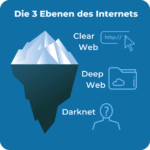
On the other hand, those stats reveal that around 40% of the dark web is not actually illegal. In fact, research performed at the University of Kent in 2015 revealed that 57% of the dark web hosts illicit material. The dark web is a hive for criminal activity due to its anonymous nature and the fact that it is extremely hard to track down anybody who accesses it. The dark web is a part of the deep web that can be accessed anonymously using Tor browser. This is also why it is essential to use strong passwords to protect any information stored on the deep web. Instead, Tor Project recommends iOS users to connect using the iOS Onion Browser app.
In fact, this hidden web is so large that it’s impossible to discover exactly how many pages or websites are active at any one time. Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here. Remember, always prioritize your online safety and exercise caution when accessing the dark web.
Which Is The Best Free VPN For Tor?
Surfshark works well with streaming platforms and is able to access geo-restricted content from the likes of Netflix, HBO, Hulu, and Disney+. The company operates a strict no-logs policy and protects internet traffic using AES-256-GCM encryption together with a SHA512 authentication hash and 2048-bit DHE-RSA key exchange. It has a large network of secure servers, the ability to keep connections private, and apps that are rich in security features. In 2018, someone gained access to a third-party data center in Finland.
How To Access The Dark Web Or Deep Web Using Tor
Bitcoin is widely employed in Dark Web transactions because of its anonymity and also because banks and governments do not control it. Though Bitcoin is not perfectly anonymous, with proper use, it can facilitate online transactions anonymously without revealing the identity of the parties. Most sites on the Dark Web use the Tor encryption tool to hide their identity.
Download And Connect A VPN
Google’s purpose is to show the most relevant information to all of its users quickly and easily. It includes media and archives which cannot be crawled and indexed with current search engine technology. The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search. Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address.
Tor Over VPN Or VPN Over Tor? What To Use For Your Phone?
With the right knowledge and precautions, you can explore the dark web with enhanced privacy and security. Ultimately, the dark web can be a place of great intrigue, but it’s essential to approach it responsibly. Regularly update your software, use encryption methods, and stay informed about the latest security practices to mitigate potential threats. However, using the dark web requires caution and adherence to responsible online practices. Remember, while these tips can significantly enhance your safety and security, there is no foolproof method to eliminate all risks. Always exercise caution and stay informed about the latest security practices to mitigate risks effectively.

Like Freenet, I2P has its own dark web that consists of websites ending in b32.i2p. It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity. I2P, or the Invisible Internet Project, is an anonymous network layer to facilitate secure and private communication among its users. It focuses on privacy, censorship resistance, and ensuring free access to content. For instance, your email inbox, online banking account, or a company’s internal database resides in the deep web. Unlike the surface web, you can’t access deep web resources directly through a search engine; they require login credentials or special permissions.
However, there are also perfectly legal, safe sites within the dark web, like privacy-focused forums, marketplaces, and more. Some of them (the hardest ones to access) are situated in what is known as the dark web. Surprisingly, the U.S. government is usually cited as the creator of the dark web to allow spies to communicate with each other anonymously. No one truly knows the size of the dark web, but some estimate that it accounts for just 5% of the total internet. The dark web is quite small when compared with the internet as a whole.
This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. There are numerous directories that host .onion links and websites, but you should always exercise caution. VPNs are also used for accessing geo-locked content hosted by streaming services. A step-by-step guide to safely accessing the dark web while maintaining your anonymity and security. Always prioritize your safety, practice good cybersecurity habits, and use your judgment when interacting with the content and websites you encounter.
Step 3: Connect To The Tor Network
A VPN encrypts your traffic as soon as you connect to it. This can expose your traffic and sensitive information. With this information, the ISP will know you’re on the dark web because Tor is mainly used for this purpose.
You’ll notice that some websites’ loading times are longer when using Tor. This time, you should do it, as you’re already hidden by NordVPN’s encryption. Everything you do is protected by NordVPN, vital to accessing the dark web and enjoying it privately. Now that your connection is active, it’s encrypted and untraceable by your internet provider.
Accessing The Dark Web Without Tor: Setting Up I2P And Hyphanet
Once connected to Tor, you’re ready to browse the dark web. Here’s a step-by-step guide to setting up Tails on a USB thumb drive and using it to access Tor. Accessing the Tor network through Tails OS (The Amnesic Incognito Live System) on a thumb drive is a highly secure way to browse the dark web anonymously. In this method, your traffic is routed through Tor before it reaches the VPN server, masking your IP address even from the VPN provider. However, keep in mind that the dark web is not organized like the regular internet. Once connected to Tor, you’re ready to begin exploring the dark web.
- To access the dark web, you will need the Tor browser, which provides the necessary anonymity and security.
- By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
- With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor.
- The process of onion routing takes your traffic, encrypts it, and bounces it among at least three relay points (or nodes), which makes it almost impossible to trace the source of the data.
- Within the dark web, there are various hidden websites, known as darknet markets, where illicit goods and services are bought and sold.
- Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web.
You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft. However, with the right security measures and cautious browsing, you can minimize these dangers. Your accidental visit to such sites can contribute to the perception of the demand, encouraging criminals to continue or expand their operations. Though the dark web offers anonymity for journalists and activists in oppressive regimes, it raises many ethical concerns. So, you risk being flagged or investigated for visiting certain sites, even without criminal intent. These tactics trick users into revealing sensitive information or paying for non-existent products.

Freelancing alongside these roles, his work has appeared in publications such as Vice, Metro, Tablet and New Internationalist, as well as The Week’s online edition. In this way, your browsing experience is made as anonymous as possible – if someone was ‘watching’ you, so to speak, all they’d be able to see is that you’re using Tor. No node can track the complete path the traffic has taken, and more importantly, neither can anyone who finds it on the other side. Traffic is relayed through three nodes each time it passes through the Tor network. When using Tor, your traffic will never reach its intended destination directly, as it would on surface web browsers. Accessing the dark web is easier than you might think – all you need is an onion and a bit of know-how…

It isn’t indexed by standard search engines such as Google or Bing. Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web. The dark web is filled with information theft from malware-infected users.
The Legality Of Accessing The Dark Web
The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines. You could consider the clear or surface web the “top” and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox. Here’s everything you need to know about this other internet, as well as how to access it.
What Is IPsec? The Definitive Guide For 2025
It’s a good idea to connect to a trusted VPN before you even open the Tor Browser to access the dark web. The Tor Browser is the safest and most trusted way to access the dark web. It also provides super-fast speeds, and its no-logs policy has been independently audited and confirmed — this way, you know it doesn’t store any user data. You need special tools to access the dark web, and the Tor Browser is the safest and most popular one.