Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes.
Myth 5: All Content On The Dark Web Is Easily Accessible
The Dark Web is a part of the internet that is intentionally hidden and not indexed by traditional search engines. It operates within a network of encrypted websites that require specific software, configurations, or authorization to access. This hidden corner of the internet offers users anonymity and privacy, making it an attractive platform for various activities, both legal and illegal.
Venturing further into the deep web does bring a bit more danger to the light. For some users, portions of the deep web offer the opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas. Others go somewhat deeper to download pirated music or steal movies that aren’t yet in theaters. Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider).
- Engaging in illegal activities on the Dark Web can have serious consequences.
- The Dark Web can serve as an essential tool for promoting free speech and anonymized dialogue in regions with restricted internet access or in the face of governmental censorship.
- Throughout the article, we emphasized the need for security precautions and protecting personal information.
- This process masks your IP address and makes it appear as if you are browsing from a different location.
- If we continue to visualize the entire web like an iceberg, the open web would be the top portion that’s above the water.
Tor Vs Alternative Solutions: What’s Best For You?
You can enter .onion URLs directly into the Tor Browser’s address bar or visit directories like The Hidden Wiki to find popular sites on the dark web. Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. If found, take immediate steps to secure your accounts and personal information.
Privacy And Anonymity
Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps.
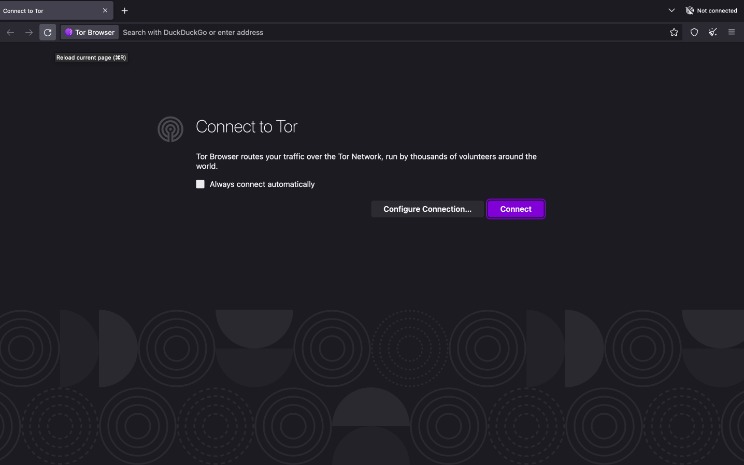
It makes visiting the dark web easy, with dedicated Onion Over VPN servers that connect you to the Tor network via the VPN. This negates the need to download, install, and run the Tor browser separately, and lets you access the Tor network without your ISP knowing. The most common way to safely access the dark web is by connecting to a VPN and then opening the Tor browser. Its inherent anonymity allows everyone from dissidents to whistle-blowers the opportunity to share information free from persecution. In many cases, this information can itself be used to prevent illegal activities. The internet providers and websites can still see that you’re using Tor, as Tor node IPs are public.
The encrypted data is sent through a series of network-based nodes called onion routers. Using a dark web-specific browser such as Tor or I2P itself is legal in virtually all countries. But using these tools for illegal purposes constitutes a criminal act either way. When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical. We recommend that you use only the Tor browser to access the deep, dark web, if you must. It is made up of two virtual machines – a Gateway and a Workstation.
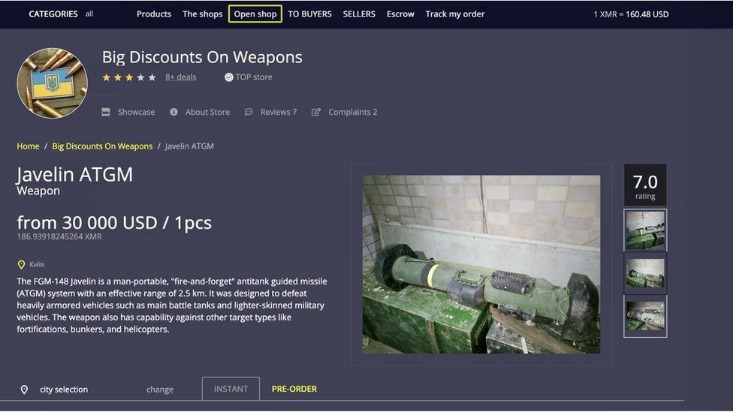
- You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is.
- Some .onion dark websites are known to contain malware, and dangerous scripts designed to damage your computer, steal your information and identify you.
- However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web.
- Remember, protecting your personal information is essential to maintaining your privacy and security while navigating the Dark Web.
- In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
Step 7: Browse The Dark Web With Tor
Lastly, we provided a list of recommended Dark Web websites, showcasing platforms and resources dedicated to privacy, journalism, whistleblowing, and secure communication. Minimize the use of your real name, address, phone number, or any other personally identifiable information. Adopt a pseudonym or anonymous username to help protect your identity. Stay informed about the latest security practices and developments related to the Dark Web. Regularly educate yourself about new threats, scams, or vulnerabilities that may arise.

Unverified Content And Hoaxes

Browse responsibly to ensure your experience doesn’t lead to unwelcome surprises. That’s a trick question, because there isn’t even a good free VPN, much less a best VPN. Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties. If top-notch privacy is your goal, yes, you can use the Tor Browser for all of your browsing. Just remember, this only hides your browser-based activities and doesn’t hide any of your other online activities.
Should You Use A VPN And Tor?
However, others may be taking advantage of the dark web’s reputation to trick users out of large sums of money. Also, some users on the dark web may attempt phishing scams to steal your identity or personal information for extortion. Infiltrations can put you at risk of monitoring for other types of activity as well. Evading government restrictions to explore new political ideologies can be an imprisonable offense in some countries. China uses what is known as the “Great Firewall” limit access to popular sites for this exact reason. The risk of being a visitor to this content could lead to being placed on a watchlist or immediate targeting for a jail sentence.
The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web.
Report It To The Authorities (if It’s Safe To Do So)
This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity. As such, you should exercise caution when accessing any unofficial dark websites. The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies.
The Tor browser provides access to “.onion” websites, which are Tor hidden services that you can only access through the Tor browser. You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web. Whether your search engine of choice is Google, Bing, Baidu, Yahoo!