However, it seems to place a considerable amount of security risk on its users, given its lack of support for XMR, use of static BTC addresses, and absence of mandatory PGP encryption or 2-FA. Despite these concerns, MGM Grand has been running smoothly without any interruptions or downtime, amassing a significant user base. Overall, the MGM Grand is a noteworthy darknet market that presents a distinctive amalgamation of advantages and limitations. Its “2.0” site design suggests a readiness to cater to a novel audience of mobile device users, yet it lacks several fundamental functionalities that are expected of contemporary darknet markets.
- Sign up for free credit monitoring to get alerted when there are unexpected changes in your credit report, which could help you quickly respond to some types of fraud.
- It takes time to get the secure setup, which is described in the DNM bible, working.
- ASAP drives 25,000+ listings and $4M monthly across BTC, XMR, LTC, and USDT, holding a 7% share.
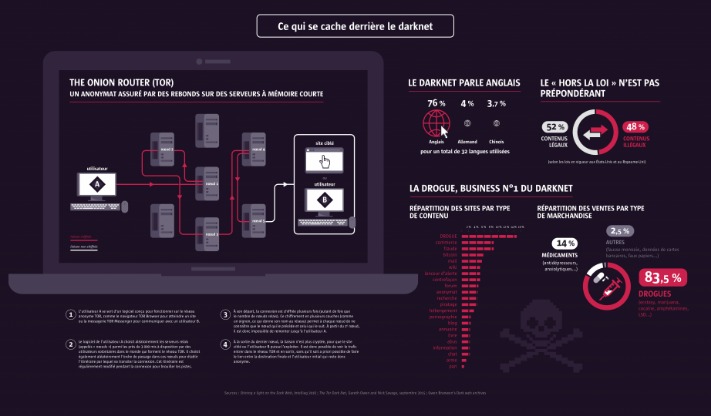
- So, is the dark web a lawless underworld or a misunderstood frontier for privacy and free expression?
The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. For example, you can only find your Facebook friends, photos, and other information by logging into your Facebook account and finding the information there. On the deep web, you can find such “private” information on web pages. But before we get into that, it’s important to understand the differences between the surface web, deep web, and dark web.
What Are Darknet Markets? Complete Guide
If you are curious about accessing the deep web, you are likely already using it daily through pending website redesigns, blog posts under review, and pages accessed during online banking. These pages are hidden for various reasons and do not threaten your computer or safety. If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app. The mobile app uses DuckDuckGo as its default search engine and is supported by the Orbit framework to provide secure access to the Tor network. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android.
Tor Layers
In that climate, the dark web’s anonymity tools serve as a digital lifeline for journalists, whistleblowers and ordinary citizens who need uncensored information. Understanding these moving parts clarifies both the promise and peril of the dark web. The same relay system that shields whistleblowers also frustrates investigators; the same hidden addresses that protect dissidents can hide criminal storefronts. Mastering the postal‑route mechanics—and their limits—lets you weigh privacy gains against security risks before venturing into the hidden Internet. We provide expert tips and best practices for maintaining your anonymity, securing your connections, and protecting your personal information while browsing the dark web.
Dark Web Links Are Visible Only Via Tor Browser
- Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy.
- The sad reality is the fact that law enforcement agencies can’t track and prosecute perpetrators or even take down such content given the anonymous nature of the dark web.
- With all this data, your ISP could create a very accurate profile of you and link it to your IP address.
- This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement.
- Please read through the sections below to gain a better understanding.
- Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks.
Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites. This is below the surface web and accounts for about 90% of all websites. This portion includes academic journals, private databases, and other content hidden from the public for various reasons. This portion of the internet can be accessed using search engines such as Google, Bing, or Yahoo. It includes websites, databases, and other online resources indexed by search engines and is easily discoverable by users.
Experience The World’s Most Advanced Cybersecurity Platform
The use of digital signatures can also help verify the authenticity of users and transactions. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network. These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets. Be cautious, as the dynamic nature of hidden services means that many links may not work or disappear over time. Hidden services are exclusive to the Tor network, identified by domain names ending in .onion.
Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors. Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation. While the Tor network is designed to provide anonymity, it alone cannot guarantee your privacy or safety.
These legitimate media companies keep a presence on the dark web to help users who might, for a variety of reasons, have difficulty accessing their content on the open web. There is a significant risk that the government can target you for visiting a dark website, as many Tor-based sites have been taken over by police authorities worldwide. Even if a person does not make any purchases on illegal marketplaces like the Silk Road, custom software used by law officials can analyze activity and identify user identities. The dark web is a hidden part of the internet that requires a special browser like the Tor browser to access it. Normal search engines like Google and DuckDuckGo don’t index this part of the web due to its illegal nature. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news.
That’s why it’s best to always take additional privacy measures, such as using a VPN, and follow safe browsing practices. It’s easy to think of the dark web as the black market of the internet, a secret corner where hackers gather, leaked personal data floats around, and pirated downloads of every kind are up for grabs. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web. Internet providers and websites can detect when Tor is being used because Tor node IPs are public.
Use Secure Communications
The dark web is a section of the Internet not searchable through traditional search engines, where privacy and anonymity reign. It is notorious for illegal transactions and activities such as drug trafficking, arms dealing and identity fraud. It also provides a safe haven for whistleblowers, journalists and those seeking free expression under oppressive regimes.
Darknet Access Guide
But it also contains other news and religious sites, private discussion forums, and medical records. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search.
Award-winning journalist Evan Ratliff spent nearly five years piecing together the uncommon story. The Goodreads community has responded well to the riveting account of a crime boss with thousands of positive reviews, and it’s no secret why the book tops our list. Interestingly, the man behind it pulled the strings from a laptop in Manila. A reclusive programmer turning criminal genius is certainly not your regular life cycle of a crime lord. It took a betrayal within his network for law enforcement to catch him.

Before delving into the specifics of darknet search engines, it’s essential to grasp what the darknet actually is. Contrary to popular belief, the darknet is not an entirely illegal space; it is a subset of the deep web, accessible only through specialized software like the Tor browser. The darknet is renowned for anonymity and privacy, attracting users who seek to evade censorship and surveillance. MGM GRAND Market is a darknet marketplace known for specializing in high-end counterfeit items, luxury goods, stolen financial data, narcotics, and hacking tools. Positioned as a premium platform, MGM GRAND Market emphasizes rigorous vendor screening and advanced encryption measures. The marketplace attracts users seeking high-value products and maintains an upscale reputation within the darknet community.
While MGM Grand is known for its user-friendly interface and mobile device accessibility, it’s not designed for beginners. Users are advised to maintain optimal operational security when placing any type of order on the market. It orientates itself on OpSec best practices and, if exactly followed, will greatly minimize the risk of you getting caught. There never will be 100% security, but with the help of the buyer’s DNM bible you can make it extremely hard and not worthwhile for law enforcement to catch you. Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random.
When using the Tor network, avoid accessing your regular browser or any site that could link back to your real identity. Mixing these activities can jeopardize your anonymity and expose your personal information. As these marketplaces flourished, they drew the interest of law enforcement. Silk Road’s takedown in 2013 fueled both fear and fascination, marking a high-profile enforcement milestone. However, it didn’t close the chapter on the dark web but, instead, opened the gates for many imitation sites. The subsequent captures of dark web operators resulted in a constant cat-and-mouse game, further embedding the idea of lifestyle communities within the web’s shadows.