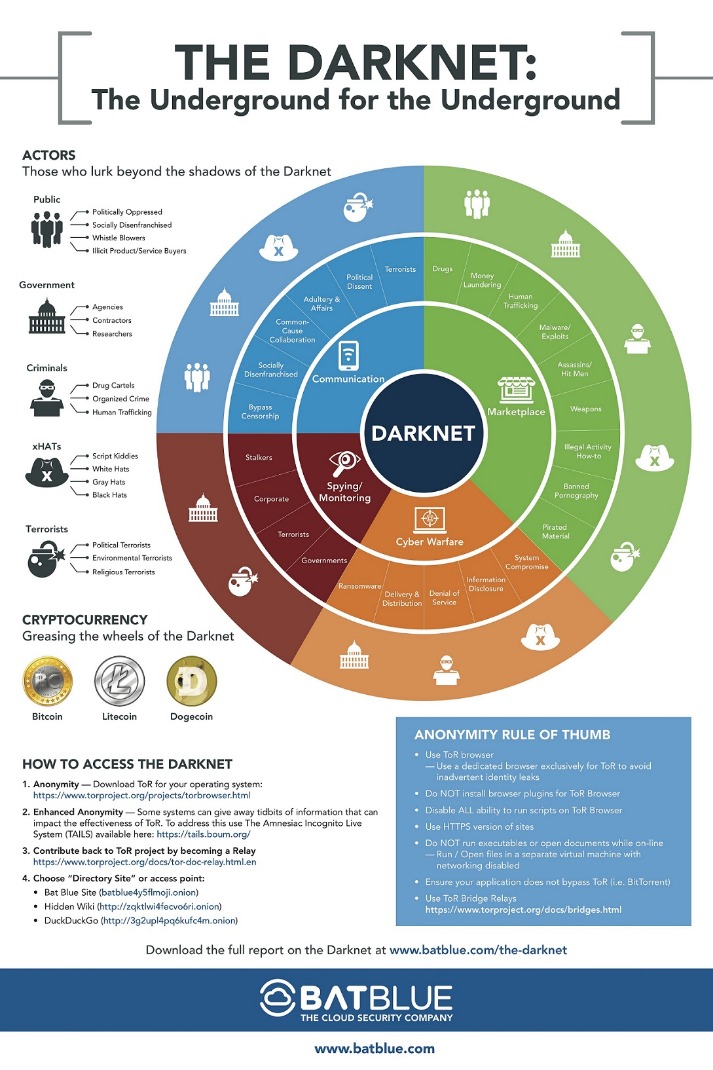
The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. Cluster 3 thematic focus is Machine learning, Social media, and Artificial intelligence related to the Darkweb. Machine learning and artificial intelligence techniques can analyze large amounts of social media data to identify patterns and trends related to the illicit drug trade and drug trafficking in the Darkweb.
Five datasets were used to characterize the evolution of these attacks and their impact on global Internet traffic, Darknet scanning activity, active probing, global DDoS attack victims and incidents, and local ISP impact. Authors 58 present a survey on the Darknet, a method for passively observing Internet activity and cyber-attacks. They define and characterize the Darknet, compare it to other monitoring systems, and report on case studies. They also identify research gaps in Darknet technologies and find that Darknet projects are distributed in one-third of the global Internet. The authors find that computer worms and scanning activities are the most common threats investigated through the Darknet, but DDoS amplification and spoofing activities are understudied. While the telescopic view of Darknet activities is useful, a microscopic view of the Tor network’s hidden services was attempted 59.
- Additionally, escrow services act as intermediaries, temporarily holding funds until the buyer confirms the transaction, reducing fraud risks.
- In addition, mainstream search engines also track your searches and collect personal information.
- Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity.
- Addressing this issue, researchers 7 have successfully demonstrated the use of LDA (Latent Dirichlet Allocation) and a non-parametric HMM (Hidden Markov Model) to spot anomalous behaviors.
As Eurasian narco-DNMs continue to battle for market supremacy, the informed prognosis on the Russian dark web is a grim, especially for user safety, according to Telegram darknet chatter. “The absence of a monopolist with simple and understandable rules will lead to a deterioration in the quality of the goods. This, in turn, according to narcologists and darknet analysts, will greatly increase the likelihood of death when using illegal substances,” said a post authored on a Telegram channel widely circulated within the Russian darknet community. Upon inspection, the main difference with Anon Market is their vast catalog of pharmaceuticals, specifically prescription drugs. In the image below you can see an array of pharmaceuticals currently for sale at the time of writing. Anon Market, a new underground dark web marketplace popped up after the closure of Hydra.
The criminal groups that developed the malware gets a cut of the affiliates’ earnings, typically between 20% and 30%. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. The growth of Huione Guarantee shows that while dark web drug bazaars may have once made the headlines, the cyberscam business is considerably more profitable than narcotics.
The Evolution Of Dark Web Marketplaces
This market is not open to the general public and is subject to a thorough vetting process to ensure its security. In fact, WeTheNorth is more of a private club than an open market – something its operators want. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. Our team searched the dark web and put together a list of the most active dark web marketplaces in order to assist you in monitoring illegal trade of products, cybercrime activity, and dark web trends in the dark web space. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement.
Set Up Tor Browser
The community remains online and available for drug sellers 24/7 despite repeated DDoS attacks. Jacob Riggs is a senior cyber security professional based in the UK with over a decade of experience working to improve the cyber security of various private, public, and third sector organisations. His contributions focus on expanding encryption tools, promoting crypto-anarchist philosophy, and pioneering projects centred on leveraging cryptography to protect the privacy and political freedoms of others.
