A dark web market is an online marketplace that operates on the dark web, a hidden part of the internet that’s not accessible through regular search engines or browsers. In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization. You won’t find drugs here, but you will find tons of credentials, RDP access, CVVs, and records stolen using malware.The platform works with data collected by well-known malware such as Lumma, RedLine, Raccoon, Vidar, and Aurora. Some of the best-known names include Abacus Market, Russian Market, and BriansClub, all with thousands of illegal items available.Despite closures by authorities or the typical “exit scams” (when a marketplace disappears with all the money), these sites continue to pop up. Passwords, tokens, session data, and API keys are valuable commodities on marketplaces.
Why People Use Dark Web Marketplaces

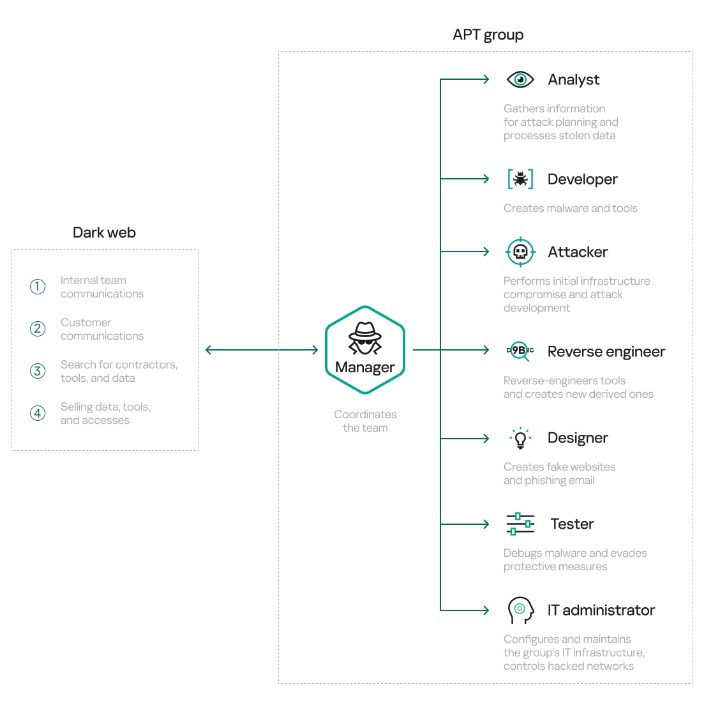
The dark web is a thriving marketplace where illicit goods and services are bought and sold by actors that range from nation-state threat groups to teenage hackers. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. The darknet marketplace is home to a plethora of illegal and legal activities. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions.
Signs Your Cybersecurity Framework Needs Rebuilding
With fast order processing, product reviews, and secure payments, it’s a trusted platform for cannabis enthusiasts in the darknet space. City Market is a modern darknet hub designed to emulate the flow and structure of a digital metropolis. With a reputation for stability and stealth, it remains a preferred destination for high-level darknet activity.
Mysterious Elephant: A Growing Threat
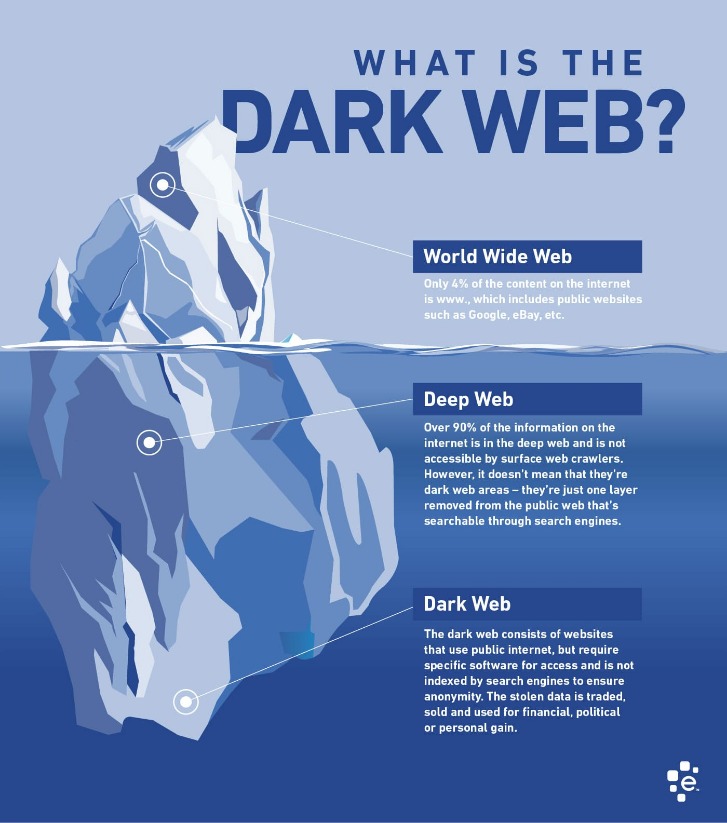
However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. The concept of darknets emerged as a response to concerns about digital privacy and government surveillance. Understanding darknets is essential for organizations to recognize and combat the threats they pose. Why Threat Intelligence Platforms Matter Now Traditional firewalls can’t protect against stolen passwords. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation.
