With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor. It’s extremely rare and only useful in very specific cases, like if your VPN is only accessible through Tor. This method sends your VPN connection through the Tor network. If you’re serious about staying private on the dark web, the order in which you use your VPN and Tor Browser matters.
Step 2: Download And Verify The Tails OS Image
The encrypted data is sent through a series of network-based nodes called onion routers. The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them. The Tor Browser (“The Onion Router”) is a product of the Tor Project, which was founded on the belief that “internet users should have private access to an uncensored web.” If you are reading this, you’ve likely heard about how the Tor Browser can help protect your internet privacy and anonymity online. For this reason, many people prefer to use a VPN to encrypt their connection to the Tor network, thereby preventing their ISP from being able to detect that they are accessing the dark web. Users’ internet traffic is sent through an encrypted network of volunteer-maintained relays around the world.
Start Your Protection,
This unique browsing experience underscores the user\’s active role in navigating the intricacies of the Dark Web landscape. Unlike the direct route taken by conventional browsers, Tor employs a series of encrypted servers known as nodes, chosen randomly, to ensure both user and site anonymity. Well known for its emphasis on security and privacy, the Tor browser distinguishes itself from mainstream browsers like Firefox or Chrome.
This means your private information, location, and any communications you send are hidden and protected. A VPN automatically encrypts your data as soon as it leaves your device through the VPN server. The dark web is full of malicious actors, cybercriminals, and other people who are looking to prey on curious but unprepared dark web browsers. Before downloading your dark web browser, though, there are a series of safety precautions you’re going to want to take first. For instance, there are some organizations who employ the services of white-hat-hackers for a number of reasons.
- Surface web search engines can’t access the darknet, but specialized dark web search engines can help you find what you’re looking for.
- We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely.
- These sites are only accessible over the Tor network and are commonly used for privacy and anonymity.
- If you decide to venture into the dark depths of the deep web, make sure you’ve bolstered your device’s security with powerful privacy and security tools that can defend against dark web threats.
It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Because it’s not as safe as Tor over VPN.
MANAGED SERVICES
There are many excellent VPNs for the dark web, but my favorite is ExpressVPN because it’s the fastest on the dark web. A VPN also helps protect you from risks in the Tor network itself. A VPN adds that extra layer of privacy you need when browsing the dark web on Tor.
Roundup – Best VPNs For The Dark Web
Accessing the dark web is not illegal in the United States, but naturally, engaging in illegal activity while on the dark web can get you in hot water. There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto. Heck, I’m one of PCMag’s resident security experts, and I’m not playing around on the dark web just because I know how to. It’s the side of the internet that’s used for transactions and conversations that need to stay anonymous. Sites on the dark web can contain potentially catastrophic pitfalls in the form of illegal activity, phishing links, financial scams, and malware infections. As a freelance content writer, Stefan can break down complex technological topics, making them easily digestible for the lay audience.
In the deep net, web crawlers are blocked from accessing web pages to gather information for indexing, so the content remains hidden. Web crawlers index websites and services on the surface web, which are accessible via regular browsers. The websites are hidden in layers of encryptions and use dot (.) onion domains, which is why they are called onion sites. The dark web is part of the hidden web, which comprises non-indexed websites that are mostly used for illegal and illicit activity. The internet providers and websites can still see that you’re using Tor, as Tor node IPs are public. In a nutshell, the deep web is not illegal as it’s a network for privacy and security-conscious people.
Cryptocurrencies And Financial Anonymity
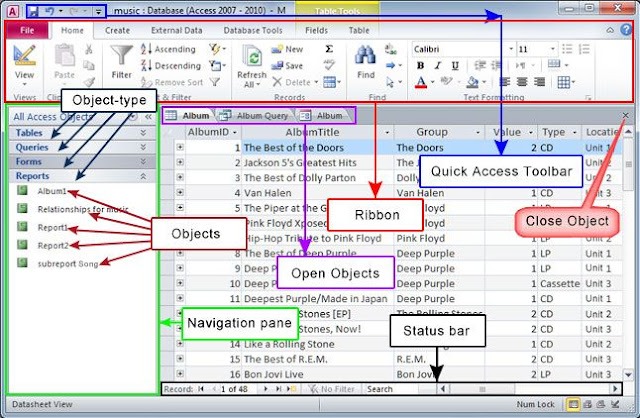
It isn’t indexed by standard search engines such as Google or Bing. Darren is regularly featured as a cyber-security expert in major media outlets including CBS Evening News, Fox & Friends, USA Today, ABC and Mashable. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. There are several whistleblower sites, including a dark web version of Wikileaks.
How To Access The Dark Web (Safely)
However, before you start your search, toggle the button beside “Onionize” to anonymize your session. Do your research beforehand and don’t click suspicious links. You can find some dark web directories on the surface web. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated.
Stick to tried-and-tested sites and do your best to avoid scams. Above all, it’s vital to go on the dark web carefully and sensibly. This internet space can be dangerous, but you can safely get on it by using a VPN and then connecting to Tor.
- We’ll also shed light on some of the legal uses of the dark web and show you how to access it securely in a detailed step-by-step guide.
- It operates on a separate network that anonymizes users by routing their traffic through a series of encrypted servers, making it difficult to trace activities or identify users.
- It encrypts data during transmission to avoid the risk of being eavesdropped.
- I2P can only be used to access hidden sites that are only available on the I2P network.
- There are simply too many risks, such as honeypot sites set up by governments waiting for you to submit your info and fake marketplaces and scam sellers who won’t actually send you the items you buy.
For example, we typed TechRadar.com into the address bar and accessed the website without any issues. To surf the web privately, you need to connect to the Tor network from your browser. Once complete, you can add Tor to your shortcuts menu for easy access. Since its public release, researchers have discovered various vulnerabilities in Tor, which have been quickly patched.
No node can track the complete path the traffic has taken, and more importantly, neither can anyone who finds it on the other side. Traffic is relayed through three nodes each time it passes through the Tor network. When using Tor, your traffic will never reach its intended destination directly, as it would on surface web browsers. Accessing the dark web is easier than you might think – all you need is an onion and a bit of know-how… This is the only way to ensure a maximally anonymous – as well as safe – browsing experience on the Dark Web. To access the Dark Web, you have to use a browser called Tor, also known as The Onion Router.
The dark web is only accessible through unique dark web browsers like Tor. Thankfully, it allows you to connect unlimited devices, which will be useful when exploring the onion links with many devices. Surfshark is a budget-friendly VPN with robust security features.
However, some Tor users do so to facilitate illegal online acts. DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers. We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention.