The U.S. government’s Naval Research Laboratory developed Tor for members of the U.S. intelligence community to use the Internet without risk of identification. While there are many legal activities on the dark web, such as protecting online privacy or staying anonymous for journalists and activists, there are also potential risks in terms of illegal activities. Despite these challenges, law enforcement agencies continue to adapt and develop new strategies to combat the dark web’s criminal underworld. While dark web search engines can help users find information, they come with their own set of challenges. Search results can be repetitive and irrelevant, and link lists may lead to timed-out connections and 404 errors.

How Does The Dark Web Work?
Tor Browser is a tool created and maintained by a non-profit privacy group, and it uses onion routing to repeatedly encrypt data and route it several times before it gets to its expected destination. Those layers of encryption and routing activity help to anonymize your movements. Keep in mind though, even the Tor browser isn’t an infallible privacy solution.
Download Tor Browser
It comprises websites, resources and services that aren’t indexed by regular web crawlers. The websites are hidden in layers of encryptions and use dot (.) onion domains, which is why they are called onion sites. The dark web is accessed with the help of special software like the Tor Browser. Download and install Tor first, and optionally a VPN for added security. After that, browse .onion websites through dark web directories or search engines, being careful to follow proper security practices.
Should I Be Worried If My Information Is On The Dark Web?
However, it also provides a cover for illegal activities, such as cybercrime and the distribution of malware. People use the dark web for both good and bad, but generally speaking, it’s used for activities requiring a high level of anonymity. Activists, journalists, and privacy seekers use it for secure communication, bypassing censorship, or protecting their identities, while criminals may use it to network or sell stolen or illegal goods.
- To get on the dark web, you need a browser built for the job, and the best in the business is Tor.
- This anonymity also allows them to access websites and services that may not be available on the surface web, further protecting their privacy.
- However, while using Tor itself is not illegal, some illegal activities can occur through the network, such as the distribution of child pornography or the sale of illegal drugs.
- If your phone number is on the dark web or you suspect it is, you should set a security PIN with your cellular network, monitor for suspicious activity, and stay alert for scam messages or calls.
- For example, the deep web is often a platform used by political activists who own a blog.
- When people go on about the so-called dark web, they’re usually talking about onion sites, which aren’t searchable via Google or accessible via standard browsers.
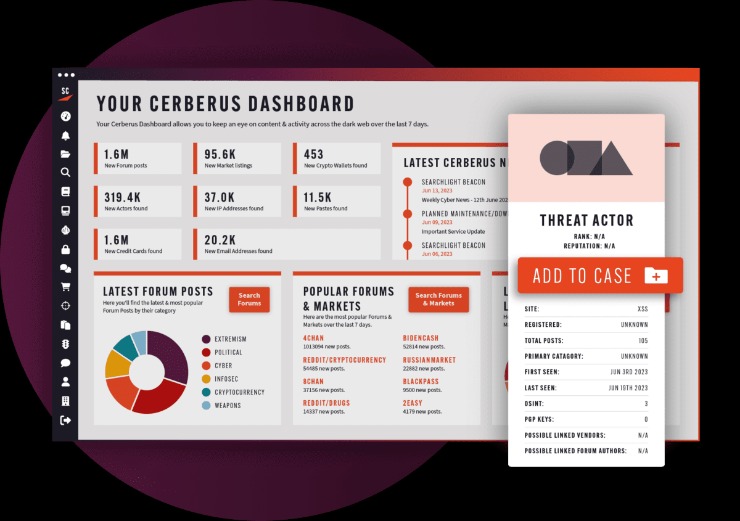
Cyble Titan Endpoint Security
Individuals can scan the dark web or sign up for a monitoring service. These dangers can interrupt business operations, defraud a company and devalue a brand’s integrity. The best way to avoid these dangers is to avoid using the dark web entirely. But if this is not possible, it’s important to employ reliable security measures, including antivirus software, and to access dark web sites only via a VPN. In addition, the Tor browser, Tor applications and operating systems should be kept up to date, and companies might want to limit or monitor their use. That said, a significant chunk of U.S.-based activity on the dark web still revolves around illegal marketplaces—selling things like stolen data, counterfeit documents, and even drugs.
