This hidden part of the web carries several illegal activities, including drug and weapon dealing, pornography, private data, and more. Cryptocurrency activities, discussions and communities, and even academic resources further populate this hidden corner of the internet. However, it is crucial to recognize the dual nature of the Dark Web, understanding that while it has legitimate uses, it also harbors risks and associations with unlawful activities. Users navigating this space should exercise caution and be aware of the potential legal consequences tied to specific content and transactions.
Secure Your System And Mental Well-being
Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. The subreddit r/deepweb is a good starting point for asking more experienced users about how to search the dark web and deep web for the content you want. Lastly, The Hidden Wiki is a collection of dark web links — but the links may not work and can lead to dangerous websites. Tor is a web browser that lets you stay anonymous online or access the dark web.
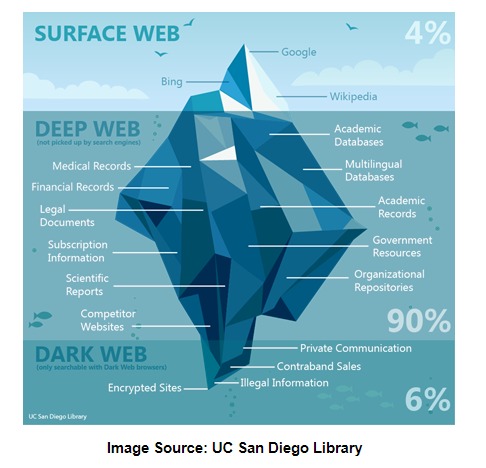
- It encompasses public domains such as websites, social media platforms, news sites, and online stores—content accessible to anyone with the help of the internet and a web browser.
- The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet.
- We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites.
- Similar to Firefox and Waterfox above, Brave is not a dedicated dark web browser.
- The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content.
How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo
Terrorist groups have used the dark web since its inception due to its anonymity and lack of regulation. The dark web provides these groups with chat platforms to inspire terrorist attacks and ‘How-to’ guides to teach people how to become terrorists and hide their identities. The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax. Some websites monitor and analyze the dark web for threat intelligence. The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity.
Due to the lack of regulations on the dark web, you are vulnerable to cyber threats anytime you visit. These risks can be avoided when you are well-informed and know how to protect yourself against them. Freenet is another Tor alternative, but more of an anonymous place for peer-to-peer content sharing. Users can form their own private groups for content sharing, called darknet mode. Or, they can use opennet mode to be randomly assigned to other peers on the network. Like I2P, it uses a distributed network database for added assurance against cyber attacks.
When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies. The dark web, however, requires special software to access, as explained below. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted.
Is Tor Enough, Or Do I Also Need A VPN?
That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. You can conduct discussions about current events anonymously on Intel Exchange.
Tor shares similarities with VPNs and proxy servers — all of these tools allow anonymous browsing. Tor can be used together with a VPN to provide overlapping layers of privacy and anonymity. The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and let you access the dark web. On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing.
Do I Need A VPN To Access The Dark Web Using Tor?
- He holds a bachelor of arts degree from the University of Washington and is now based in Boston, Massachusetts.
- Always remember, your safety online depends significantly on personal responsibility, informed decisions, and proactive application of security tips.
- In this guide, we’ll explain what the dark web is, how to access it safely, and why using a VPN (Virtual Private Network) with Tor is essential for anonymity.
- This app connects to the Tor network, allowing you to visit .onion sites.
And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing. As such, you should exercise caution when accessing any unofficial dark websites. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing.
It’s online and you can access it but your friend or family can’t. This is usually done to prevent tracking and website shutdowns typical for this part of the internet. The trick with these onion websites is their accessibility, which is made possible only with Tor. Tor is an abbreviation for The Onion Router and now, we can see why.
Find Trusted onion Sites
To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. You won’t be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service.
Using Tor Browser: The Final Step To Get On The Dark Web
But with the NSA setting up fake exit nodes, and growing concerns about the overall security of the network, you may need a VPN as well, if you want to ensure your privacy. Lastly, navigating the Dark Web also carries legal risks, as unintentional engagement with illegal platforms or content can lead to severe consequences. Maintaining compliance with legal and regulatory standards is essential for businesses operating in this space. Brandefense’s solutions not only detect risks but also provide a framework to ensure that your activities remain within the bounds of the law, protecting both your brand and your reputation.
Let’s unpack the steps and safety measures you’ll need for this expedition. I’ve put together detailed guides on how to access the dark web safely on both Android and iOS. I also share essential tips for staying secure there — personally, I always use a VPN for added privacy since Tor isn’t completely secure on its own.

Simply copy the URL of the site you want to visit, press Enter, and you’re all set. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information. This is where a VPN comes in, and a reliable VPN like NordVPN (read our NordVPN review here) can do wonders for you. We can say the same about private networks belonging to companies and other entities.

Disabling JavaScript and avoiding personal logins or revealing identifying details can further reduce the risk of being tracked. However, remember that nothing is foolproof, so always exercise caution when exploring the dark web. To ensure your traffic is properly routed through the Tor network, you’ll also need to install Orbot, which helps secure and anonymize your connection. When using Tor, your traffic will never reach its intended destination directly, as it would on surface web browsers. Instead, it is funneled through different ‘nodes’ – other user’s computers – before coming out the other side.

Using The Tor Browser
This portion of the internet can be accessed using search engines such as Google, Bing, or Yahoo. It includes websites, databases, and other online resources indexed by search engines and is easily discoverable by users. Cybercrime services, such as hacking tools and stolen databases, are available for hire, creating a marketplace for illicit online activities. Dark web monitoring platforms provide secure communication channels for individuals seeking to expose information without fear of retribution.


