet market safety. It allows buyers and sellers to exchange messages securely, ensuring that sensitive details like delivery addresses or transaction confirmations remain private. Cybersecurity companies, researchers, and law enforcement agencies (including FBI) monitor the dark web.
Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts. The dark web is only accessible through specific software like Tor (The Onion Router). Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. OPSEC (Operational Security) involves following strict online practices to protect your identity. This includes separating personal and market-related accounts, avoiding reuse of usernames, and never sharing identifiable information. Use the Tor Browser with all security settings enabled, combine it with a trusted VPN for additional privacy, and always keep your browser and operating system updated.
What Is The Role Of OSINT In Cybersecurity?
- Finally, the data is purchased by consumers who use it to commit various forms of fraud, including fraudulent credit card transactions, identity theft, and phishing attacks.
- He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks.
- Always prioritize ethical practices, and ensure that your dark web investigations are conducted with full legal compliance and operational security.
- Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices.
- The dark net is famous for being a hub of black market websites for buying and selling products and services.
- They are followed by market-U2U sellers, then market-only sellers, and lastly U2U-only sellers.
Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
The empty point on the multiseller median income line demarcates the quarter with only two multisellers. After that quarter, their number remains small, which is represented by the dashed line. In all panels, the dashed vertical line marks the time of operation Bayonet. The evolution of the ecosystem of all buyers and sellers obtained from the considered markets and the U2U network is shown in Fig. Although it shows fluctuations, including those caused by external shocks, the ecosystem exhibits a positive growth trend in terms of trading volume. As the digital underworld grows in complexity and reach, the dark web in 2025 is no longer just a fringe element; it’s an expanding infrastructure of illicit trade, advanced technology, and escalating threats.

Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks. For instance, there may be sellers that make a small amount of transactions, or spend more than receive, which we would classify as buyers. Despite consistent results, this clearly leaves space for refinements. Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities. Third, at any given moment we classify entities as either buyers or sellers.