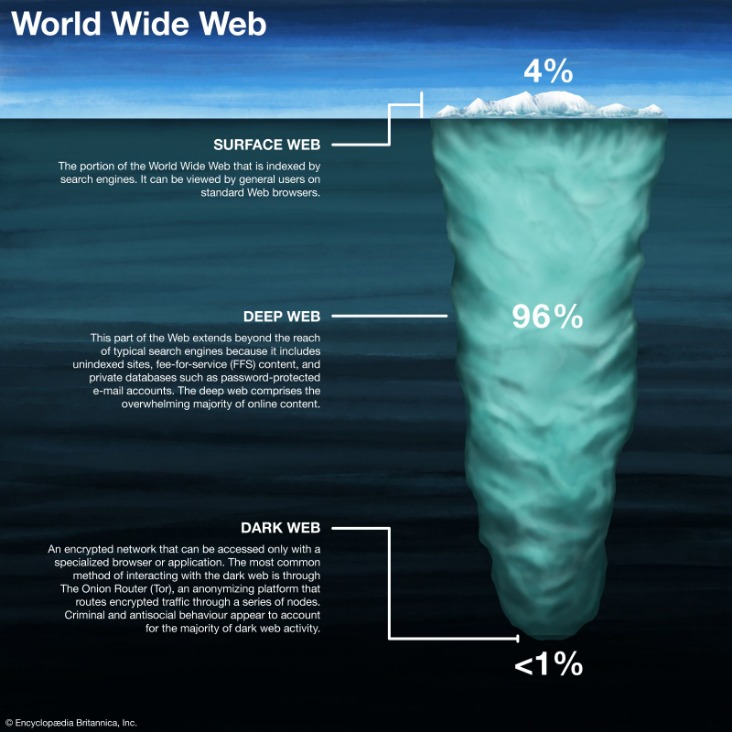
Anything beyond that index, which is hidden behind a password or any software, is known as Deep Web or Dark Web. The difference between the deep web, dark web, and surface sites is essential for organizations that assess the threats that come from the internet. As a result, ‘Dark Web’ is often used interchangeably with ‘Deep Web,’ but in fact, they are two different things. The “Surface Web” comprises the WWW sites that are searchable using search engines such as Google or Bing.

Use A Dark Web Search Engine
The dark web itself is neutral; how people use it is what makes it good or bad. The deep web is crucial for maintaining privacy and security online, as it keeps sensitive information away from the prying eyes of the public and search engines. While the term “deep web” might evoke images of hidden, secretive content, most of it is just routine data stored on private networks. Sites on the surface web (or open web) are those visible to average users without the use of Tor or any other special browsers or software. Sites on the surface web are also indexable and can be easily found using search engines.
What’s The Difference Between The Deep Web And The Dark Web?
If you want to observe the lawless sides of the internet from afar, check out YouTube videos of dark web explorations, like this one from John Hammond, to satisfy your curiosity. This adds an extra layer of protection to thwart tracking and monitoring in case the traffic passes through a compromised exit node. Beyond DuckDuckGo, other options have failed to keep up with the evolving landscape. Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s. Though most volunteers mean well, others are malicious actors and surveillance agencies.
This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.
Ironclad Cybersecurity
Valentina Bravo is a managing editor at Cloudwards with a rich background in technology topics, particularly productivity tools and online security. She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience. Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks.
Instead, the dark web uses information from individual email or social media accounts, databases, and documents to give users access. Over the years, the Dark Web has gained a certain level of notoriety due to its association with illegal activities, including the trade of illicit goods, hacking services, and various forms of cybercrime. Law enforcement agencies worldwide have grappled with the challenges posed by the Dark Web, attempting to balance the need for online privacy with the necessity of combating criminal activities. If you are looking to read combating crime on the dark web online, many resources and platforms are available that shed light on the ongoing efforts to curb the growing threats of cybercrime. Unlike the surface web, which can be indexed by standard search engines, the dark web exists on encrypted networks and hosts websites with random, complex URLs. This layered encryption and anonymization make it difficult for authorities or outsiders to trace activities or identify participants.
Use a separate wallet for dark web transactions to further protect your funds. Avoid using the same password across multiple sites since it increases your vulnerability if one account is compromised. You can also use a password manager to generate and store complex passwords with ease. Get daily tips, tricks, guides, and special offers delivered right to your inbox. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs.
Malicious software — i.e. malware — is fully alive all across the dark web. It is often offered in some portals to give threat actors the tools for cyberattacks. However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web. As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online. Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites. But of course, these benefits can be easily extended to those that want to act outside of the constraints of laws in other explicitly illegal ways.