Stolen Data And Identity Theft
Digital forensics helps in tracing digital footprints back to their sources. Another significant bust was the Kingdom Market, which was brought down in late 2023. The risk of data breaches is higher than ever for businesses, potentially leading to financial loss, reputational damage, and legal consequences. Individuals are also at risk, as their personal information can be exploited for identity theft or sold multiple times over. After all, criminals are getting more creative and professional by the day, running their operations like businesses with customer service and even reviews.
14 Darkweb And Phishing, Cybercrime
Bibliometric analysis serves as a method to discern patterns, themes, and shifts within a particular realm of research. It also facilitates the identification of the most prolific institutions, authors, and countries engaged in that research domain. Researchers employ bibliometric analysis to examine subjects and nations in their studies 30, 31, 32,33. One of its notable advantages is its transparency, reliability, and ease of replication.
The Hidden Wiki
Highly trained specialists take reports from both the public and law enforcement agencies on more than 400 laws enforced by ICE. A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
US Government Seizes Approximately 145 Criminal Marketplace Domains
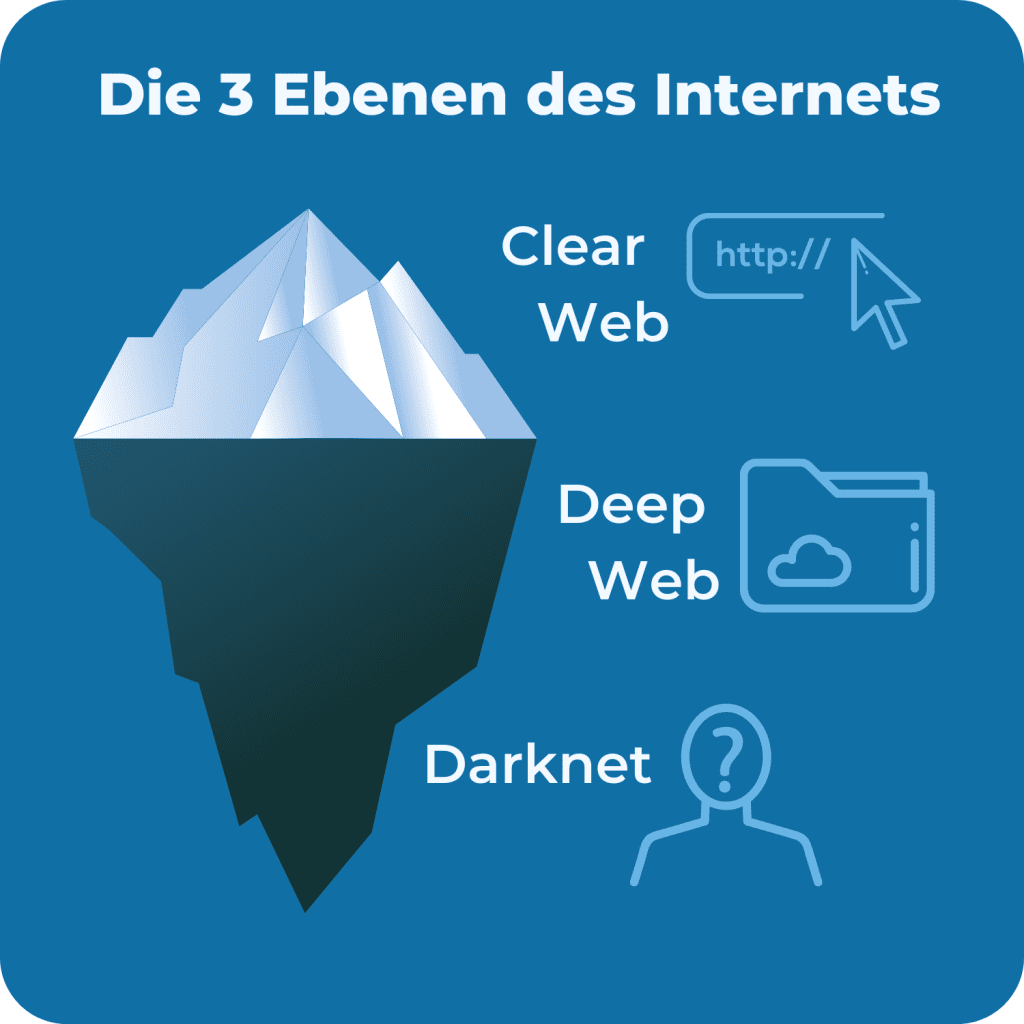
As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked. There’s no denying that the dark web is well-known for illegal activities. Besides, not everyone wants to purchase an illegal item – some want items anonymously. The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion. The hidden part of the internet is the larger portion that features over 95% of the entire internet.
What Is The Cost Of Stolen Data On The Darknet Market?
- According to the indictment, Parsarad, 36, of Tehran, Iran, launched Nemesis Market in or around March 2021.
- Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen.
- The website has a great design and a clean and organized interface that is easy to use.
- These sources are all journals and have the highest citations per publication ratio.
- In both cases, this activity is coming from cybercriminal or semi-criminal elements, which are likely driven not just by their personal interest, but the direction from a third-party.
- Upon inspection, the main difference with Anon Market is their vast catalog of pharmaceuticals, specifically prescription drugs.
For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
Pharmacies In Mexico Are Shut As Authorities Crack Down On Fentanyl-tainted Pills

Fill out the form to speak with our team about investigative professional services. Many people overlook the importance of regularly changing the WiFi network password. The US government created the dark web to help its spies communicate and exchange information securely. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails.

Data, whether in the form of simple user credentials and passwords or proprietary trade secrets, can fetch quite a price on the dark web. The dark web might not interest you, but its denizens might have already cast their eyes on you, so approaching all of your business processes from a security-by-design perspective is essential. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment.