To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing.
Using The Tor Browser
Install Norton 360 Deluxe to help secure your device, block scams, and stay private online. Download Norton 360 Deluxe to help secure your device, block scams, and stay private online. That information can include checking and credit card account numbers, social security numbers, and other sensitive information.
Can I Use Tor To Browse The Surface Web?
Accessing the dark web sites isn’t safe and requires a user to go through several privacy measures to access it anonymously. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions.
- It is possible to navigate the dark web even though it doesn’t host user-friendly onion search engines.
- Law enforcement authorities regularly shut down illegal sites and reveal site visitors’ identities to try to deter others.
- Here’s how to access the dark web safely and anonymously.
- People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web.
- The VPN boasts bullet-proof 256-bit encryption, solid leak protection, a kill switch, a no-logs policy, and split tunneling to safeguard your online privacy and safety.
There are a lot of these sites across the dark web, which is why you have to be extra careful. Often, these sites are made to look just like real, trusted platforms, such as banks, social media sites, or email providers. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors. Firstly, it could jeopardize your anonymity if you submit any kind of personal information during a dark web browsing session. It won’t guard you against all of the many threats that exist on the dark web, from phishing scams to malware and malicious sites. It’s illegal to use the dark web for any form of criminal activity, like buying stolen goods, drugs, user accounts, and so on.
With any malware infecting your device, you can suffer horribly and come across data loss and, in the worst-case scenario, lose your device, too. Not only is it offered as a means for threat actors to launch attacks, but it is also prowling around looking for unsuspecting victims to infect. Some of the best dark web search engines include Grams and The Hidden Wiki. Although dark web search engines are available, keeping pace with their constant evolution is challenging, even for the best programmers. Safe access to the dark web requires a deep understanding of its risks. Therefore, activities within the virtual machine in no way impact your computer.

Always comply with local laws and use proper security measures. Darren is regularly featured as a cyber-security expert in major media outlets including CBS Evening News, Fox & Friends, USA Today, ABC and Mashable. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. There are several whistleblower sites, including a dark web version of Wikileaks. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious.
The major difference from the open web is that it is system admin — not the search engine — that can follow your activities. “On the deep web, you can assume that activities are monitored at the gateway. Mail providers Mailbox.org and Protonmail can also be accessed via an .onion link. Any internet traffic leaving the exit node is no longer part of Tor’s dark web.
The Future Of Cybersecurity Leadership: AI, Governance & Education Kevin Powers, Boston College
DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines. However, the vast majority of items found on dark web marketplaces are illegal or illicit. Books, video games, apparel and rare collectibles are some of the legal items you can buy on dark web commerce sites. A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense. This is because Tor traffic is usually unencrypted when it passes through the exit node. There’s evidence that law enforcement agencies in freer countries operate many exit nodes for monitoring and surveillance purposes.
How To Use Tor Browser Safely
Tor Browser masks your IP address and routes traffic through multiple servers. We’ll focus on secure, ethical practices tailored to cybersecurity professionals and IT leaders. In this guide, we’ll cover the dark web access guide, explain how to use Tor browser safely, and answer key questions like is it safe to browse the dark web. Always conduct your own research or check with certified experts before investing, and be prepared for potential losses.
Can My ISP See That I Am Accessing The Dark Web?
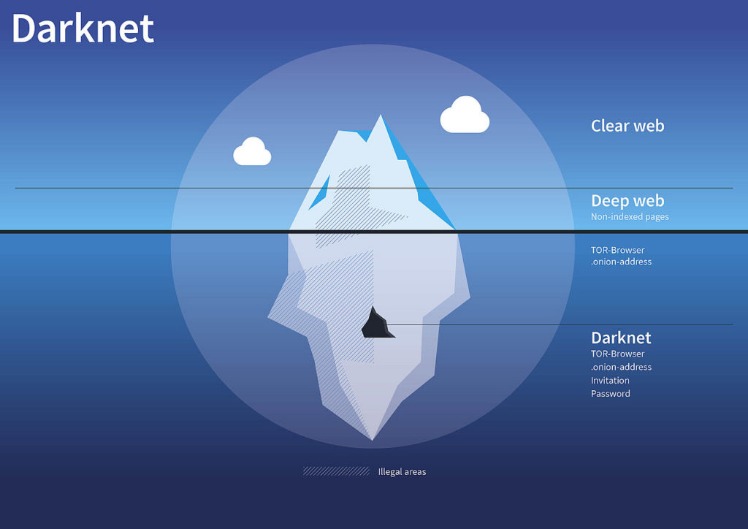
In most ways, the dark web resembles the clear web, but dark web sites often have a text-heavy, minimalistic design focused on anonymity and functionality. The dark web is a small, hidden subset of the deep web that requires special tools to access. Unlike the publicly accessible surface web, the deep web includes sites requiring login credentials but is still accessible via traditional browsers. Estimates suggest around 43% of dark web content and activity is legal, but finding it requires a specialized dark web search engine. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. This can include medical records, research papers, private forums, and networks.
Signs Your Cybersecurity Framework Needs Rebuilding
NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. However, third parties such as the government and your internet service provider (ISP) can see that you are using Tor. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. Note that engaging with the content in any way is not only distressing but could also put you at legal risk. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark web sites offer malware as a tool for cyberattacks.
Method II – VPN Over Tor
With over 20 years of experience in cybersecurity and marketing, Ben has held leadership roles at companies like Check Point, Cognyte, Cylus, and Ionix. “Understand that the web as we know it today is privacy-hostile and that nothing is foolproof, do research, support organisations and projects — like Tor Project, i2p, and Open Privacy — that are building and maintaining tools that make enforcing your consent easier.” It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult.

Originally created by the US military to enable secure and anonymous communication, this hidden layer of the Internet has since evolved into a complex digital underground. To counter this, dark web monitoring has become essential to detect these threats and safeguard digital privacy. From information security threats like identity theft and malware to scams and surveillance, navigating the dark web without caution can lead to real dangers. Are you thinking of buying drugs off the darknet?
Step 1: Use A Secure Device
The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis. “The big win of Tor for me is access — with a sprinkling of anonymity, to be sure — but that I can be stuck behind some hotel firewall, in some airport or restaurant lounge, or in a sketchy cafe is a sketchy country,” Muffett says. To review security settings, click on the onion logo in the top left and select “Security Settings”, which will bring up a slider offering a choice of the default of standard, or safer and safest.
Tor over VPN also doesn’t protect users from malicious Tor exit nodes. You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network. Your ISP only sees the encrypted VPN traffic and won’t know you’re on Tor.
For its part, Mullvad says that it would “cease operation of our service” if forced by legal means to spy on users. Apps are independently audited for security and are available for Windows, macOS, Linux, iOS, and Android. The former protects traffic using AES-256-GCM encryption and 4096-bit RSA certificates with SHA512 for server authentication. Mullvad is one of the few providers that offer the VPN Over Tor configuration to access the dark web.
Although the underground internet world is rife with everything bad, it also hosts positive elements. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). We’re a nonprofit organization and rely on supporters like you to help us keep Tor robust and secure for millions of people worldwide. Tor Browser already comes with HTTPS-Only mode, NoScript, and other patches to protect your privacy and security.