The silver lining is that no one has been arrested or prosecuted for using an anonymizing browser. No, the dark web isn’t illegal, but what you do while in the underbelly of the internet matters. A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense. The entry node is the first server in the Tor chain, the relay node is the middle node and the exit node is the last server in the network.

What Is Onion Over VPN — And Do You Still Need It?
This is good practice generally, but particularly important in countries where the Tor browser is blocked, such as China, Russia, Belarus, and Turkmenistan. Accessing the Dark Web safely in 2025 demands vigilance, preparation, and strict adherence to security best practices. By carefully following the safety procedures outlined in this guide, you minimize your risk of encountering malware, fraud, or legal troubles. Always remember, your safety online depends significantly on personal responsibility, informed decisions, and proactive application of security tips.
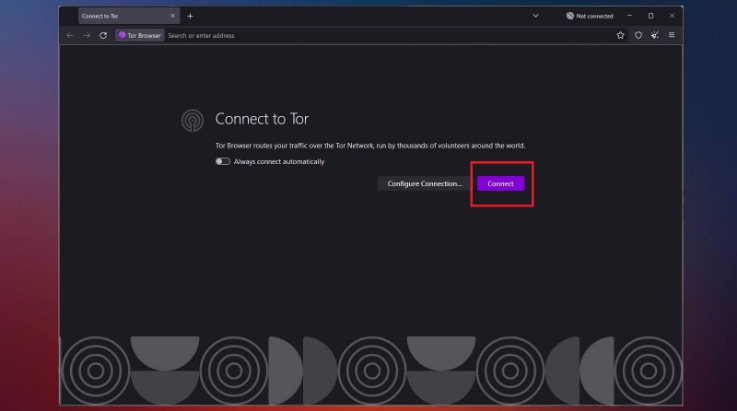
Step 7: Browse The Dark Web With Tor
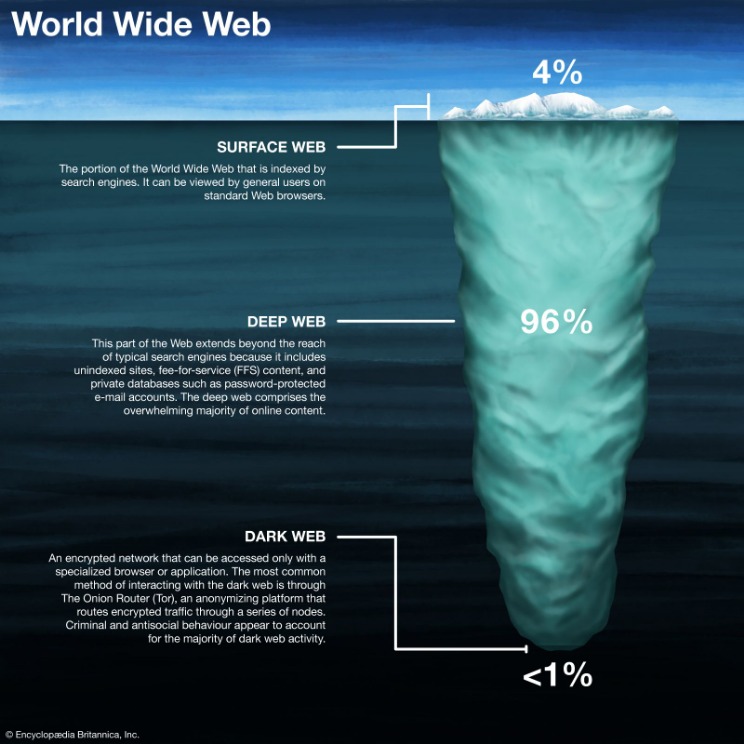
Therefore, it’s inaccessible through conventional browsers like Chrome, Edge, Firefox, Brave, and others. On the other hand, the dark web hosts marketplaces and forums where illegal goods and services—such as drugs, weapons, and stolen data—are traded, making it a hotspot for criminal activity. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions. To protect your privacy, always use a VPN before accessing the dark web. Additionally, avoid sharing personal information and refrain from clicking on unfamiliar links.
Step-by-Step Guide: How To Access The Dark Web Using Tor Browser
Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it. It also adds a crucial layer of encryption before your traffic even enters the Tor network. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private.
The Dark Web Demystified: Myths, Facts And How To Stay Safe Online
You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. There are many legitimate uses for dark web services and communication. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources.
Accessing The Dark Web Securely
Dark web monitoring platforms provide secure communication channels for individuals seeking to expose information without fear of retribution. Additionally, the Dark Web serves as a haven for those in censored environments, offering access to restricted information and enabling the free expression of opinions. While Tor browsers are used to access the dark web, search engines play a crucial role in facilitating the browsing experience for users. Since Google and surface-level search engines don’t work in the dark web world, users often opt for these search engines that enhance their experience and accessibility on the platform.
Step-by-Step Guide: Access The Dark Web On Any Device

The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. While Bitcoin may arguably be the most popular cryptocurrency, it is not completely anonymous.
- If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more.
- PIA is popular in the USA because it offers servers in all 51 states.
- The Tor browser is the most popular tool, though you can also use Freenet, ZeroNet, I2P, and Riffle.
- The dark web is packed with potentially harmful content that puts you at risk, so a VPN is an important tool in keeping your identity and personal information safe.
Using Tor Browser FAQs
In some cases, fraudulent websites claim to be used by terrorist organizations such as ISIL. With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks. The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax.
- Encrypted, hidden sites that require special tools like Tor to access.
- You will have to manually configure it to connect to the Tor network.
- Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims.
- While the process is not overly complicated, it demands attention to detail, adherence to best practices, and an understanding of the risks.
- Tor is both a type of connection – with the extended relays – and a browser.
How To Access The Dark Web Safely: A 2025 Beginner’s Guide
Everything you can search for and interact with through regular browsers is part of the surface web, but much of the internet’s data is hidden below this easily accessible layer. This makes it really appealing for those who want to avoid unnecessary surveillance or who need to communicate without fear of oppression or governmental retaliation. However, if you’re planning to spend any time exploring the dark web, it’s crucial you take the necessary precautions to keep your device, your data, and yourself safe. Securing a VPN and choosing your overlay network has you in the final stretch for accessing the dark web safely. The final step before you can start browsing with relative peace of mind is to conduct an IP leak check. Because VPNs offer users anonymity and mask their actual location, they’re also effective tools for accessing geo-locked services.
There are plenty of services that offer a VPN over onion feature, which will keep you secure and private online. The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. Dark web browsing is not as simple as regular web surfing, but there are some tools you can use to chart your journey.
For Using The Internet Anonymously
The dark web is a playground for hackers, cybercriminals, and people with nefarious objectives. We strongly advise you against visiting it, even if your intentions are good. Contrary to a widespread misconception, the dark web is a tiny part of the web. According to Recorded Future research1, out of 55,000 onion domains discovered, only 8,400 have a live site. In this article, we will unpack everything you should know about what the dark web is, how it works, how to surf it safely, and more. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences.
Other search engines like Haystak boast millions of indexed pages and advanced filtering options. However, none provide the same coverage or reliability as surface web search engines, so users often rely on forums, directories, and community recommendations to find trustworthy sites. The Dark Web is also known for hosting illegal and explicit content, including child exploitation material, snuff videos, and other highly disturbing or illegal material.