This suggests that law enforcement responses to cryptomarkets result in continued security innovations, thereby making markets more resilient to undercover law enforcement efforts. Many sites use Bitcoin multisig transactions to improve security and reduce dependency on the site’s escrow. Uptime and comparison services provide sources of information about active markets as well as suspected scams and law enforcement activity. From then on, through to 2016 there was a period of extended stability for the markets, until in April when the large Nucleus marketplace collapsed for unknown reasons, taking escrowed coins with it. The market owners set up a phishing website to get the attacker’s password, and subsequently revealed collaboration between the attacker and the administrator of Mr Nice Guy’s market who was also planning to scam his users. In March 2015, the Evolution marketplace performed an “exit scam”, stealing escrowed bitcoins worth $12 million, half of the ecosystem’s listing market share at that time.
The History Of Darknet Marketplaces
“With Huione Guarantee, the primary thing being sold is actually laundering of the proceeds of online scams,” Robinson alleges. The website for USDH, the Elliptic researchers say, describes it as “not restricted” by regulators around the world and says that it “avoids the common freezing and transfer restrictions” that can be applied to other cryptocurrencies. Preventing it from operating would have a significant impact on online scams and would have an immediate beneficial effect on victims and potential victims.” “What platforms really do is help scammers to scale up their operations, and it’s really enabled the industrialization of online scams,” says Tom Robinson, Elliptic’s cofounder and chief scientist. At the same time, the platform is offering more services than ever, including launching its own messaging app, stablecoin, and cryptocurrency exchange.
STYX is a great example of a ‘new model’ market with a searchable structure and trusted vendor processes, which helps buyers quickly filter for fresh data. Unlike older drug-oriented markets, STYX looks more like a specialized cybercrime exchange than a bazaar. Its listings focus on stealer logs, initial access and financial credentials, making it highly relevant for financial security professionals.
The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. Even passive activity on these sites can contribute to criminal networks.
Hydra Market 2015 2022 Europe’s Drug Giant
Traditional firewalls and antivirus programs no longer suffice, especially when attackers operate with military-grade tools sourced from the dark web. Stolen data remains a top-selling commodity, with new breaches appearing almost daily. Such models ensure that the market remains community-controlled and resilient to outside interference. Smart contracts manage vendor-buyer interactions, and blockchain-based dispute systems replace traditional moderators. These platforms run on peer-to-peer protocols without central servers or administrators. Global law enforcement agencies face mounting challenges in tracking and dismantling dark web operations.
Dark Web Marketplaces

Atlantis, the first site to accept Litecoin as well as Bitcoin, closed in September 2013, just prior to the Silk Road raid, leaving users just one week to withdraw any coins. It has been considered a “proto-Silk Road” but the use of payment services such as PayPal and Western Union allowed law enforcement to trace payments and it was subsequently shut down by the FBI in 2012. Since the year 2000, some of the emerging cyber-arms industry operates online, including the Eastern European “Cyber-arms Bazaar”, trafficking in the most powerful crimeware and hacking tools.
- A wide variety of goods and services, from hacking to designer knockoffs, are available on the dark web.
- These hidden e‑commerce sites run on Tor hidden services with .onion domains, using cryptocurrency payments (often Bitcoin or privacy coins like Monero) to conceal identity.
- Understanding how dark web marketplaces work is no longer niche knowledge — it is central to modern cybersecurity.
- Although each marketplace may have its own specialty, most focus on a few well-known categories.
- Its 13,000+ users and 1,100+ vendors prioritize speed and escrow security in darknet trading.
- What other bounty might be found in the CyberBunker data, now that investigators have its entirety?
Set Up Tor Browser
Coincidentally, those admins carried out an exit scam first stealing roughly $11 million in user escrow funds in mid April. Unlike overt seizures, Dream’s shutdown was an exit by administrators, a pattern sometimes seen when market owners bail out. It specialized in narcotics, stolen data credit cards, credentials and contraband.
Darknet Markets List
It offers over 20,000 listings ranging from narcotics and forged documents to hacking software and fraud tools. By 2025, it is already a key player for those involved in the business of data theft and trafficking. With constant updates and new providers entering the market, Exodus is positioning itself as a major player in the digital underworld of credential theft. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. Today, they are still active and have evolved considerably in terms of security and sophistication. To access them, you need to use special browsers like Tor, which allow you to browse anonymously.
Best Free Firewall Software In 2025
Darknets rely heavily on Tor (The Onion Router), a privacy-focused network designed to conceal users’ identities and locations. They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity.