Archetyp is one of only 5 markets on Dread’s Darknet Markets Superlist. These services break the link between a user’s initial funds and the final payment received by a vendor, which is a fundamental requirement for maintaining privacy. This infrastructure extends beyond the marketplace itself, creating a self-sustaining environment for anonymous commerce.
Torrez Market
- Some health professionals such as “DoctorX” provide information, advice and drug-testing services on the darknet.
- At the end of August, the leading marketplace Agora announced its imminent temporary closure after reporting suspicious activity on their server, suspecting some kind of deanonymization bug in Tor.
- The combination of Tor, encryption, and anonymous payments ensures transactions remain confidential.
- These platforms also employ escrow systems and vendor ratings, which significantly reduce the risk of fraud and ensure that transactions are completed smoothly.
- If you are going by amount of vendors, Archetyp is slightly ahead of Incognito Market at #1.
Vice City offers a user-friendly platform with strong escrow. It reduces fraud by 25%—Alphabay secures $20M monthly with it. Use trusted directories or PGP-signed mirrors—30% of 2025 links are scams. Latest updates from the darknet trading world as of February 2025—key shifts and developments.
What’s The Benefit Of Escrow Security?
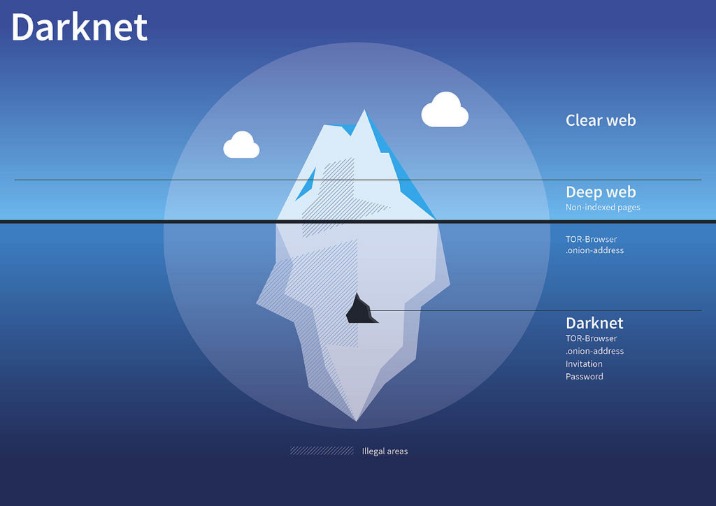
With that said, legitimate websites also exist on the dark web. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. The dark web, or the darknet, is a small subset of the deep web. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
The Top 7 Dark Web Marketplaces In 2025
Darknet market lists help users navigate the best darknet markets, while updated URLs maintain access to dark web drug marketplaces. The evolution of darknet markets in 2025 has significantly enhanced the security and reliability of drug trade, offering users a streamlined and efficient platform for transactions. In 2025, darknet markets have significantly evolved, offering users secure and reliable platforms for drug trade. In 2025, darknet markets have become highly sophisticated platforms for secure and reliable drug trade, offering users unparalleled privacy and efficiency. In 2025, darknet markets have become the preferred platforms for secure and reliable drug trade, offering users unparalleled privacy and efficiency.
Federal investigators traced Silk Road’s funds on the blockchain, linking them to Ross Ulbricht the Dread Pirate Roberts. Its fall began with a tip to U.S. agents and clever bitcoin tracking. It marketed itself as a black market bazaar and sold everything from marijuana to heroin, plus hacking tools and counterfeit IDs. The dark web is not as dark as you think, warns Europol law enforcement uses specialized techniques to unmask hidden transactions.

Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. It has built a reputation for being a reliable source of stolen credit card data and PII. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.
Top 7 Dark Web Marketplaces
Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you.
Emerging Darknet Marketplaces Of 2025 Anatomy Tactics & Trends
- These addresses are essential for establishing a direct and encrypted connection to the marketplace’s server.
- This environment facilitates direct access to a wide range of goods, with platforms like the Nexus darknet market establishing themselves as reliable hubs for commerce.
- This permanence facilitates trust and streamlines the process of conducting secure transactions using bitcoin and other cryptocurrencies, which are integral to the system’s economy.
- This in turn led to political pressure from Senator Chuck Schumer on the US DEA and Department of Justice to shut it down, which they finally did in October 2013 after a lengthy investigation.
- In August 2021, AlphaBay was relaunched after the return of one of the original security administrators DeSnake.
By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers. This encryption makes attribution and tracking more difficult for authorities and cybersecurity professionals. Platforms like Nexus and Abacus dominate due to their encrypted links, reliable escrow systems, and verified vendor networks. The focus remains on seamless transactions, with Bitcoin and Monero payments processed faster through optimized escrow services.

Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero. At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions. Privacy-focused operators are shifting to Monero due to its default anonymity, compared to Bitcoin’s transparent ledger Darknet markets see BTC inflow drop to $2B. Darknet marketplaces remain central to illicit trade in 2025, with evolving business models, payment systems, and law enforcement responses.
Security Blogs
Both defendants further admitted to distributing fentanyl-laced pills to two additional victims, both of whom suffered fatal drug overdoses shortly after they received the pills from Ta and Srinivasan. Srinivasan received virtual currency as payment for the drugs and then routed that virtual currency through cryptocurrency exchanges. Srinivasan also used the encrypted messaging application Wickr to communicate with and sell drugs to customers.

Just visiting these sites can attract attention from law enforcement, especially if you interact with known vendors or download suspicious content. Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn’t foolproof. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Such markets are typically accessible through the Tor network, which anonymizes traffic by routing it through multiple relays and encrypting each layer.

The selection of a darknet marketplace is a critical decision that directly impacts transaction security and product quality. These dark web marketplaces maintain extensive lists of available products through multiple darknet market urls. Entering a leading darknet market in 2025 is a streamlined procedure designed for user convenience and security. This combination of organized information, verifiable vendor reputations, and secure transactions establishes a framework for reliable procurement within the darknet ecosystem. The Tor browser is essential for accessing these .onion sites, as it routes internet traffic through a global volunteer-run overlay network, concealing a user’s IP address and location.

One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. Some were taken down by law enforcement, others just vanished overnight with users’ money. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.